After you enable log collection for a Web Application Firewall (WAF) protected object, use log query to search and analyze log data, generate charts, and create alerts based on query results.
Prerequisites
WAF Log Service is enabled. For details, see Enable or disable log service.
-
You have added your web services to WAF 3.0 as protected objects and protected object groups.
Log delivery is enabled for the WAF protected object. For details, see Manage log delivery status.
Query and analyze logs
-
Log on to the Web Application Firewall 3.0 console. From the top menu bar, select the resource group and region (Chinese Mainland or Outside Chinese Mainland) for the WAF instance.
- In the navigation pane on the left, choose .
-
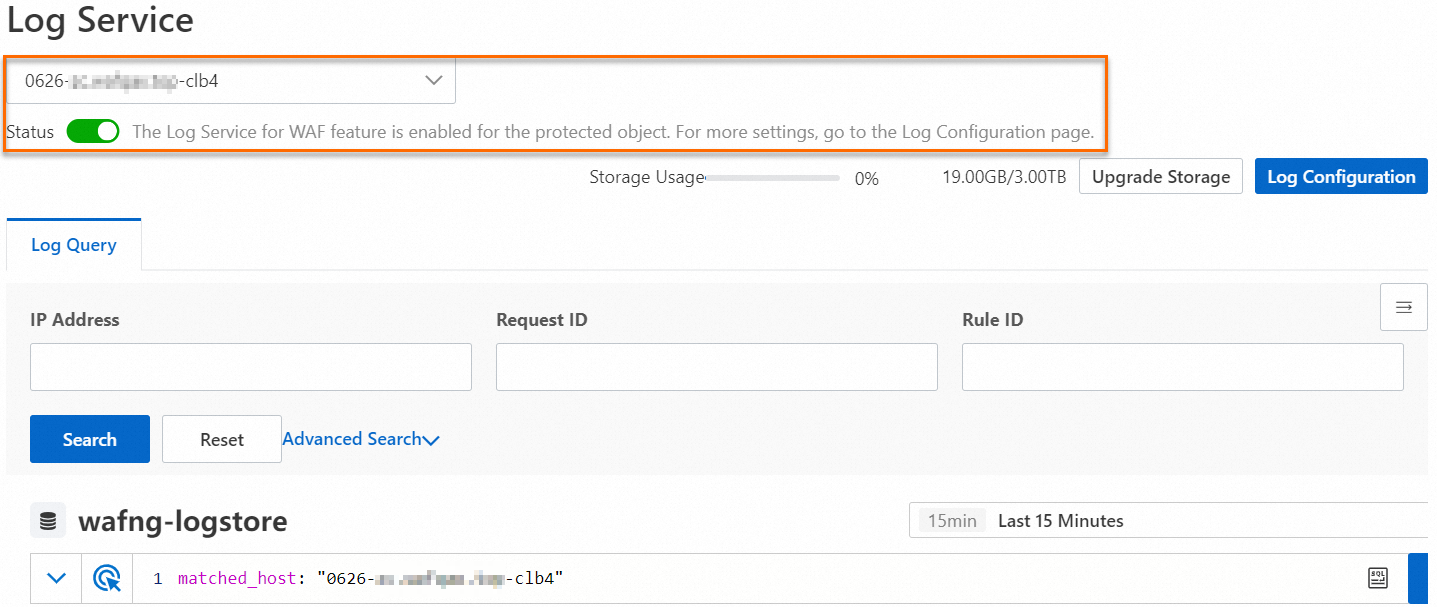
On the Log Service page, select the protected object whose logs you want to query.
ImportantThe protected object must have log collection enabled (the Status toggle must be on). If it isn't enabled, WAF won't collect log data or provide log query and analysis. If log collection isn't enabled for the selected protected object, find it on this page, click the object name, and turn on the Status toggle. Alternatively, go to the Log Configuration page, click the Delivery Settings tab, and use Status of Delivery to Simple Log Service to manage log collection for all protected objects. For details, see Manage log delivery status.
-
On the Log Query tab, use query and analytics statements to search and analyze WAF log data.
Follow these steps:
-
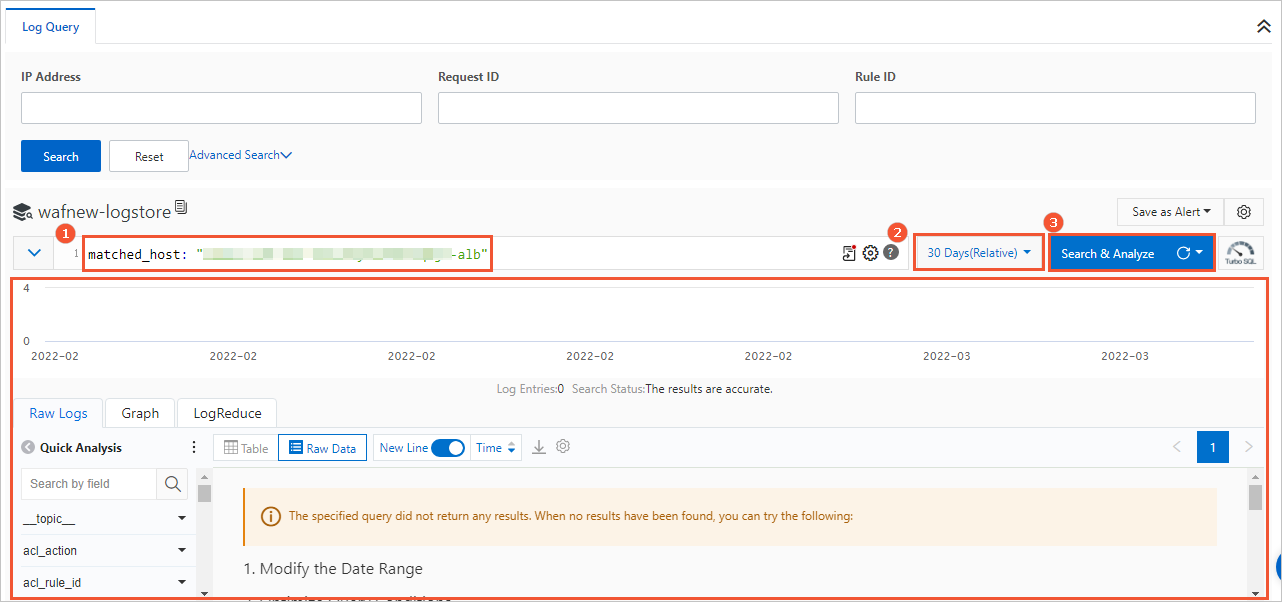
In the statement input box (labeled ①), enter a query statement.
Query statements use the Alibaba Cloud Log Service syntax. For details about this syntax, see Query syntax and functions. Use WAF log data fields as query fields. For a list of supported query fields, see Log fields.
If you're unfamiliar with the log query syntax, use Advanced Search. Expand Advanced Search above the statement input box, configure your search conditions, and click Search. The statement input box automatically generates a query statement that matches your conditions.
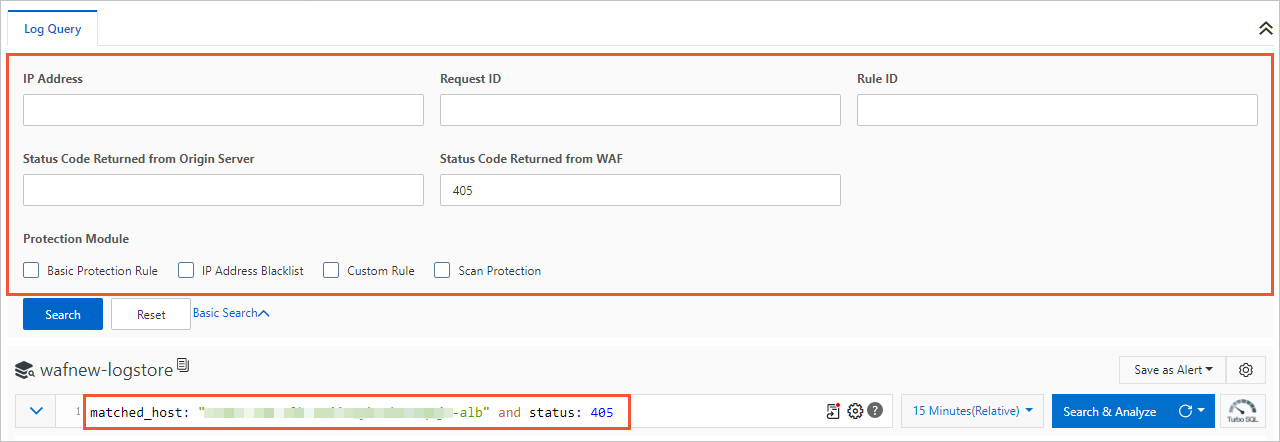 Advanced search supports the following search conditions:
Advanced search supports the following search conditions:Search condition
Description
IP
IP address of the client that sent the request.
Request ID
Unique ID that WAF generates for the client request. WAF includes this ID in block pages and CAPTCHA challenge responses, and you can use it for issue analysis and troubleshooting.
Rule ID
ID of the WAF protection rule that the request matched. Find the rule ID on the Protection Rules page, or get it from the rule-hit records and statistics on the Security Reports page. For more information, see Security reports.
Status Code Returned from Origin Server
HTTP status code that the origin server returned in response to WAF's back-to-origin request.
Status Code Returned from WAF
HTTP status code that WAF returned to the client.
Protection Module
Type of WAF protection module that the request matched. For an overview of WAF protection modules and how to configure protection rules for each module, see Protection configuration overview.
-
To run statistical analysis on query results, append an analytics statement after the query statement in the statement input box (labeled ①). To retrieve only matching log data, skip this step.
Separate the analytics statement from the query statement with a pipe character (
|). Analytics statements use standard SQL 92 syntax. For details, see Overview of log query and analysis. Use the time range selector (labeled ②) to set the time range for the logs you want to query.
-
Click Log Query(labeled ③).
The query and analysis results — WAF log data that matches your query — appear at the bottom of the page. Results include a log distribution histogram, Original Request Header, charts, and log clustering. From the results, run quick analysis, generate charts, and set up alerts. For details, see Description of the Query/Analysis page.
-
Description of the Query/Analysis page
Page overview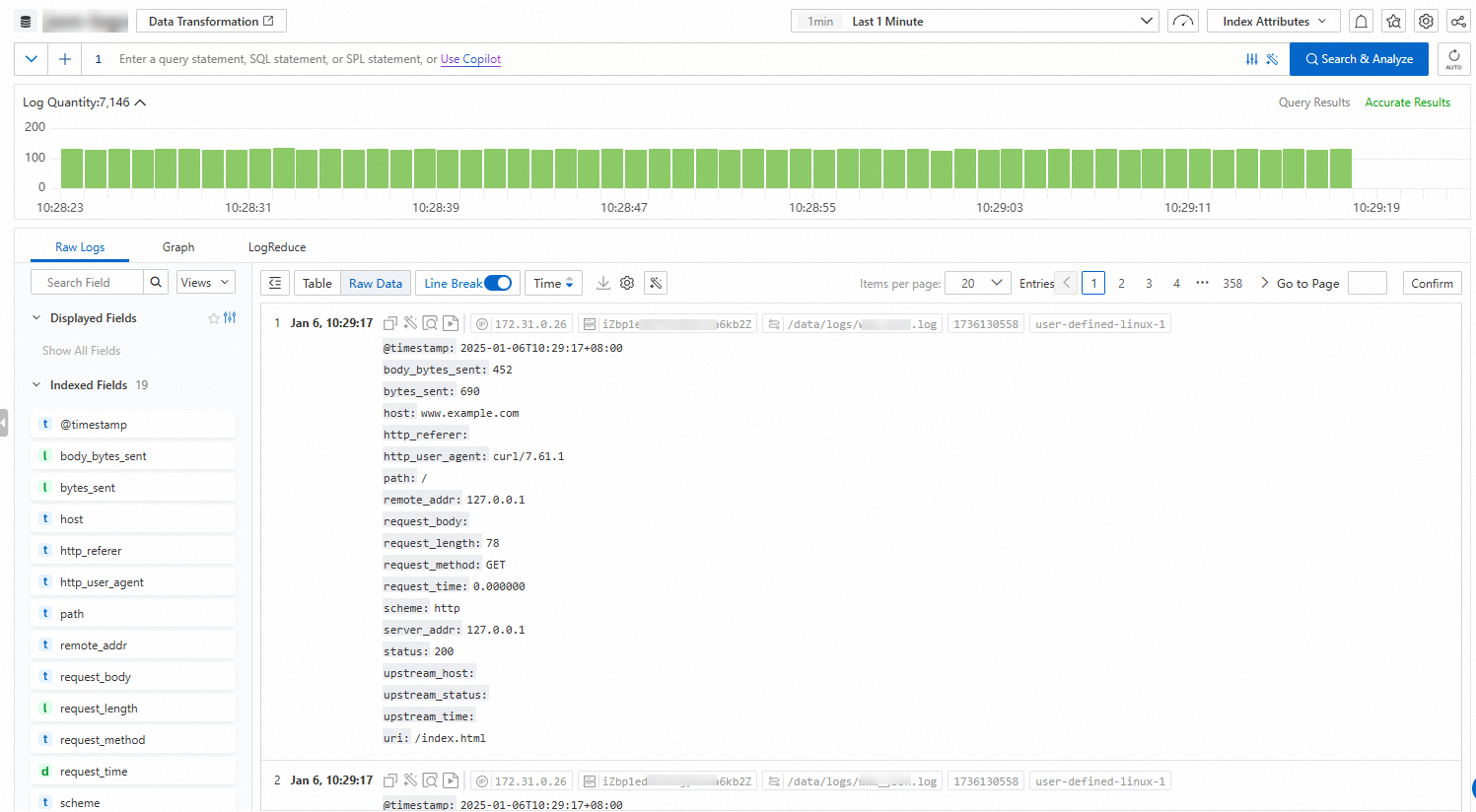
Histogram
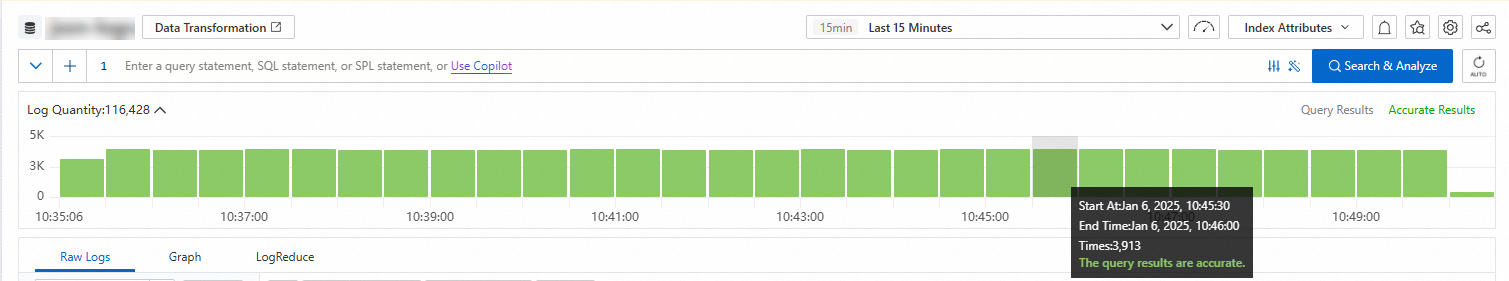
Hover over a green block to view the time range and the number of log hits in that time range.
Double-click a green block to view the log distribution with a finer time granularity. The Raw Logs tab also displays the query results for the specified time range.
Raw Logs
Log details
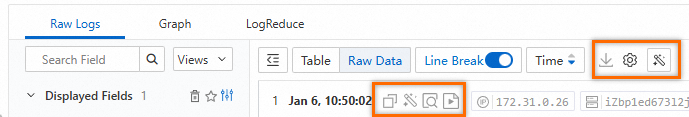
Click Table or Raw to switch the log format.
: Download the logs to your local computer. For more information, see Download logs.
 >JSON Settings: Set the JSON display type and expansion level.
>JSON Settings: Set the JSON display type and expansion level.  >Event Settings: Configure events for raw logs.
>Event Settings: Configure events for raw logs.  : Copy the log content.
: Copy the log content. : SLS Copilot. Summarize information and find error messages in the log content.
: SLS Copilot. Summarize information and find error messages in the log content. : View the context of a specific log in the original file. The contextual query feature is available only for logs collected using Logtail. For more information, see Contextual query.
: View the context of a specific log in the original file. The contextual query feature is available only for logs collected using Logtail. For more information, see Contextual query. : Monitor log content in real time and extract key log information. The LiveTail feature is available only for logs collected using Logtail. For more information, see LiveTail.
: Monitor log content in real time and extract key log information. The LiveTail feature is available only for logs collected using Logtail. For more information, see LiveTail.
Displayed Fields
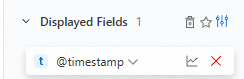
In the Displayed Fields section, click the
 icon next to a field to remove it from Displayed Fields. The field is then hidden from the log information on the right.
icon next to a field to remove it from Displayed Fields. The field is then hidden from the log information on the right. : Save a view. After you set the displayed fields, you can save the view. You can then select the saved view from the drop-down list above the log details.
: Save a view. After you set the displayed fields, you can save the view. You can then select the saved view from the drop-down list above the log details. >Tag Settings: Set a field as a system tag.
>Tag Settings: Set a field as a system tag. >Alias: After you enable this feature, field names are replaced by their aliases. Fields without an alias continue to show their original names. To set a field alias, see Create an index.
>Alias: After you enable this feature, field names are replaced by their aliases. Fields without an alias continue to show their original names. To set a field alias, see Create an index.
Indexed fields
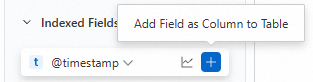
In the Indexed Fields section, click the
 icon next to a field to add it to Displayed Fields. The field is then shown in the log information on the right.
icon next to a field to add it to Displayed Fields. The field is then shown in the log information on the right. : View the Basic Distribution and Statistical Metrics of the field. For more information, see Field settings.
: View the Basic Distribution and Statistical Metrics of the field. For more information, see Field settings.
Statistical charts
Statistical charts are rendered by Simple Log Service based on query and analysis statements. Simple Log Service provides various chart types, such as tables, line charts, and column charts. For more information, see Statistical charts. After you run a query and analysis statement, you can view the resulting visualizations on the Statistical Charts tab. 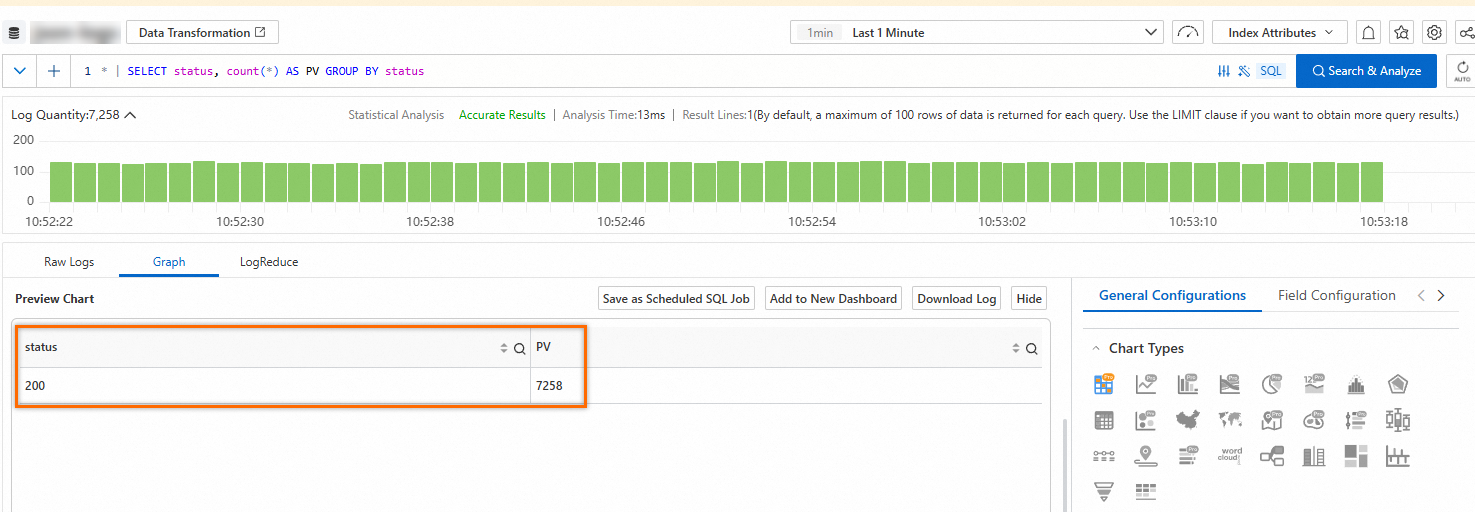
Other features on this tab are described below:
Add to Dashboard: A dashboard is a real-time data analysis tool provided by Simple Log Service. Click Add to Dashboard to save the chart to a dashboard. For more information, see Visualization overview.
Save as Scheduled SQL: Simple Log Service provides the Scheduled SQL feature. This feature lets you periodically analyze data, store aggregated data, and perform projection and filtering. For more information, see Scheduled SQL.
Interaction Occurrences: Interaction occurrences are an essential data analytics feature. This feature lets you change the hierarchy of data dimensions and the granularity of analysis to obtain more detailed information from your data. For more information, see Add an interaction occurrence to a dashboard for drill-down analysis.
LogReduce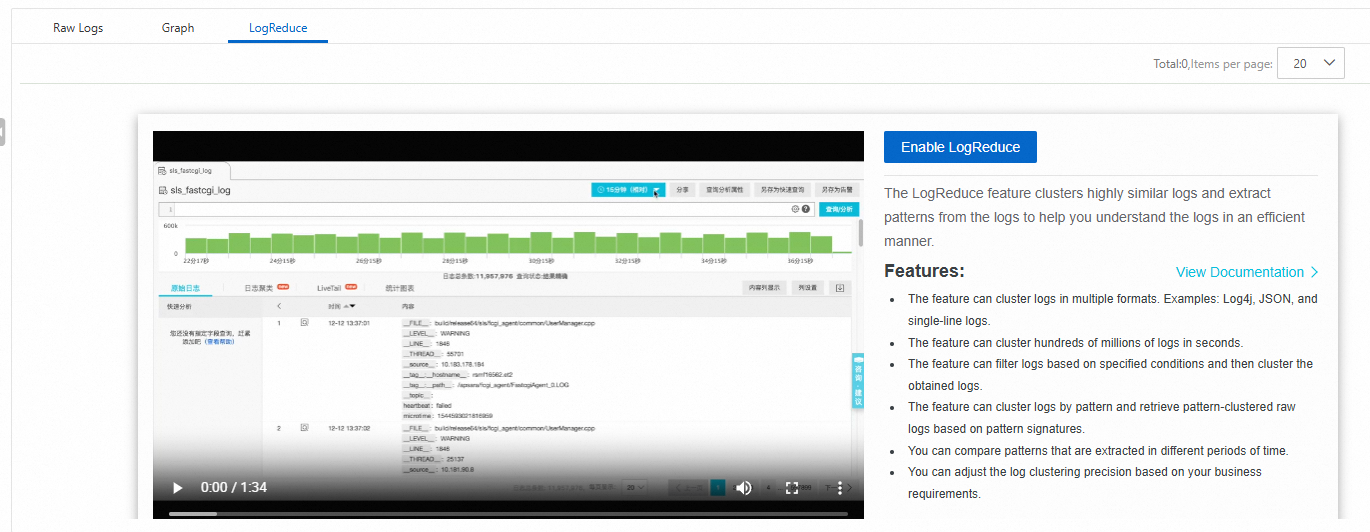
On the LogReduce tab, click Enable LogReduce to aggregate similar logs during log collection. For more information, see LogReduce.
SQL Enhancement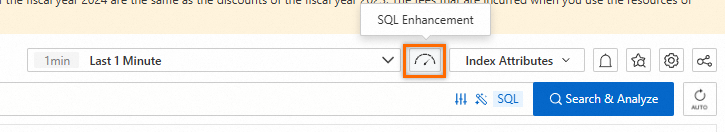
Click the ![]() icon in the upper-right corner to enable Dedicated SQL for a single query. If the data volume is large, a standard SQL query may not be able to analyze all logs within the specified time range. Enabling Dedicated SQL adds computing resources to increase the amount of data that can be analyzed in a single query. To enable this feature by default, see High-performance and accurate query and analysis (Dedicated SQL).
icon in the upper-right corner to enable Dedicated SQL for a single query. If the data volume is large, a standard SQL query may not be able to analyze all logs within the specified time range. Enabling Dedicated SQL adds computing resources to increase the amount of data that can be analyzed in a single query. To enable this feature by default, see High-performance and accurate query and analysis (Dedicated SQL).
Alerting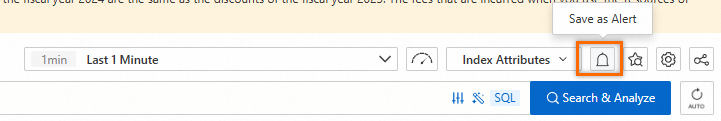
Click the  icon in the upper-right corner and Save as Alert. For more information, see Alert configuration quick start.
icon in the upper-right corner and Save as Alert. For more information, see Alert configuration quick start.
Saved search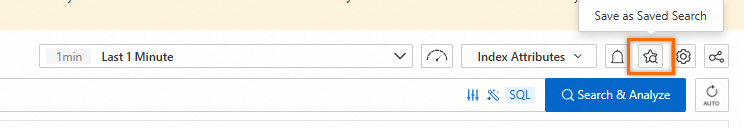
Click the  icon in the upper-right corner and Save as Saved Search. You can use saved queries to quickly run query and analysis operations. For more information, see Saved search.
icon in the upper-right corner and Save as Saved Search. You can use saved queries to quickly run query and analysis operations. For more information, see Saved search.
Sharing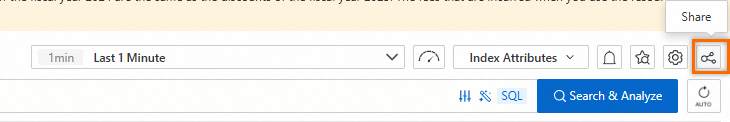
Click the  icon in the upper-right corner to copy the link to the current page and share it with other users. For more information, see Embed console pages and share log data.
icon in the upper-right corner to copy the link to the current page and share it with other users. For more information, see Embed console pages and share log data.
 > Download Log
> Download Log