Web Application Firewall (WAF) protects your websites and applications by inspecting HTTP/HTTPS traffic, blocking malicious requests before they reach your servers, and forwarding only legitimate traffic. Deploy WAF in under 5 minutes — no hardware, software, or routing changes required.
%E8%8B%B1%E6%96%87-%E9%98%BF%E9%87%8C%E4%BA%91WAF-3-2.mp4
How WAF works
WAF sits between your users and your origin servers. For each incoming request, WAF can:
Allow the request and forward it to your server.
Block the request and return an error response to the client.
Monitor the request — log it and trigger an alert without blocking.
This decision is based on your configured protection rules, threat intelligence signals, and WAF's detection engine. You control which behavior applies to each type of traffic.
Use cases
WAF protects HTTP/HTTPS traffic for web servers deployed on Alibaba Cloud or in any other environment. It is widely adopted across financial services, e-commerce, O2O, Internet+, gaming, government, and insurance.
Core security capabilities
Web application attack protection
OWASP Top 10 protection: Blocks SQL injection, cross-site scripting (XSS), webshell uploads, backdoors, command injection, malformed HTTP requests, cross-site request forgery (CSRF), unauthorized access to core files, and path traversal.
Website cloaking: Hides your origin server's IP address from attackers, preventing them from bypassing WAF to attack your origin directly.
Virtual patching and 0-day protection: Deploys virtual patches for high-risk and 0-day vulnerabilities by rapidly updating protection rules before official security patches are available.
Monitor mode: For new applications, enable monitor mode to log alerts for suspicious traffic without blocking it. Use this to identify and tune out false positives before switching to enforcement.
Deep inspection technology: Fully parses common HTTP data formats — any header field, form data, multipart, JSON, and XML — and decodes URL, JavaScript Unicode, HEX, HTML entity, Java serialization, PHP serialization, Base64, UTF-7, UTF-8, and mixed nested encodings. Whitespace normalization, comment stripping, and special character handling further reduce false positives.
HTTP flood protection
Multi-dimensional rate control: Controls access rates per source IP, verifies visitor identity through redirect challenges and human/bot checks, and identifies attack patterns by correlating response code statistics, URL request distribution, and abnormal Referer and User-Agent headers.
Threat intelligence: Leverages Alibaba Cloud's big data security capabilities to build threat intelligence and trusted access models that quickly distinguish malicious traffic from legitimate users.
Fine-grained access control
Custom protection policies: Configure precise access control rules using common HTTP fields such as IP address, URL, Referer, and User-Agent.
Scenario-based protection: Built-in support for hotlinking prevention and website backend protection scenarios.
Layered defense: Integrates with web attack protection and HTTP flood protection modules to build a multi-layered defense that distinguishes trusted traffic from malicious traffic.
Bot management
Traffic classification reports: Classifies bot traffic as malicious, suspicious, or legitimate, and surfaces traffic trends and risky client details in reports.
Cross-platform coverage: Protects web pages, H5, native apps (iOS, Android, HarmonyOS), and mini-programs (WeChat, Alipay).
End-to-end detection: Applies bot detection throughout the entire request lifecycle using over 100 browser probe features, more than 7,000 client fingerprint types, over 1 million malicious bot threat intelligence signatures, and 6 advanced bot detection algorithms.
API security
Passive traffic analysis: Enable detection with a single click. Supports full-lifecycle API management and monitors sensitive data flows without disrupting your services.
Risk discovery: Detects API vulnerabilities, identifies unauthorized sensitive data exposure and internal API leakage, and provides remediation suggestions.
Threat detection: Identifies API abuse behaviors — such as data scraping and brute-force attacks — through cross-session, bidirectional traffic analysis. Supports response actions directly from WAF.
AI application protection
Prompt injection detection: Identifies adversarial behaviors targeting generative AI systems, including jailbreaking, role-playing inducements, and system prompt manipulation.
Content compliance detection: Checks both request and response content against security and regulatory requirements.
Real-time response: Combines blocking, content replacement, and retraction to stop abnormal behavior and automatically modify response content.
Deployment and architecture
Simple deployment and O&M
Fast activation: Deploy WAF in under 5 minutes with no hardware, software, or routing configuration changes.
Centralized event management: Use security reports and logs to analyze attack events, traffic patterns, and attack scale in one place.
Reliable, scalable architecture
Cluster deployment: A cluster architecture eliminates single points of failure — a single server failure or maintenance event does not affect overall availability.
Load balancing: Multiple built-in load balancing strategies ensure high-performance, high-availability traffic processing.
Auto scaling: Scale the number of servers in your cluster up or down based on actual traffic volume.
Proven expertise and intelligent defense
Over a decade of security experience: Built on more than ten years of cybersecurity practice from within Alibaba Group, with proven capability to support high-concurrency, high-security scenarios such as Taobao, Tmall, and Alipay. A dedicated security team defends against known vulnerabilities including the OWASP Top 10 and continuously responds to newly disclosed security vulnerabilities.
Big data-driven intelligence: Defends against hundreds of millions of attacks daily. WAF leverages a world-leading IP threat intelligence library and an extensive repository of attack signatures across multiple industries and scenarios, enabling deep recognition of mainstream attack patterns, behaviors, and payloads. Attack detection models are continuously improved using big data analytics and machine learning.
For more information, see the Web Application Firewall product page.
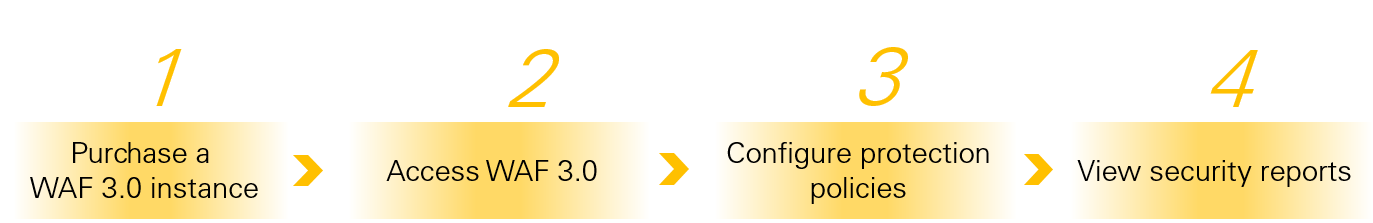
How to use WAF
For more information, see Protect an ECS instance from HTTP flood attacks with WAF.
Relationship between RASP and WAF
Runtime Application Self-Protection (RASP) is a security mechanism integrated within an application that detects and blocks attacks in real time as the application runs. For more information, see Connect to Application Protection.
RASP and WAF are complementary technologies suited for different security scenarios:
RASP is more effective against application-layer threats such as 0-day exploits and attacks within encrypted traffic.
WAF excels at network-layer access control, geo-blocking, HTTP flood protection, and bot attacks.
For comprehensive protection, deploy both RASP and WAF to create a dual-layer security system that combines in-app and perimeter defenses.
Compliance certifications
WAF complies with multiple international standards and certifications, including ISO 9001, ISO 20000, ISO 22301, ISO 27001, ISO 27017, ISO 27018, ISO 27701, ISO 29151, BS 10012, CSA STAR, MLPS Level 3, SOC 1/2/3, C5, HK Financial, OSPAR, and PCI DSS.