The default WorkerRolePolicy permissions for nodes in Container Service for Kubernetes (ACK) managed clusters are broad. To strengthen security isolation for managed cluster nodes in multi-tenant scenarios, ACK has converged the permissions attached to the RAM roles of managed cluster nodes.
Role authorization
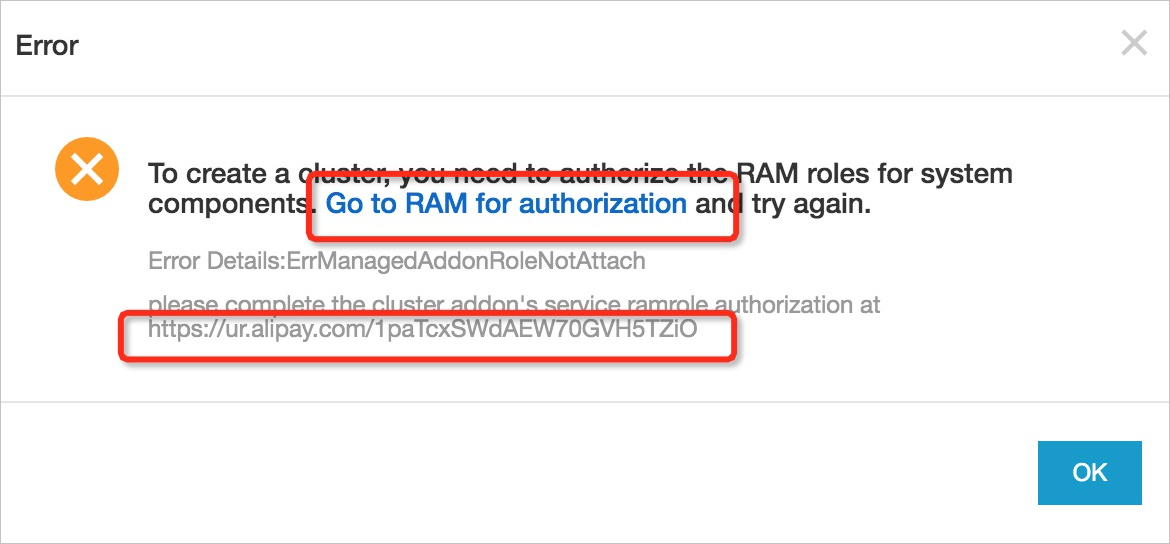
After convergence, the original RAM role permissions no longer include policies used by cluster system add-on components. Instead, ACK assigns dedicated system roles to each add-on component. When you create a managed cluster in the ACK console after this change, the system prompts you to authorize these system roles. Use your Alibaba Cloud account or a RAM user with AliyunRAMFullAccess or AdministratorAccess permissions. Click Go to RAM console.
Note If you use OpenAPI to create a cluster, use the authorization link to authorize.
At the bottom of the batch authorization page, click Confirm Authorization Policy. Then sign in again to the Container Service Management Console to create your cluster.
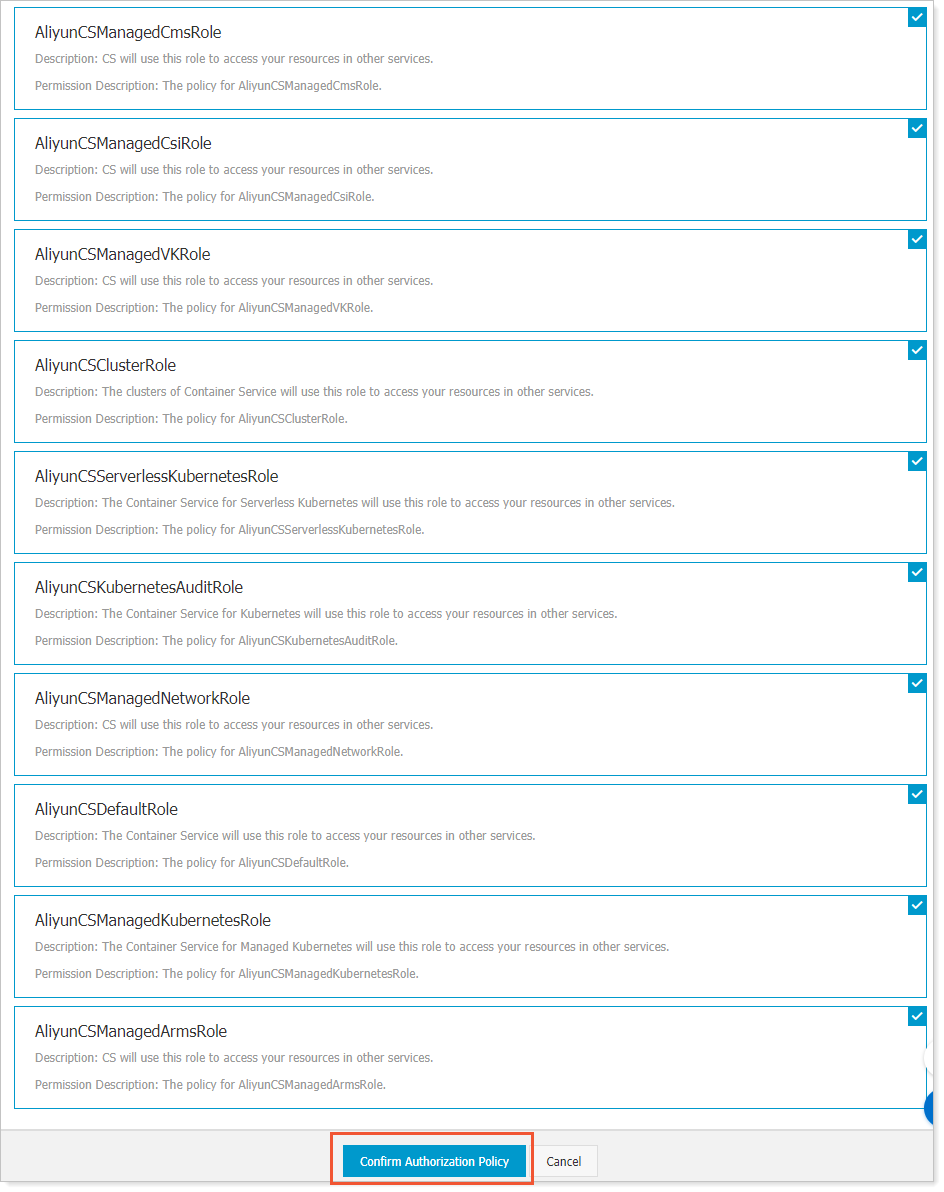
This batch authorization grants the following system roles, which support OpenAPI calls from cluster add-on components:
- AliyunCSManagedLogRole
- AliyunCSManagedCmsRole
- AliyunCSManagedCsiRole
- AliyunCSManagedVKRole
- AliyunCSManagedNetworkRole
- AliyunCSManagedArmsRole
The converged default WorkerRole RAM policy is defined as follows.
{
"Version": "1",
"Statement": [{
"Action": [
"ecs:DescribeInstanceAttribute",
"ecs:DescribeInstanceTypesNew",
"ecs:DescribeInstances"
],
"Resource": [
"*"
],
"Effect": "Allow"
},
{
"Action": [
"log:GetProject",
"log:GetLogStore",
"log:GetConfig",
"log:GetMachineGroup",
"log:GetAppliedMachineGroups",
"log:GetAppliedConfigs",
"log:GetIndex",
"log:GetSavedSearch",
"log:GetDashboard",
"log:GetJob"
],
"Resource": [
"*"
],
"Effect": "Allow"
},
{
"Action": [
"cr:GetAuthorizationToken",
"cr:ListInstanceEndpoint",
"cr:PullRepository"
],
"Resource": [
"*"
],
"Effect": "Allow"
}
]
}