HTTP flood attacks use different techniques to overwhelm your web applications. WAF provides multiple protection features, each targeting a specific attack pattern. Use the following table to identify the right defense strategy.
| Attack type | Primary WAF feature | When to use |
|---|---|---|
| Volumetric and high-rate HTTP floods | Rate Limiting (Custom Protection Policy) | High request volume from individual sources |
| Regional and public cloud attacks | Area-based IP Blacklist, Bot Threat Intelligence | Requests from unexpected geographic regions or cloud provider IPs |
| Malformed requests | Custom Protection Policy (ACL) | Abnormal User-Agent, missing headers, or incorrect methods |
| API abuse | Data Risk Control | Low-frequency automated attacks on login, registration, or voting APIs |
| Malicious scans | Scan Protection | High-frequency web attacks, directory traversal, or scanning tools |
| App attacks | App Protection (SDK) | Automated requests targeting native apps |
| Malicious crawlers | Bot Management | Persistent crawling that bypasses other defenses |
Defend against volumetric and high-rate HTTP floods
In volumetric HTTP flood attacks, a compromised server sends requests at a much higher frequency than normal. The most effective defense is to limit the request rate of each source. WAF provides the Rate Limiting function for this purpose. Configure it from the Custom Protection Policy page. For more information, see Create a custom protection policy, you can enable the custom protection policy feature to protect the website. This feature allows you to customize access control list (ACL) rules based on precise match conditions and configure rate limiting. Custom protection policies can be tailored for different scenarios, such as hotlink protection and website backend protection.").
Site-wide rate limiting
The following rule blocks all IP addresses that initiate more than 1,000 requests in a 30-second interval to any path under the domain name. The blocking period lasts for 10 hours. This rule protects small and medium-sized websites.
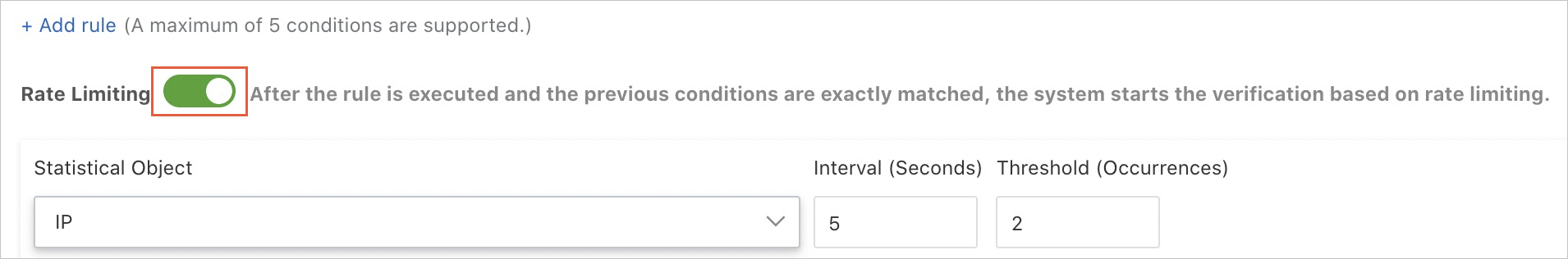
Modify the protected path, adjust the threshold, and select the optimal action to suit your protection requirements.
Credential stuffing protection
To prevent credential stuffing on login endpoints, set Matching field to URL and Matching content to /login.php, and block IP addresses that send more than 20 requests within 60 seconds.
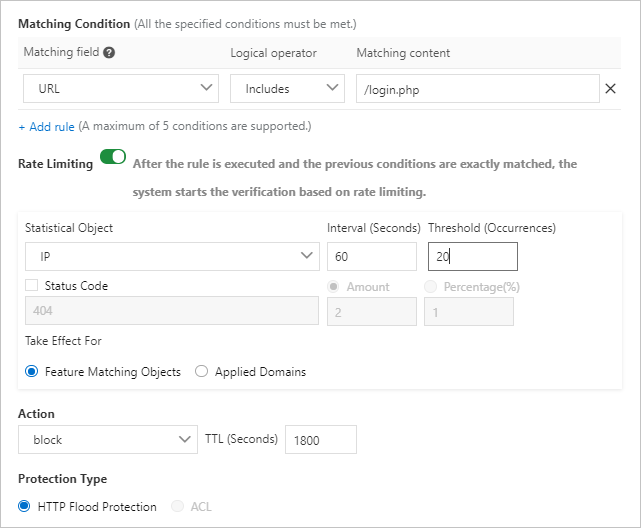
Key constraints
Captcha and Strict Captcha in the Action drop-down list verify whether requests originate from a human or an automation script. Use these two actions to protect common and HTML5 web pages, but not native apps or APIs. For native apps and APIs, set Action to block.
Configure whitelist policies for APIs or IP addresses that may be mistakenly blocked by HTTP flood protection on the Access Control/Throttling tab. For more information, see Configure a whitelist for Access Control/Throttling, you can configure a whitelist for Access Control/Throttling to allow trusted access requests of the website to bypass the detection of HTTP Flood Protection, IP Blacklist, Scan Protection, and Custom Protection Policy. This whitelist is used to allow access requests that are blocked by mistake.").
Do not select Protection-emergency mode for native apps or APIs in the HTTP Flood Protection section.
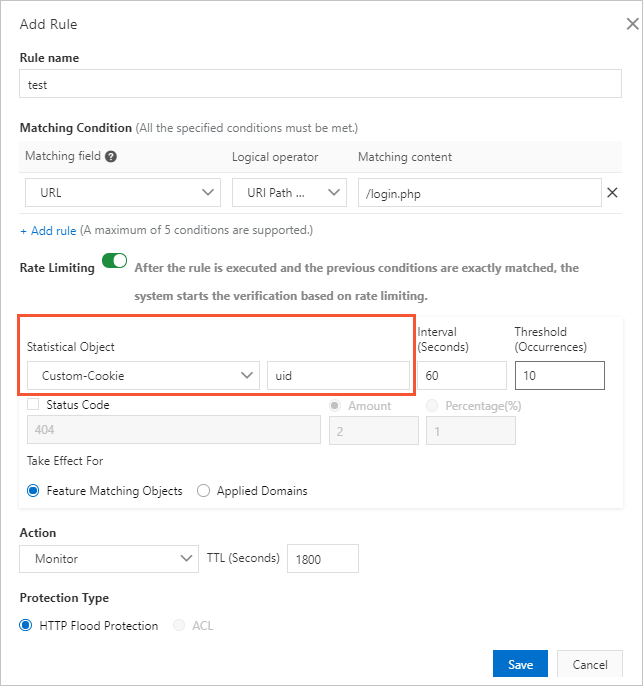
Cookie-based rate limiting (Enterprise edition)
If you have purchased a WAF Enterprise edition instance, configure rate limiting using custom statistical objects, IP addresses, and sessions. Blocking IP addresses may affect NAT. Use cookies or parameters that identify users as statistical objects instead.
In the following example, the request rate is calculated based on the cookie that identifies the user, and Captcha is used to verify the requests. The cookie format is uid=12345.
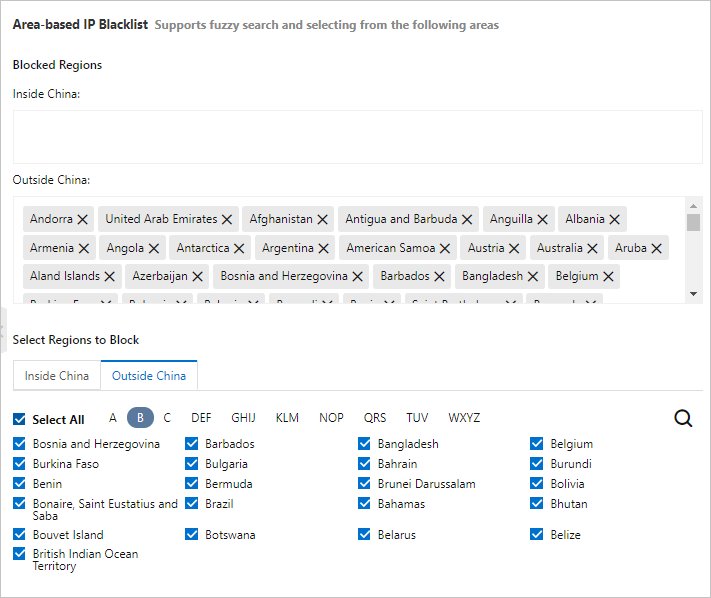
Block attacks from regions outside China and public clouds
A large portion of HTTP flood attacks originate from regions outside China, on-premises data centers, and public clouds.
Geographic blocking
If your website targets users inside China, block requests from regions outside China. WAF provides the Area-based IP Blacklist function for this purpose. For more information, see Configure a blacklist, you can enable the blacklists feature. This feature blocks access requests from specified IP addresses, Classless Inter-Domain Routing (CIDR) blocks, and IP addresses in specified regions. You can specify either an IP address blacklist or a region blacklist based on your requirements.").
Cloud provider IP blocking
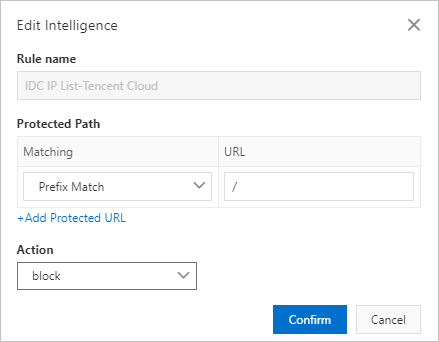
To block crawler IP addresses from common IP libraries, such as the CIDR blocks of Alibaba Cloud, Tencent Cloud, and on-premises data centers, use the Bot Threat Intelligence function on the Bot Management tab.
Note: Many crawlers are deployed on ECS instances. Users do not access your services from the source IP addresses of public clouds or on-premises data centers.
The following example shows a bot threat intelligence rule that blocks accesses from the crawler IP addresses of Tencent Cloud. For more information, see Set a bot threat intelligence rule.
Block malformed requests
Malicious requests in HTTP flood attacks often contain anomalies. Analyze request features and set Protection Type to ACL from the Custom Protection Policy page to block these requests. For more information, see Create a custom protection policy, you can enable the custom protection policy feature to protect the website. This feature allows you to customize access control list (ACL) rules based on precise match conditions and configure rate limiting. Custom protection policies can be tailored for different scenarios, such as hotlink protection and website backend protection.").
Indicators of malformed requests
| Indicator | Description | Example |
|---|---|---|
| Abnormal User-Agent | Characteristics of automation tools, incorrect format, or impossible values | Python, Mozilla///, www.example.com |
| Unusual User-Agent | User-Agent does not match the expected access pattern | A WeChat-targeted HTML5 page accessed by a Windows desktop browser such as Microsoft Internet Explorer 6.0 |
| Abnormal referer | Missing referer or a referer that identifies an illegitimate website | First visits may lack a referer. For redirect-only URLs, filter based on the referer field. |
| Abnormal cookie | Malicious requests typically contain no cookie information | Block requests without cookies for sites that require them |
| Missing HTTP headers | Normal requests contain authorization headers; malicious requests do not | Block requests missing required authorization headers |
| Incorrect request method | An API that normally receives POST requests is flooded with GET requests | Block unexpected GET requests to POST-only endpoints |
Configuration examples
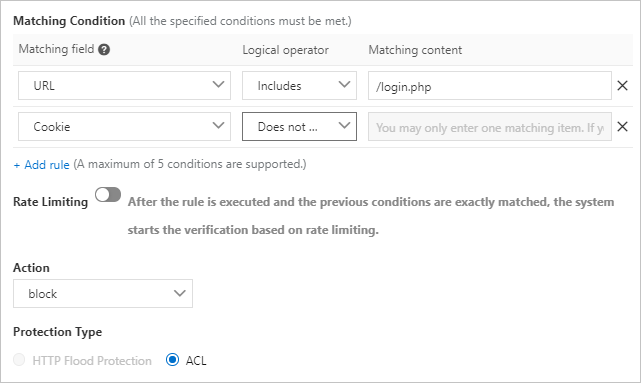
Block requests without cookies:
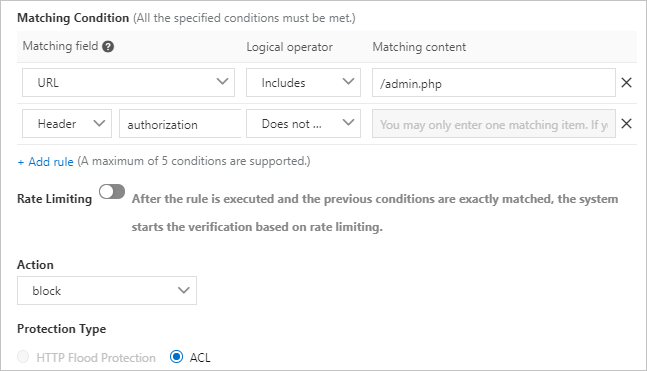
Block requests without authorization headers:
Prevent API abuse
Use the Data Risk Control function to protect important APIs from automated attacks. These APIs include login, registration, voting, and SMS verification endpoints.
Data Risk Control injects a JavaScript snippet into your website and collects information about user behaviors and environment variables to determine whether requests originate from a human or an automation script. It makes decisions based on CAPTCHA rather than request rate or source IP address, making it effective against low-frequency attacks.
Notice: Data Risk Control checks whether requests contain authentication parameters required by normal requests to identify malicious ones. This function is not suitable for environments where JavaScript is not supported, such as APIs and native apps. To prevent false positives, test Data Risk Control in a test environment before enabling it. Alternatively, use the observation mode and contact engineers before enabling the prevention mode.
For more information, see Configure data risk control, you can enable data risk control for the added website. Data risk control is used to protect crucial website services against attacks. These services include registrations, logons, campaigns, and forums. You can customize data risk control rules based on your business requirements.").
Defend against malicious scans
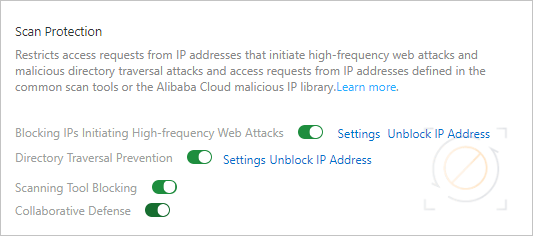
A large number of malicious scans pose a serious threat to server performance. In addition to rate limiting, use the Scan Protection function to strengthen security.
Scan Protection supports the following settings:
| Setting | Description |
|---|---|
| Blocking IPs Initiating High-frequency Web Attacks | Automatically blocks client IP addresses that initiate high-frequency web attacks |
| Directory Traversal Prevention | Automatically blocks client IP addresses that initiate multiple directory traversal attacks in a short period |
| Scanning Tool Blocking | Automatically blocks access requests from IP addresses defined in common scan tools or the Alibaba Cloud malicious IP library |
| Collaborative Defense | Automatically blocks access requests from IP addresses defined in the Alibaba Cloud malicious IP library |
For more information, see Configure scan protection, you can enable the scan protection feature for your website. After the scan protection feature is enabled, access requests from specific IP addresses are automatically blocked. These IP addresses include source IP addresses that initiate high-frequency web attacks and malicious directory traversal attacks, and IP addresses defined in common scanners or the Alibaba Cloud malicious IP library.").
Protect apps with SDK integration
In addition to the preceding measures, you can also use the SDK to enhance protection. After you integrate the SDK with your app, all incoming requests are verified before reaching your server. The device information and request signature are combined to determine whether requests come from legitimate apps. Requests that do not originate from official apps are automatically blocked, so only valid requests are served.
To use the SDK, enable App Protection. For more information, see Configure application protection console after you integrate the Anti-Bot SDK into an application.").
Mitigate malicious crawlers
For informational websites that offer services such as credit reports, apartment rentals, airline tickets, and e-book reading, malicious crawlers can increase bandwidth usage and server workload, and cause data leaks. If the preceding measures cannot prevent malicious crawlers, enable the Bot Management feature for more effective protection.
For more information, see Configure a whitelist for Bot Management, you can configure a whitelist for Bot Management to allow trusted access requests of the website to bypass the detection of Bot Threat Intelligence, Data Risk Control, Intelligent Algorithm, and App Protection. This whitelist is used to allow access requests that are blocked by mistake.").