What Is VPN?
VPN is an abbreviation for Virtual Private Network. As the name suggests it is a virtual network created over the internet/public network between two or more physical networks (or devices) to create an extended private network. This helps users/devices send and receive data as if the users are in one directly connected private network. This means that applications in a VPN can get the same functionalities and be managed in the same manner as in a private network.
Why use VPN?
Every device on the internet has a public IP address which is used to identify and connect to that device either using a browser, command line or any other method. To connect with the device, the data is sent over the internet. This data contains information such as IP addresses etc. which can be intercepted if it is sent over an unsecured network. To protect identity, privacy and data transferred over the internet, VPNs are used to make private connection between the two device/networks.
VPNs can be used in various scenarios. Most commonly, people working remotely from the office wants to access the facilities, network, files etc. from their office using a secure network connection over the internet as if they are working from office. This is also known as a point-to-site VPN connection. Another common case is where a company has many offices in different geographical locations and wants to create a private connection over the internet to connect these offices/networks. This is also known as site-to-site connection. As the connection is happening over the public network, to have data security and safeguard from eavesdropping, authorised access to protect loss of data, it becomes important to have a secure and encrypted private connection between the two networks/devices which is provided by VPN.
For businesses, VPN can be used to connect to their cloud environment and this can help them create an extended network to store, process etc data and information. In individual cases, VPN can be used to hide your public IP address and geolocation as all your requests over the internet is send from a server to which you have created a VPN connection(tunnel).
How does VPN work?
When you use VPN over the internet, it creates a private and encrypted tunnel between the two devices/networks. Now as a VPN it is much harder to do eavesdrop on your data and even if it is intruded upon, as this is data is encrypted, it is close to impossible to get any information from this encrypted data. There are several VPN tunnelling protocols such as PPTP (Point-to-Point Tunnelling Protocol), L2TP (Layer Two Tunnelling Protocol), IPSec (Internet Protocol Security), SSL (Secure Sockets Layer) etc which are used to created VPN tunnels.
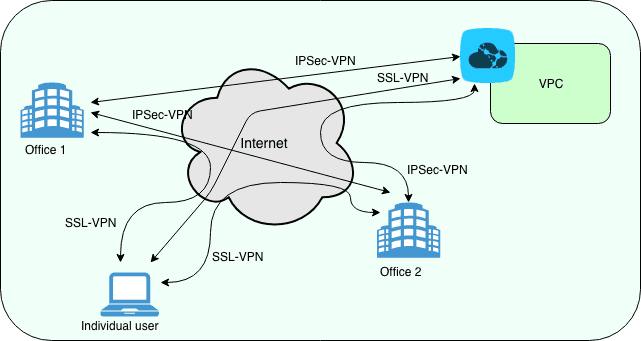
For example, if you use IPSec, which is a suite of protocols, to create a VPN tunnel, then you can use the following scenario. Let’s say you have an office in New York and you want to connect it to another office in London to share information between these office over internet in a private, secure and encrypted manner. Then you can create a VPN tunnel between these two offices and start access device/networks like one single large private network spread over two continents. To achieve this private VPN tunnel, you need to use VPN appliances/devices or VPN Gateways which would work as two ends of the tunnel. However, if you need to connect a remote device to any of these offices, you can just use a point-to-site VPN connection using SSL-VPN.
For IPSec, you follow a two-phase process to create a VPN tunnel. First phase is used to authenticate the IPSec peers and to set up a secure channel between the peers to enable IKE (Internet Key Exchange) exchanges. Once that is done, IKE phase two is used to negotiate IPSec SAs (Security Association) to set up the IPSec tunnel. In simple terms, first phase is used to define how the two peers would exchange the keys (negotiates cryptographic parameters) and the second phase defines how the two peers would encrypt the data (by creating keying material for the IPSec tunnel to use). Once both the phase negotiations are successful you can use this VPN tunnel to communicate between two networks.
Alibaba Cloud provides VPN Gateway services. The VPN Gateway is used to transmit encrypted traffic between Alibaba Cloud VPCs and enterprise data centers, enterprise office networks, or Internet platforms over the Internet. You can use this service to establish reliable and secure connections for data transmission.
Related Articles
-
What is cloud computing
Knowledge Base Team
-
What is CDN
Knowledge Base Team


