The SASE security client routes Internet traffic from corporate devices to the nearest SASE service node. Devices without the client installed fall outside zero trust policy coverage. This topic explains how to configure account settings, allowlists, message push notifications, custom storage, and enterprise branding, and how to download, install, and upgrade the security client.
After employees install the SASE security client, you can view the total number of enrolled devices and per-device details in the terminal list. The terminal list also shows which users and devices have not installed the client. For details, see View the terminal list.
After an employee logs on to the security client, all Internet traffic from that device is forwarded through SASE, where it is inspected and managed.
Configure account settings
The Account Settings tab has three sections: enterprise authentication identifier, account expiration time, and account expiration policy.
Log on to the SASE console.
In the left navigation pane, click Settings.
On the Account Settings tab, configure the following: Enterprise Authentication Identifier The enterprise authentication identifier is the credential employees enter when logging on to the SASE security client for the first time. Use a value that is easy for employees to remember, such as your company name. Account Authentication Frequency Specifies how long after a user's last logon the security client can automatically log on when the device starts. When this duration elapses, the logon page appears and the user must re-enter their credentials. Account Authentication Policy Controls what happens when the account session expires:
Option Behavior Priority Immediate authentication The security client logs off immediately. The user must re-enter credentials before continuing. Security Authentication During Network Change The security client stays logged on until the next device wake from sleep or network change. User experience
Configure allowlists
Adding resources to an allowlist removes them from SASE inspection and management. All allowlisted traffic and activities are no longer audited or controlled by SASE policies. Review each entry carefully before adding it.
If you have confirmed that certain internal applications, public websites, outbound files, peripherals, or watermark activities are safe, add them to an allowlist to exclude them from SASE management.
Log on to the SASE console.
In the left navigation pane, click Settings.
On the Whitelist tab, select the allowlist type and configure it.
Private access allowlist
On the Private Access tab, add websites by IP address or domain name:
IP Address Whitelist: Enter one or more IP addresses or IP address ranges.
Domain Name Whitelist: Enter one or more domain names or wildcard domain names.
Click Submit. Corporate users can then access allowlisted internal applications directly, bypassing SASE inspection.
Data protection allowlist
On the Data Protection tab, add entries to one or more of the following allowlist types. Separate multiple entries with a comma (,).
| Allowlist type | What it excludes |
|---|---|
| Outbound File Transfer Whitelist | Specified outbound file transfers |
| Screen Watermark Whitelist | Specified screen watermark activities |
| Application Watermark Whitelist | Specified application watermark activities |
| Print Watermark Whitelist | Specified print watermark activities |
Click Submit. SASE no longer manages or blocks the activities of allowlisted users. If an outbound detection policy is triggered for a user on a storage bucket allowlist, the corresponding files are not stored.
Internet behavior management allowlist
On the Internet Behavior Management tab, add entries to the following fields:
User Whitelist: Specific users whose Internet behavior is excluded from management.
User Group Whitelist: Specific user groups whose Internet behavior is excluded from management.
Exception Domain Name: Domain names accessible without SASE inspection.
Click Submit. SASE no longer manages or blocks Internet activity for allowlisted users, user groups, or access to allowlisted domain names.
Configure message push
Configure message push to receive real-time notifications in your corporate group chat when monitored events occur — such as user logons, device registrations, client uninstallation requests, and requests to use disabled software. After a successful configuration, messages about the end users you follow are automatically pushed to your corporate group through DingTalk, WeCom, or Lark chatbots.
Prerequisites
Before configuring message push in SASE, create a custom chatbot for your messaging platform and obtain the required webhook details:
DingTalk: Requires a webhook URL and webhook key. See Custom DingTalk robots.
WeCom: Requires a webhook URL only. See Custom robots for WeCom groups.
Lark: Requires a webhook URL and webhook key. See Custom Lark robots.
Create a message push template
Log on to the SASE console.
In the left navigation pane, click Settings.
On the Message Push tab, click Create Template.
In the Create Template panel, configure the following:
Webhook URL examples by platform:
DingTalk:
https://oapi.dingtalk.com/robot/send?access_token=****(webhook key example:123456)WeCom:
https://qyapi.weixin.qq.com/cgi-bin/webhook/send?key=90e25f1d-99b5-4496-890d-4d1c6efe3****Lark:
https://open.feishu.cn/open-apis/bot/v2/hook/4c83950f-2335-42ae-a5bd-11a96d6d****(webhook key example:123456)
Supported message types:
Notification of Client Log Report
Notification of Exceeded Registration Quota on Client
Notification of Application for Client Uninstallation
Application for Using Unauthorized Software
Notification of Abnormal Connector
Terminal Alert
Configuration item Description Notification Source Select DingTalk Chatbot, WeCom Chatbot, or Lark Chatbot. Chatbot Configuration Enter the webhook URL and, if required, the webhook key for your selected platform. See the examples below. Message Type Select one or more notification types to receive. Click Connectivity Test. When a success message appears, click OK.
To edit or delete a template later, click Edit or Delete on the Message Push tab.
Deleting a message push template stops all automatic notifications to your corporate group. Proceed with caution.
Configure enterprise elements
SASE supports custom branding for the security client, download page, browser authentication page, and help guide — for both Chinese and English versions.
Log on to the SASE console.
In the left navigation pane, click Settings.
On the Enterprise Elements tab, configure the settings described below.

Custom client elements
Click Custom Client Elements.
On the 中文版设置 and English Client Settings tabs, configure the LOGO, Background Image, Title, and Promotion Text. A preview appears on the right.
Click OK.
Custom elements on client download page
Click Custom Elements on Client Download Page.
On the 中文版设置 and English Client Settings tabs, configure the LOGO, Logo Name, Title, and Description. A preview appears on the right.
Click OK.
Customize browser authentication page elements
Click Customize Browser Authentication Page Elements.
On the 中文版设置 and English Client Settings tabs, configure the LOGO, Background Image, and Title. A preview appears on the right.
Click OK.
Guide
The help guide gives employees quick access to onboarding instructions, tips, or FAQs directly from the security client.
Click Guide.
On the 中文版设置 and English Client Settings tabs, configure the Title, Description, and URL, then click OK.
Log on to the SASE client.
In Settings > Toolbox, the configured help guide is available.
SASE App v4.8.5 or later is required for the help guide feature.

Configure custom storage
Custom storage is available in the Data Protection edition of SASE Internet Access Security.
By default, trace data generated during outbound detection is stored in SASE's built-in cloud storage. To store this data in your own environment, configure custom storage using an Alibaba Cloud Object Storage Service (OSS) bucket or a local MinIO storage system.
Log on to the SASE console.
In the left navigation pane, click Settings.
On the Custom Storage Settings tab, review the built-in storage usage, click the switch icon, then click OK.
In the Data Storage Settings dialog box, configure the following: If you select On-premises MinIO Storage System, note the following:
Encrypt data stored in MinIO to reduce the security risks of plaintext storage.
If the MinIO system cannot connect to the SASE platform, you cannot download original files from the console. Locate the file storage address in the logs and download files directly from your MinIO system.
The Optical Character Recognition (OCR) detection engine runs in the cloud. Image files are uploaded to the cloud for detection, but SASE does not retain your enterprise's outbound image data.
Configuration item Description Custom Storage Type Select Alibaba Cloud OSS or On-premises MinIO Storage System. Bucket The bucket for the storage space. Endpoint The endpoint for the storage space. Both HTTP and HTTPS are supported. Use HTTPS — with HTTP, you may need to adjust browser settings to view screenshot evidence or download source files. AccessKeyid An AccessKey ID with data download permissions. Without download permissions, you cannot retrieve original files from the Sensitive File Detection page in Log Audit. AccessKey Secret The AccessKey secret for the storage space. Maximum Size The maximum size for a single stored file. The limit is 60 MB. Click Test Network Connectivity to verify the connection.
Click Confirm.
After configuration, custom storage is enabled automatically. Data files that trigger an outbound detection policy are stored in your specified storage space.
To disable custom storage, toggle the switch to off. Data files are then stored in SASE's built-in storage. Make sure the built-in storage has enough capacity to prevent data loss.
Manage built-in storage
If built-in storage is running low, expand or clear it:
Activate: Click Activate to go to the SASE purchase page and buy additional file storage capacity.
Clear: Click Clear. In the Clear Logs dialog box, select Clear by Time Range or Clear All, then click OK.
Download the SASE security client
Log on to the SASE console.
In the left navigation pane, click Settings.
On the Download Client tab, download the installation package. Packages are available for PC, Mobile, and Enterprise-specific Version.
Decompress the downloaded package and double-click
setup.exeto install.
After installation completes, the SASE security client icon appears on the user's desktop.
Upgrade the SASE security client
Log on to the SASE console.
In the left navigation pane, click Settings.
On the Client Update tab, select the target operating system.

Select the SASE App version to deploy. In the Actions column, click Download to get the installation package.
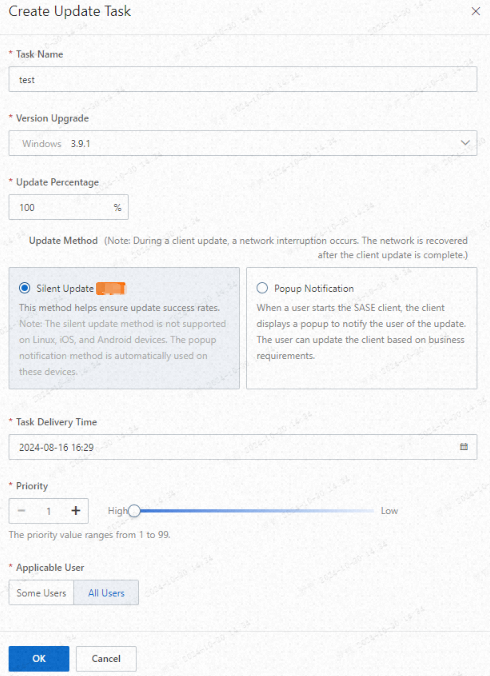
To push the upgrade to employees, click Push Upgrade, configure the upgrade task, then click OK. You can set a custom upgrade percentage. The upgrade rolls out randomly to the specified percentage of devices belonging to users in the selected user group.
Configure traffic redirection
SASE assigns default back-to-origin IP addresses to each Virtual Private Cloud (VPC). These addresses may overlap with your corporate intranet IP range, causing route conflicts or access failures. To avoid this, configure custom proxy IP addresses.
Log on to the SASE console.
In the left navigation pane, click Settings.
On the Traffic Redirection Settings tab, configure proxy IP addresses for each operating system, then click Submit.
Only internal IP addresses can be used as proxy IP addresses.
If corporate intranet applications have firewalls or security control policies, add the SASE back-to-origin IP addresses to those allowlists to prevent traffic from being blocked.