Servers are the most desirable zombie for a hacker. The massive amounts of computing resources available in current cloud environments are extremely attractive to hackers. Open-source systems tend to have serious system vulnerabilities, making them easy for hackers to access. Virtual systems also tend to have insufficient security management, making intrusion simple for hackers.
Security researchers have recently discovered that tens of thousands of WordPress stations have been used to implement layer 7 DDoS attacks. Most websites that originate these attacks are hosted on well-known VPS/cloud service providers: Amazon's AWS, DigitalOcean, Google Cloud Platform, Microsoft's Azure, HETZNER, OVH, and Linode.
When thinking about cyber threats, most people first think of zombies, trojans, and worms. Worms are hugely ineffective as they offer low controllability, are highly visible, and easy to eliminate. They likely will not be considered a threat in the near future. However, it is becoming more and more common for hosts to be controlled via trojans, forming a huge zombie network that can be used to carry out DDoS attacks.
Cloud hosts are controlled by hackers for the following three reasons.
Unlike traditional commercial software, open-source software can be developed by programmers and teams around the world. However, making the source code public opens it up to malicious users. This means that open-source systems can be vulnerable to uncontrollable security threats. Therefore, open-source systems are increasingly facing serious system vulnerabilities.
| WordPress | 133 | 5.7% |
| Joomla | 81 | 3.4% |
| Nongyou | 44 | 1.9% |
| YonYou OA | 34 | 1.4% |
| ezOFFICE | 28 | 1.2% |
| Topsec | 19 | 0.8% |
| Kingdee | 19 | 0.8% |
| Shop7z | 19 | 0.8% |
| ruvar OA | 17 | 0.7% |
| 74CMS | 16 | 0.6% |
This is a ranking of component vulnerabilities that we collected from the Internet. We can see more than 100 security vulnerabilities surprisingly exist in WordPress components alone. Therefore, it's not surprising that tens of thousands of WordPress stations have become zombie computers to be abused by hackers.
These are just threats caused by known vulnerabilities. There are a large variety of zero-day vulnerabilities in hackers' hands that have not been exposed, and vulnerabilities existing in the cloud computing environment. The negative effects caused by these vulnerabilities are far more complex than the cloud host becoming a "zombie computer".
Aside from software vulnerabilities, the negative effects on the cloud host caused by trojan and hacker programs cannot be ignored either.
After obtaining control permissions for the cloud host via software vulnerabilities, hackers are able to occupy the host long-term by uploading trojans and other hacker programs.
Moreover, during the process of using the cloud host, it is often necessary to install a number of third-party tools. A lot of download websites, however, offer free tools with hacker programs like backdoors and trojans to make money.
These backdoor and trojan programs are various and difficult to detect. They imitate system or service process, which makes it difficult for you to identify the process in real time.
Aside from vulnerabilities and trojans, if hackers get your login information, they can still do what they want to on the cloud host. Therefore, security problems such as database hits, brute-force cracking, and weak passwords are always threats to the security of the cloud host.
Each time a network is compromised, massive amounts of user information will be lost. By collecting login information from other systems, hackers are able to build a "skeleton key" database that allows them to break into your cloud database through a database hit without triggering a login alert. Moreover, they can use a zombie network to perform brute force attacks on login information over different periods of time.
The biggest risk is that many users do not pay attention to the security of their login information. Rather they log into multiple systems with common, easy to remember usernames and passwords.
First, traditional enterprise level anti-virus software requires a significant amount of CPU and memory to run real-time defense functionality. Eliminating the virus requires a large virus library to analyze the system and file. Traditional servers have powerful processing capability and can sacrifice the resources necessary to run these features. However, for a cloud host, paying for the required resources can be a huge waste.
Second, because cloud systems expand and contract due to current service demands, traditional anti-virus software has difficulty offering consistent coverage at all times.
Moreover, traditional enterprise-level anti-virus software often lacks effective methods of defending against attacks on administrator permissions, including database hits, brute-force cracking, and weak passwords.
So how can we ensure the security of our cloud host? Alibaba Cloud has developed a cloud host security product specifically to address this problem, Server Guard.
Server Guard consists of Agent, Cloud Protection Center, Console, and Server Guard App.
Agents are lightweight processes resident in ECS operating systems. An agent is designed to report ECS security risk data and added security event data based on the security policies configured by the user. Moreover, they respond to commands from the user and Server Guard cloud protection center in order to remove ECS security threats and intercept malicious attacks.
The cloud protection center receives ECS security event and threat data from all the agents in the network and uses a cloud-based multi-threat recognition model to analyze each reported security event. Based on the results of this analysis, the center gives relevant interception and processing commands to the agents.
The console's primary features include ECS resource management, security threat data processing, security policy configuration, and security report display.
With the Server Guard App, you can check on the security status of your ECS instance anytime, anywhere. It also allows you to quickly handle security threats to your ECS.
ZDNet carries out experimental assessment o Server Guard's security protection function based on the current primary threats to the cloud host.
Like most of Alibaba Cloud's security functions, the Server Guard console has been integrated into the Alibaba Cloud console. They are directly invoked via the server security (Server Guard). The security state of cloud hosts can be queried intuitively.
What's more, Server Guard's agent can be installed on both Alibaba Cloud's cloud host, and on non-Alibaba Cloud servers! It is supported by multiple versions of Windows and Linux.
We discover Alibaba Cloud Security and AliHids processes only occupy 0.3% of total CPU capacity (0.6% and 0.9% of total respectively) when installing Server Guard on a single core Linux cloud host with 1G of memory. This operation has no influence on service applications on the cloud host.
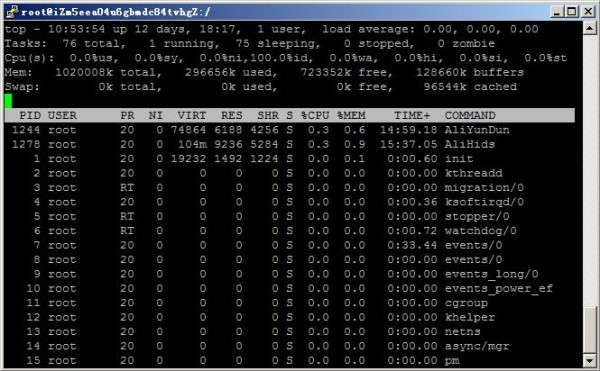
The ability of the console to uniformly manage security significantly reduces the effort required by users when maintaining massive cloud hosts. Lightweight agent avoids wasting resources on cloud hosts.
Do detection results suffer when using a lightweight agent? We have tested the detection capability of Server Guard agent to find out.
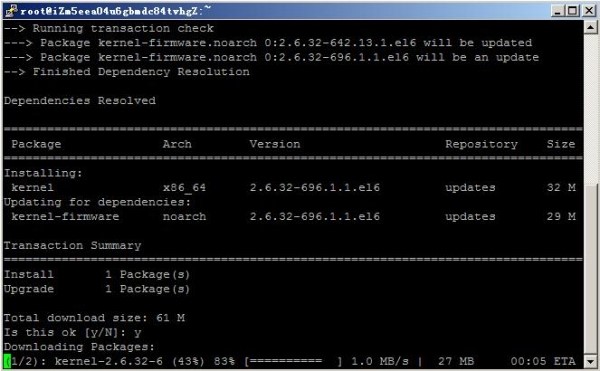
When testing kernel settings through the Server Guard console, we discovered that the mirror used by the cloud host can be changed to a newer mirror to upgrade the kernel, so Server Guard issued a security notice.

The notice disappeared when we upgraded the system kernel.

Inactive patch repairs cannot meet the cloud host's security protection requirements. It is necessary to actively keep an eye on the source to ensure the security of the cloud host. Server Guard provides such a function for tracking the source and cleaning Trojans. With the link between Server Guard Agent and the cloud protection center, trojans in the cloud host can be quickly analyzed and trojan files can be identified and cleaned instantly.
In this test, we uploaded a Webshell script file to be executed via remote command on the cloud host. When the file was uploaded, Server Guard Agent found it immediately and sent out an alert on the control center. The Webshell script file was also instantly isolated so that it could not control the cloud host.
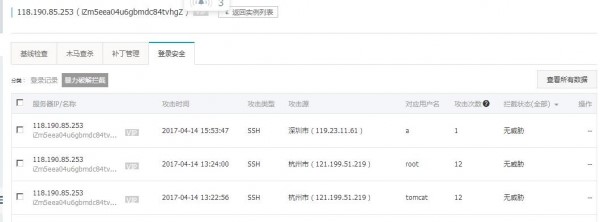
Administrator permissions are critical to the security of the cloud host. Once the user's username and password are leaked or fall victim to a brute-force attack, the cloud host will fall under malicious control and can be considered compromised.
Records and IP address information for user login attempts can be queried on the Alibaba Cloud Server Guard console. If abnormal login information is found, it can then be easily handled in a timely manner.

At the same time, Server Guard performs tremendously well in preventing and recording brute-force cracking attempts.
Server Guard provides logging, prevention, alerts, and threat locating. Alibaba Cloud Server Guard works in tandem with the multiple threat recognition features provided by the cloud protection center, lightweight agent, and intuitive console applications to provide efficient and comprehensive protection. The cloud host is therefore far from an easy target for hackers. In addition, we can cut off and expose the driving force behind the hackers' attacks. As a result, our cloud computing becomes just as secure as traditional systems. With the increasing application of Alibaba Cloud Server Guard, we believe that cloud computing will be much more secure in the near future.

Visit the official page of Alibaba Cloud Server Guard to learn more about this product.
Deploying a Docker Application with Alibaba Cloud Container Service

2,593 posts | 794 followers
FollowPM - C2C_Yuan - June 3, 2024
Alibaba Cloud Community - October 14, 2025
Alibaba Clouder - July 10, 2020
Alibaba Cloud Native Community - February 13, 2025
Nick Patrocky - January 5, 2024
Alibaba Cloud Security - October 30, 2020

2,593 posts | 794 followers
Follow Security Center
Security Center
A unified security management system that identifies, analyzes, and notifies you of security threats in real time
Learn More Web Hosting Solution
Web Hosting Solution
Explore Web Hosting solutions that can power your personal website or empower your online business.
Learn More Security Solution
Security Solution
Alibaba Cloud is committed to safeguarding the cloud security for every business.
Learn More Security Overview
Security Overview
Simple, secure, and intelligent services.
Learn MoreMore Posts by Alibaba Clouder