By Dassi Orleando, Alibaba Cloud Community Blog author.
CryptPad is a free and open-source collaborative document editor that allows you to share notes, documents, codes, presentations, sheets, and something called Kanban boards, among other things. But the biggest advantage of CryptPad, by far, is that it offers a level of security that you cannot find with other office software provided on the cloud. Let me explain.
In many ways, you could say that Google's suite of online software-particularly Google Docs-offers pretty much the same feature set, but there's a huge difference between the two in terms of security. Google Docs isn't as secure as you may assume. Google could see everything that you're typing in the background if they wanted, too. However, this is absolutely not the case with CryptPad. Everything is encrypted thanks to Blockchain technology, utilizing the encryptions provided by the ChainPad real-time blockchain engine.
In this article, we are going to walk you through how you can install CryptPad on your own server and how you can take advantage and start to use many of its great features.
Entirely cloud-based, CryptPad can be used from its official website at https://cryptpad.fr or as an open-source solution which you can download and then deploy it onto a custom server to be accessible form any modern web browser.
There are many ways to install CryptPad. You can either manually install it from the source code, or you can set it up using Docker, or launch it using Ansible. Below we will go through each of these three methods one by one.
For some further guidance on how to install CryptPad, check out this page. Also, you could consider setting up CryptPad on a server provided by Alibaba Cloud. Alibaba Cloud ECS instances are my choice when it comes to servers in the cloud.
Let's go through the first method. In short, a from-source installation refers to a more technical approach where you'll need to first obtain the source code, install the required utilities or dependencies, and then launch the app itself. Here are the necessary components to have before pursuing the from-source installation:
npm install -g bower command in Npm.)Also, you can get the source code by cloning the GitHub repository with the following command: git clone https://github.com/xwiki-labs/cryptpad. Log in to your local copy of the project and use the npm install or bower install command to install all the required packages/libraries the project depends on.
The config folder is where we should go next in order to provide the required parameters for the project to run seamlessly. An example configuration is there. It's named config.example.js . We can use it as a basis for creating config.js by just making a fully copy: cp config.example.js config.js. The default configurations file is generally good enough for most cases, but you may want to update its content according to your specific need.
Now that we have finished the configurations in the the project's root folder, you only need to start the server with the node server command. Here's how the main page looks once we access the App on port 3000:

You may also need to do a few more additional things if you're deploying CryptPad on the public internet instead of your local computer. Specifically, you'll need to do the following:
foreverjs and systemd to accomplish this. You can reference this guide.You can update your configuration relatively easily. In fact you can do so simply by running the three following commands in your project's root folder. Below are the three commands and a description of what each command does.
git pull: Use to get the most updated version of the source codenpm update: Used to update the npm dependencies, which are saved into node_modules
bower update: Used to update the bower dependencies, saved into bower_components
CryptPad's GitHub repository includes all the necessary tools for building a CryptPad-Docker image. Once you've created a CryptPad container using Docker, we can self-manage the container and let Docker compose handle it for us.
Here are some of the features accessible after you have installed CryptPad using Docker:
.env fileconfig.js to customize folderYou can run CryptPad through running the following commands:
docker build -t xwiki/cryptpaddocker run --restart=always -d --name cryptpad -p 3000:3000 -p 3001:3001 \ -v /var/cryptpad/files:/cryptpad/datastore \ -v /var/cryptpad/customize:/cryptpad/customize -v /var/cryptpad/blob:/cryptpad/blob \ -v /var/cryptpad/blobstage:/cryptpad/blobstage \ -v /var/cryptpad/pins:/cryptpad/pins \ -v /var/cryptpad/tasks:/cryptpad/tasks \ -v /var/cryptpad/block:/cryptpad/block \ xwiki/cryptpadOr by a single command using docker-compose, which will function by copying the instance state in the current directory to ./data folder: docker-compose up –d.
You can check out the full Docker guide here to be able to configure it better and set up the persistence in a different way than the default plus managing the SSL proxy.
For CryptPad to work with Ansible, you will need to use role variables to set up CryptPad. Role variable are responsible for the installation and running of CryptPad on port 30000. The role variables are as follows:
## Role variables
cryptpad_required_packages:
- nodejs
- git
cryptpad_repository: "https://github.com/xwiki-labs/cryptpad.git"
cryptpad_repository_key_file: ""
cryptpad_repository_version: "master"
cryptpad_user: "cryptpad"
cryptpad_group: "{{ cryptpad_user }}"
cryptpad_home: "/home/cryptpad"
cryptpad_path: "{{ cryptpad_home }}/cryptpad"
cryptpad_update: False
# enable monit service monitoring
cryptpad_monit_enabled: False
## template/config.js variables
cryptpad_http_address: "::"
cryptpad_http_headers_enabled: "True"
cryptpad_content_security_enabled: "True"
cryptpad_pad_content_security_enabled: "True"
cryptpad_http_port: 3000
cryptpad_http_safe_port: 3001
cryptpad_websocket_path: "/cryptpad_websocket"
cryptpad_log_to_stdout: "false"
cryptpad_verbose: "false"
cryptpad_main_pages:
- index
- privacy
- terms
- about
- contact
- what-is-cryptpad
cryptpad_remove_donate_button: "false"
cryptpad_allow_subscriptions: "false"
cryptpad_domain: "i.did.not.read.my.config.myserver.tld"
cryptpad_default_storage_limit: "50 * 1024 * 1024"
cryptpad_admin_email: "i.did.not.read.my.config@cryptpad.fr"
cryptpad_storage: "./storage/file"
cryptpad_file_path: "./datastore/"
cryptpad_pin_path: "./pins"
cryptpad_blob_path: "./blob"
cryptpad_blob_staging_path: "./blobstage"
cryptpad_channel_expiration_ms: 30000
cryptpad_open_file_limit: 2048
cryptpad_rpc: "./rpc.js"
cryptpad_suppress_rpc_errors: "false"
cryptpad_enable_uploads: "true"
cryptpad_max_upload_size: "20 * 1024 * 1024"Now, you'll want to download the latest version of ansible-galaxy, and then run the following command to install the required role properly:
ansible-galaxy install systemli.cryptpadHere's a playbook we can immediately use as example:
- hosts: servers
roles:
- { role: systemli.cryptpad }Note: This Ansible role is licensed under the GNU GPL v3.
Let's note that the current version at the time of writing this article is the 2.22.0 (Wolf), the full releases list is accessible over on GitHub.
Note: CryptPad's source code is hosted on GitHub.
CryptPad is an open-source and secure collaborative editor allowing us to:
Among other features, CryptPad's most important feature is the ability for sharing and collaborating with our peers on your pads. Sharing a document here simply means the ability to retrieve a sharable URL from the "share" option.
Below are some other functions described in detail:
The Rich Text is one of the supported document types you can manage with CryptPad. CryptPad includes fully featured text editor allowing you to create and edit rich text documents.
CryptPad has the following configurations: bold, italic, heading (H6 to H1), font-size, font family, text color, background color, link, anchor, image insertion, Math symbols, table insertion, insert special characters, underline text, strikethrough text, superscript, subscript, insert list (ordered with numbers and unordered with bullets), increase or decrease indent, Block quote, align text (left, right, center and justify).
Here's how it looks like when you step into the editor itself:
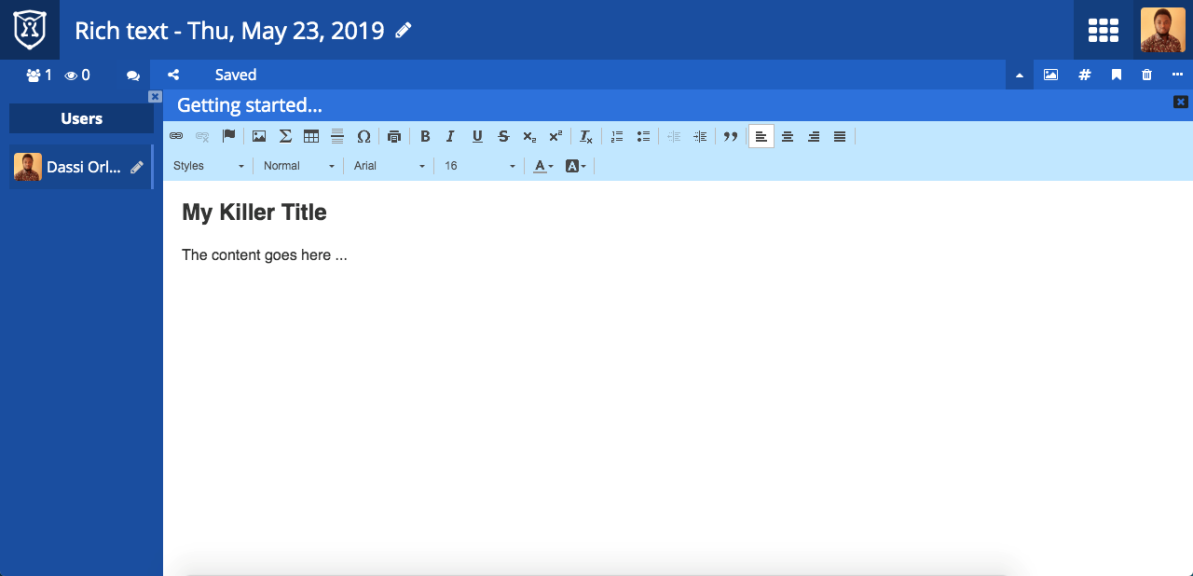
Note: once written, there is the ability to export your Rich Texts to HTML or even print it to have the pdf version.
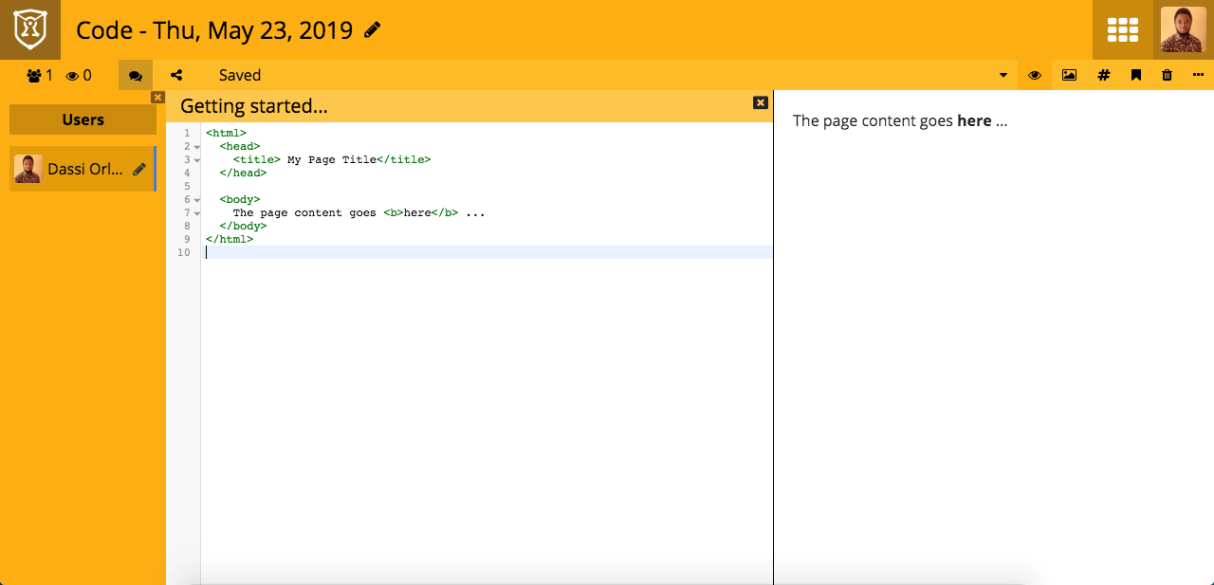
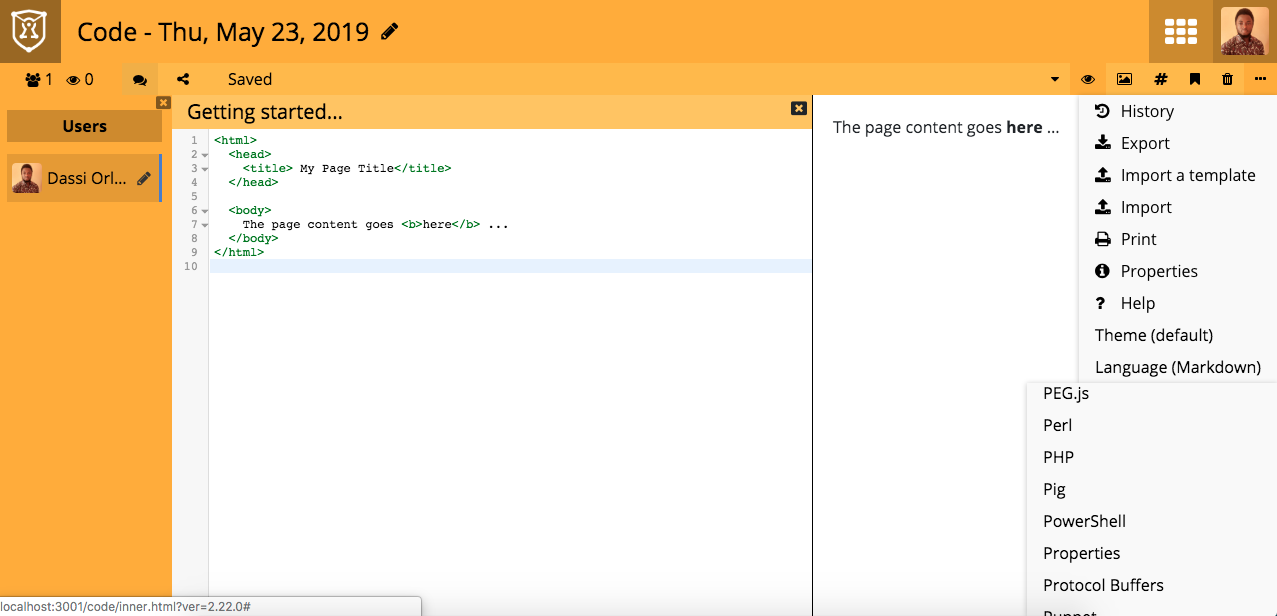
The code editor allows you to write syntax in several different languages, including the following languages: Java, C, Markdown, Pascal, PHP, Perl, Python, Q, R, Ruby, Rust, SQL, TOML, XML, YAML, Visual Basic, SPARQL, CSS.
The syntax you're writing will be highlighted on the left side or the right side depending on the language you are entering.
Here's the screenshot showing the way we're currently writing HTML:
To change the editor language syntax, you can just click on the top right option menu, and then click on Language and pick a different one:
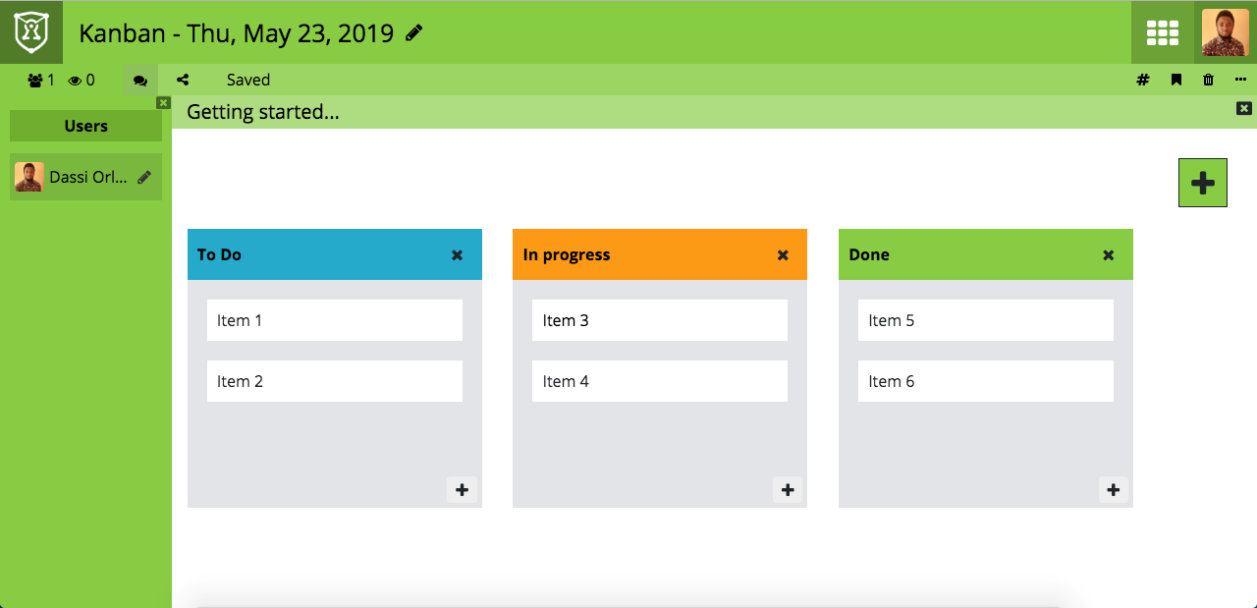
The Kanban area helps us to better manage our project in term of tasks status and progress, the current version is minimalist but the core idea is there:
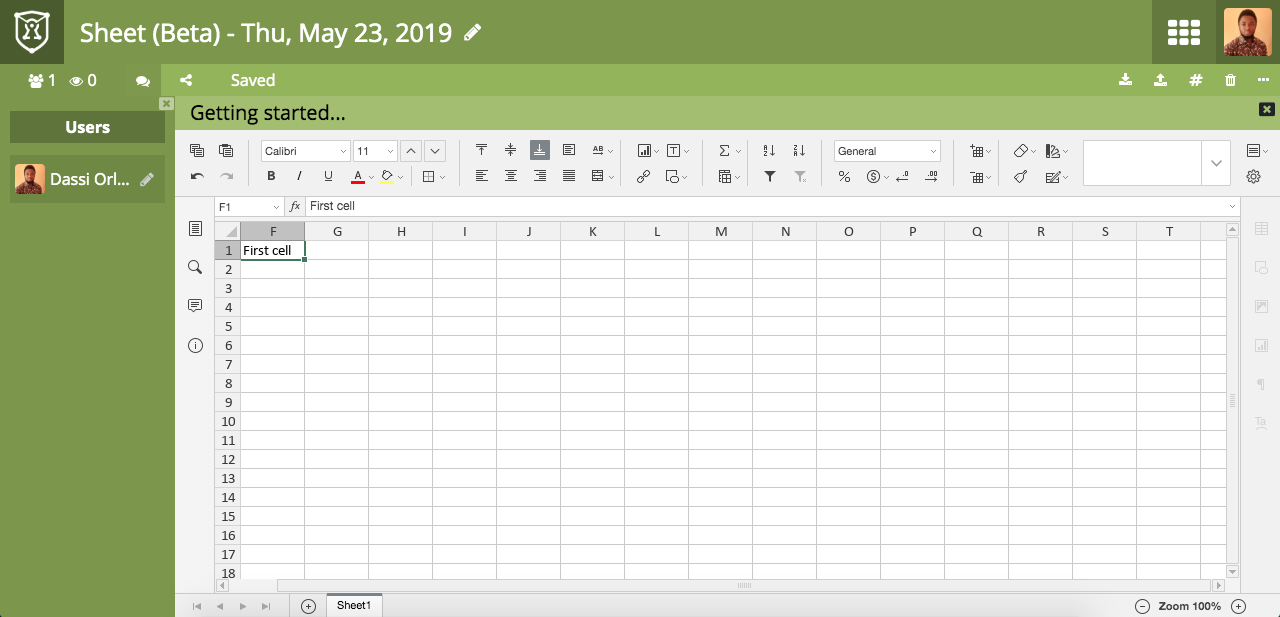
The creating sheets function is one of the most promising feature of CryptPad, but it still in beta version for testing and improvements. In the image above you can have a look at how it's looking like:
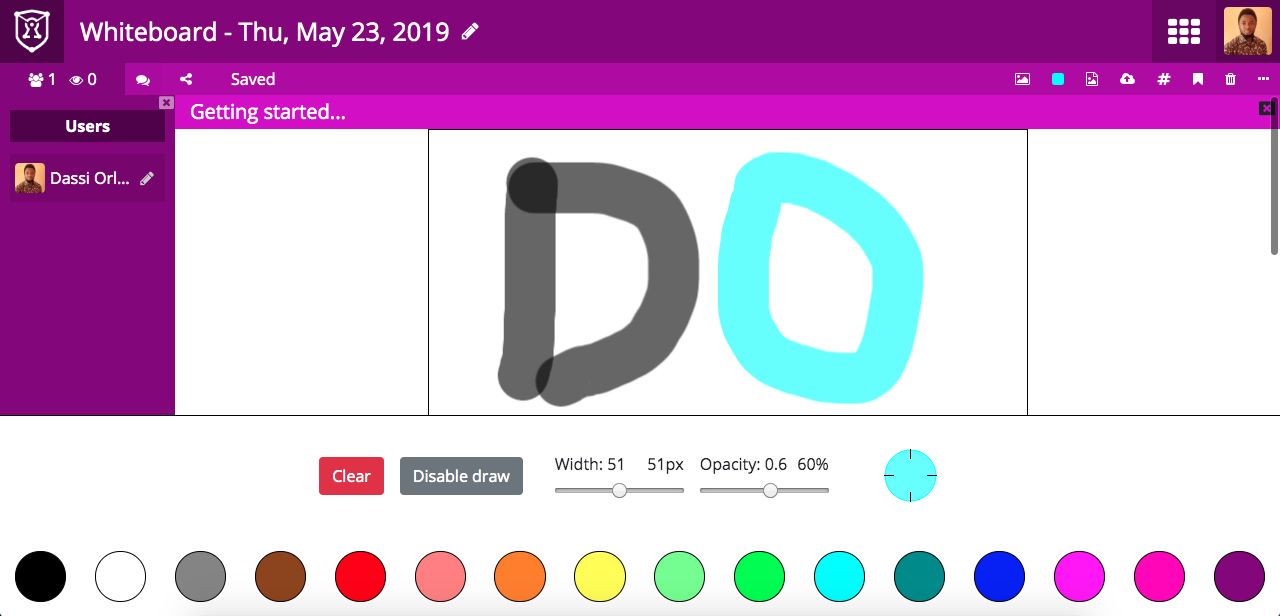
The Whiteboard function of CryptPad is simply an interface feature that allows you to draw on a white screen. It doesn't yet include undo and redo capabilities, but it is very good tool for doodling.
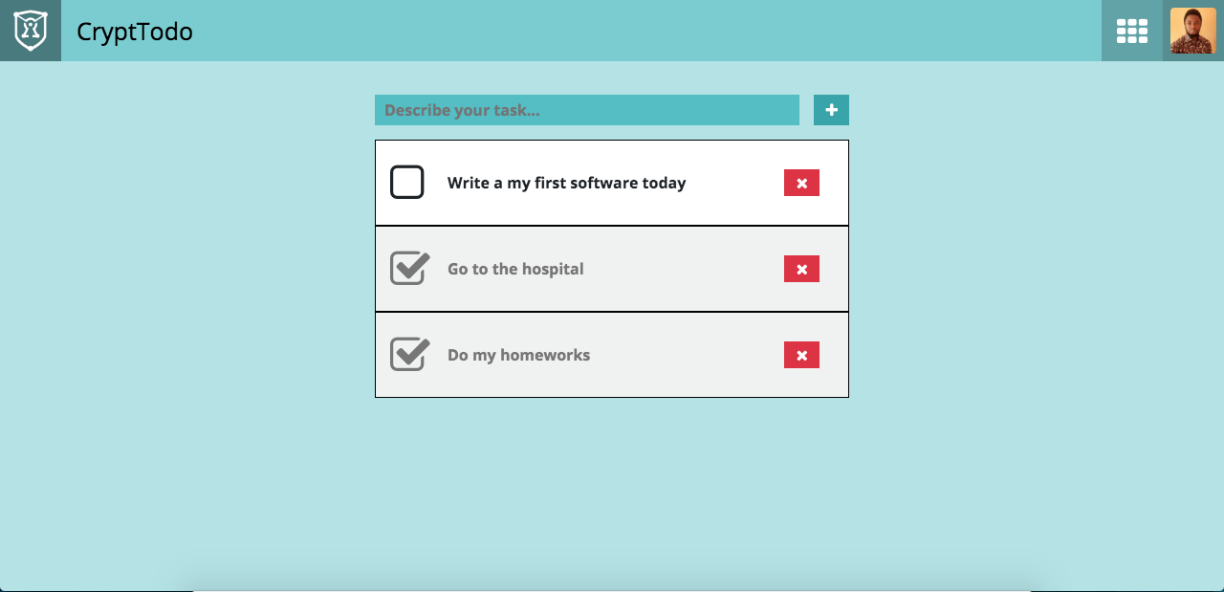
There is also a TODO area of CryptPad for those who are interested in gathering a MinimaList of things to accomplish soon in term of checklist. This tool is a great productivity tool.
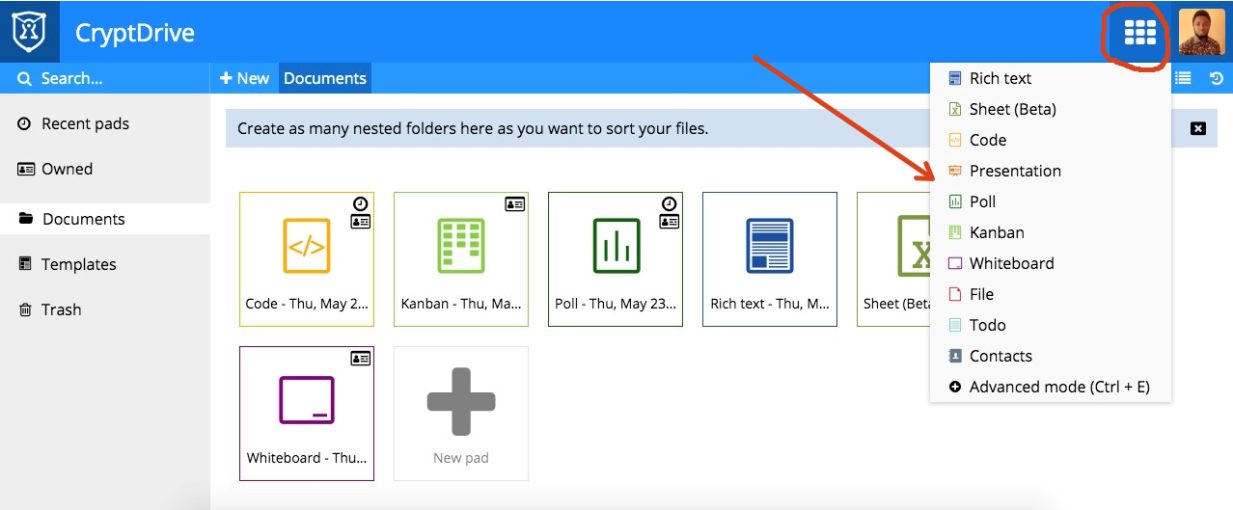
CryptDrive allows you to manage all of your documents regardless the type from one single screen. You can even check your Trash, Templates and the Documents that you own (in contrary to those shared with you by your contacts) as shown in the following screenshot:
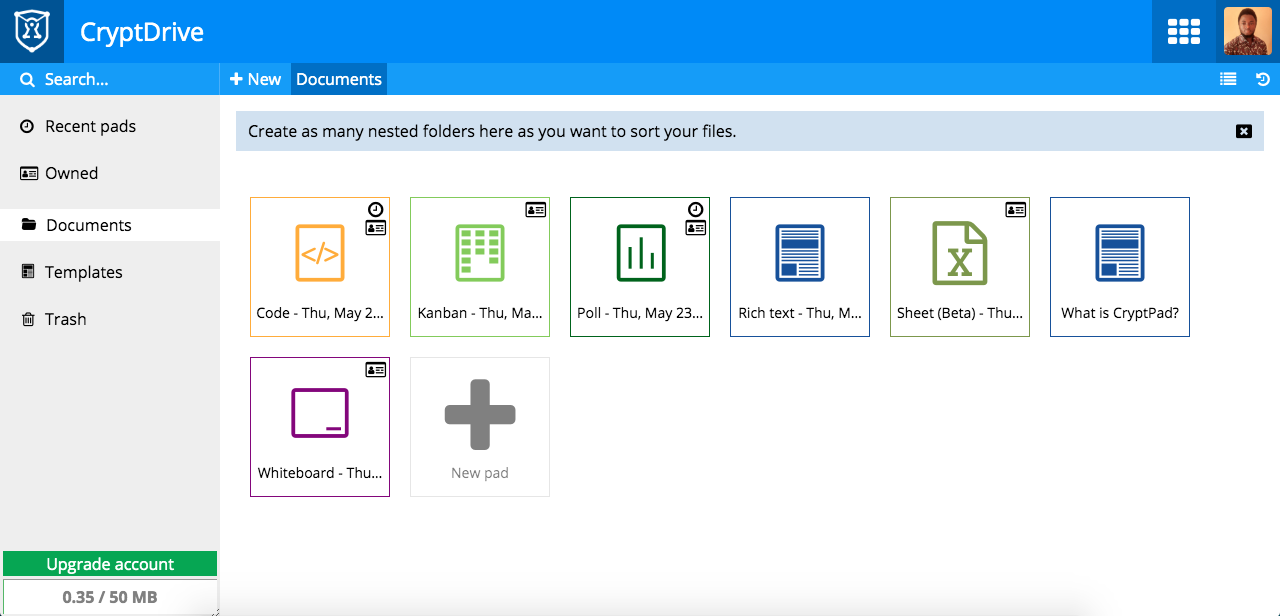
There are many more tools you can access by clicking the dashboard button in the very top right of the screen left to your profile picture, here's the full list as for now:
In this article, we've seen how to install CryptPad, learned some basic ways in which you can use it, and some of its major features. The most important and distinct function of CryptPad is how secure is it and how it can be used to manage your documents in a collaborative workflow among multiple members of a team.
Alibaba Cloud MVPs at the Apsara Conference 2019 - Leading, Sharing, and Changing

2,593 posts | 794 followers
FollowAlibaba Cloud MVP - November 22, 2019
Miles Brown - November 27, 2025
Alibaba Clouder - March 29, 2019
Alibaba Clouder - February 14, 2020
Alibaba Clouder - February 27, 2019
Alibaba Clouder - March 12, 2019

2,593 posts | 794 followers
Follow LedgerDB
LedgerDB
A ledger database that provides powerful data audit capabilities.
Learn More Blockchain as a Service
Blockchain as a Service
BaaS provides an enterprise-level platform service based on leading blockchain technologies, which helps you build a trusted cloud infrastructure.
Learn More Security Center
Security Center
A unified security management system that identifies, analyzes, and notifies you of security threats in real time
Learn More Security Solution
Security Solution
Alibaba Cloud is committed to safeguarding the cloud security for every business.
Learn MoreMore Posts by Alibaba Clouder