Port forwarding rules route non-website traffic—such as traffic from game clients or custom-protocol applications—through Anti-DDoS Pro or Anti-DDoS Premium for scrubbing before it reaches your origin server. This topic describes how to add, modify, and delete port forwarding rules for non-website services.
Prerequisites
Before you begin, ensure that you have:
An Anti-DDoS Proxy (Chinese Mainland) or Anti-DDoS Proxy (Outside Chinese Mainland) instance. See Purchase an Anti-DDoS Pro or Anti-DDoS Premium instance
Usage notes
Batch configuration is available only for instances in the Chinese mainland.
Application-layer Protection is available only for instances in the Chinese mainland.
After all Anti-DDoS Proxy instances under your account are released, the system automatically clears all associated domain and port forwarding rules after 30 days. The countdown starts from the release of the last instance.
UDP port blocking: When you purchase an instance with the Enhanced Function Plan, ports commonly targeted by UDP reflection attacks are automatically blocked after you configure UDP port forwarding rules. This typically does not affect your services. If your services use one of these blocked ports, unblock it manually. See Set up UDP reflection attack mitigation.
NoteCustom UDP reflection attack mitigation settings take precedence over the default blocking behavior.
Add a port forwarding rule
Add a single rule
Log on to the Anti-DDoS Proxy console.Anti-DDoS Proxy console
In the top navigation bar, select the region of your instance:
Anti-DDoS Proxy (Chinese Mainland): Select Chinese Mainland.
Anti-DDoS Proxy (Outside Chinese Mainland): Select Outside Chinese Mainland.
In the left-side navigation pane, choose Provisioning > Port Config.
Select an instance and click Create Port Forwarding Rule.
Configure the parameters in the following table, then click Confirm.
NoteRules marked with the
 icon next to Forwarding Protocol are auto-generated for website services. You cannot edit or delete these rules manually. An auto-generated rule is removed when all website configurations that use it are deleted. For details, see Add a website configuration.
icon next to Forwarding Protocol are auto-generated for website services. You cannot edit or delete these rules manually. An auto-generated rule is removed when all website configurations that use it are deleted. For details, see Add a website configuration.If the website server port is 80, the system auto-generates a TCP rule for forwarding port 80.
If the website server port is 443, the system auto-generates a TCP rule for forwarding port 443.
Parameter Description Forwarding Protocol The protocol used to forward traffic. Valid values: TCP and UDP. ImportantSec-MCA does not support UDP port forwarding.
Forwarding Port The port on your Anti-DDoS instance that receives and forwards traffic. Keep the following in mind: Same port as origin: Set the forwarding port to the same value as the origin server port for easier management. No port 53: Port 53 is not supported, because Anti-DDoS Pro and Anti-DDoS Premium does not allow users to build their own DNS servers for protection. Unique per protocol: Each rule using the same protocol must have a unique forwarding port. Adding a duplicate protocol-and-port combination causes a rule conflict error. No conflicts with auto-generated rules: Avoid using ports already claimed by auto-generated website rules. Origin Server Port The port on your origin server. Back-to-origin Scheduling Algorithm The algorithm used to distribute traffic across multiple origin IP addresses. The default mode is polling and cannot be changed. Application-layer Protection Available only for TCP-based services on instances with the Enhanced Function Plan. Protects against application-layer attacks that use non-HTTP/HTTPS protocols. For more information about attack types, see DDoS attack types that can be mitigated. Configure the following timeout values: Back-to-origin new connection timeout: An integer from 1 to 3 (seconds). If a new connection to the origin is not established within this period, the connection times out. This setting limits the impact of attackers who flood the origin with fake TCP connections without sending valid data. Back-to-origin read/write connection timeout: An integer from 60 to 600 (seconds). Read timeout: How long Anti-DDoS waits for a response from the origin after sending a request. Write timeout: How long Anti-DDoS has to successfully deliver data to the origin. These settings prevent attackers from occupying origin resources by sending or receiving data at an extremely low rate over legitimate connections. Origin IP Address The IP address of your origin server. You can add up to 20 IP addresses, separated by commas (,), to enable automatic load balancing. The origin server can be an Alibaba Cloud service or a third-party service. If it is an Alibaba Cloud service, it must belong to the same Alibaba Cloud account. If it belongs to a different account, contact your account manager.
Add rules in a batch
Batch add is available only for instances in the Chinese mainland.
You cannot enable Application-layer Protection when adding rules in a batch. To enable it, add the rules first, then turn on the switch for the relevant rules in a separate batch operation.
On the Port Config page, click Batch Operations > Add Rule.
In the Add Rule dialog box, enter the rules to add. Each line represents one rule, with the following four fields separated by spaces:
<protocol> <forwarding-port> <origin-server-port> <origin-ip-address>Example:
TCP 8080 8080 203.0.113.1 UDP 9000 9000 203.0.113.2Select the rules to upload, then click Upload.
What to do next
After adding port forwarding rules, complete the following steps to safely route production traffic through your Anti-DDoS instance.
Step 1: Add back-to-origin IP addresses to your origin server's allowlist
Add the back-to-origin IP addresses of Anti-DDoS Pro and Anti-DDoS Premium to an allowlist on your origin server. This prevents security software on the origin from blocking scrubbed traffic forwarded by your instance. See Add back-to-origin IP addresses of Anti-DDoS Pro and Anti-DDoS Premium to an allowlist.
Step 2: Verify the rule configuration on a local machine
Before switching production traffic, verify that the forwarding rules work correctly from a local machine. This step prevents service interruptions caused by misconfigured rules. See Verify that traffic forwarding configurations are effective on a local machine.
Switch traffic to your instance only after verifying that the forwarding rules are working. Switching traffic before verification may interrupt your services.
Step 3: Switch traffic to your Anti-DDoS instance
Replace your service IP address with the exclusive IP address of your Anti-DDoS Pro or Anti-DDoS Premium instance. The exact method depends on your platform.
Domain name as server address: If the server address is a domain name (for example, hard-coded in a game client), update the A record at your DNS provider to point to the exclusive IP address of your instance. See Change a DNS record.
Multiple Anti-DDoS IP addresses with automatic traffic switchover: Add the non-website service using a domain name and update its CNAME record. This associates the service with multiple Anti-DDoS Pro or Anti-DDoS Premium IP addresses and enables automatic traffic switchover between them. See Use a CNAME record to add a non-website service.
More operations
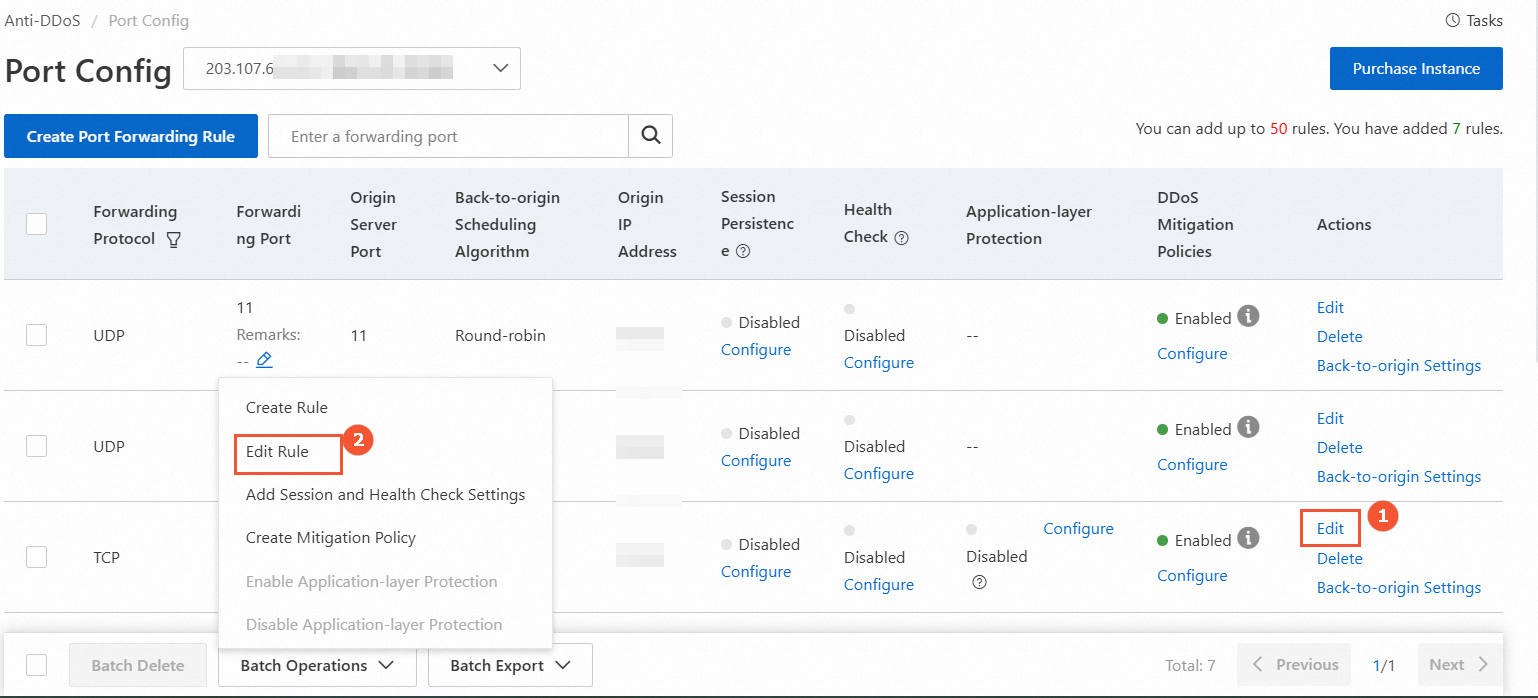
Modify the origin IP address
The following figure shows how to modify the origin IP address for a single rule (①) and for multiple rules in a batch (②).
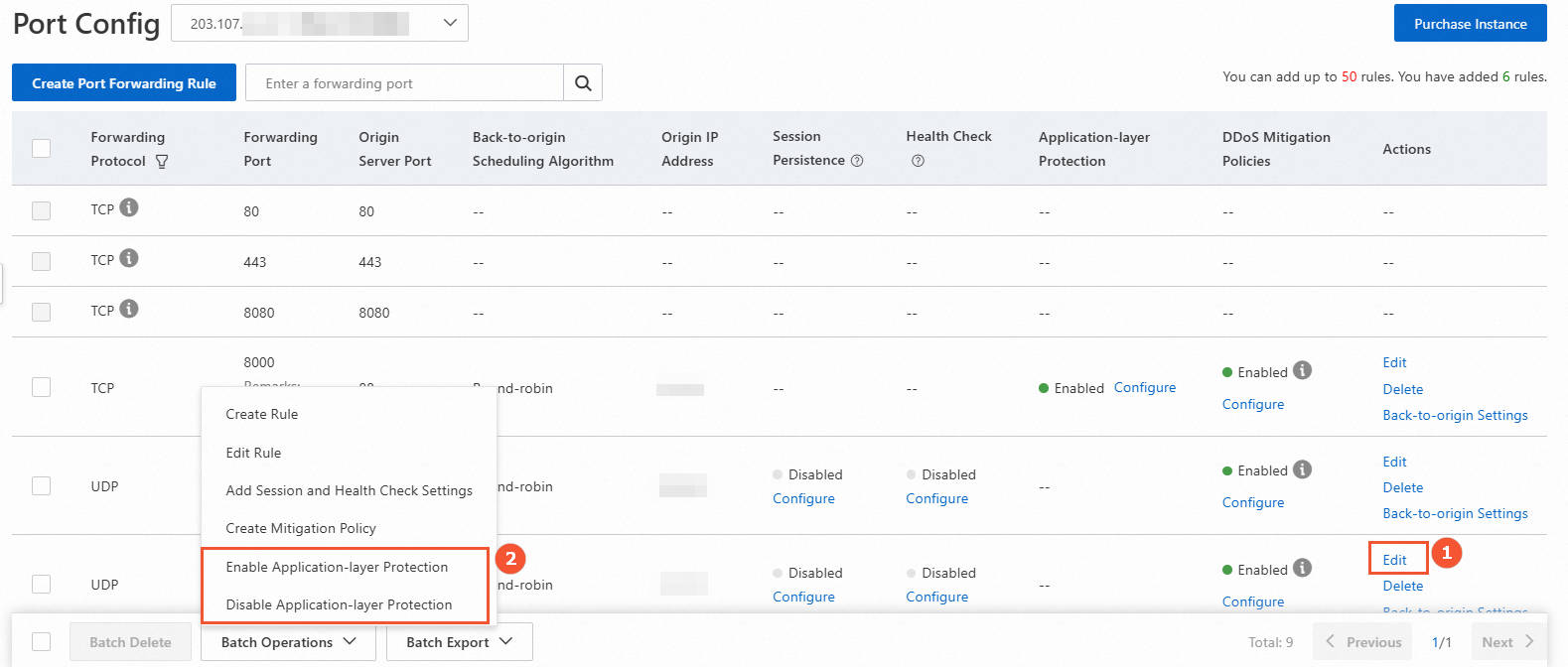
Modify the Application-layer Protection switch
The following figure shows how to modify the switch for a single rule (①) and for multiple rules in a batch (②).
Do not click the Configure button under Application-layer Protection. That button opens the mitigation policies page, not the switch.
When you turn on the switch in a batch, the defaults are:
Back-to-origin new connection timeout: 3 seconds
Back-to-origin read/write connection timeout: 600 seconds
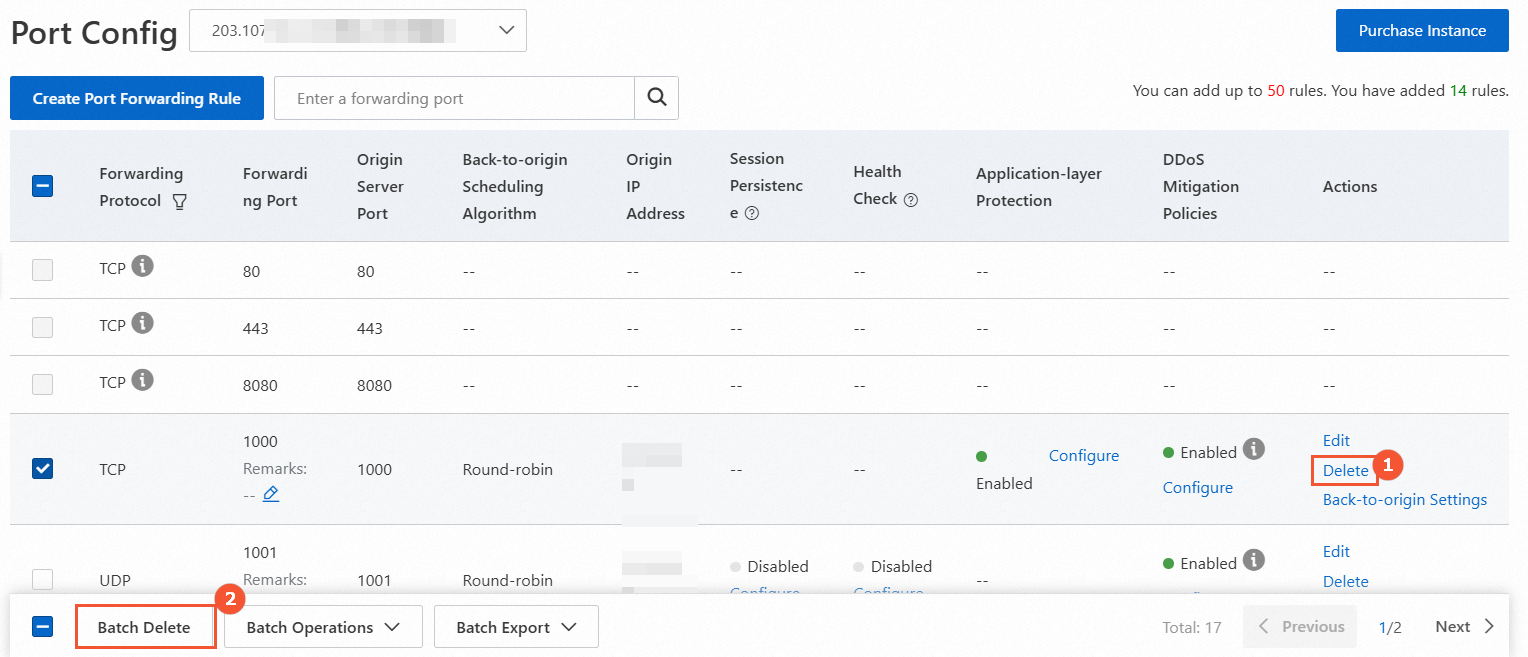
Delete port forwarding rules
Before deleting a rule, redirect your service traffic back to the original service IP address. Deleting the rule before redirecting traffic will interrupt your service.
The following figure shows how to delete a single rule (①) and multiple rules in a batch (②).