HTTPS secures data transmission through encryption and integrity checks. HTTP/2 introduces several technical enhancements to improve transmission efficiency and speed. When used together, HTTPS and HTTP/2 deliver a more secure, faster, and smoother network experience for end users.
Configure HTTPS secure acceleration
Introduction
Hypertext Transfer Protocol Secure (HTTPS) is an HTTP channel secured using the SSL or TLS protocol. ApsaraVideo Live provides an HTTPS secure acceleration solution that lets you view, disable, enable, and edit certificates. If a certificate is correctly configured and enabled, both HTTP and HTTPS access are supported. If the certificate does not match the domain name or is disabled, only HTTP access is available.
Benefits of HTTPS acceleration
Encrypts sensitive user information during transmission, preventing security risks such as session ID or cookie leakage if an attacker intercepts the traffic.
Performs data integrity checks during transmission to prevent man-in-the-middle (MITM) attacks, such as DNS hijacking, content hijacking, or tampering.
Precautions
Configuration
Feature | Description |
Disable and Enable the HTTPS feature |
|
View a certificate | You can view certificate information. However, because the private key is sensitive information, you cannot view it. Keep your certificate information secure. |
Modify or edit a certificate | You can modify or edit a certificate. The change takes about five minutes to take effect. Perform this operation with caution. |
Certificates
ApsaraVideo Live supports two types of certificate deployments: Alibaba Cloud Security certificates and your own certificates.
If you enable the Enable HTTPS feature for an accelerated domain name, you must upload its certificate and private key in PEM format.
ApsaraVideo Live uses the Tengine service, which is based on Nginx. Therefore, it supports only certificates readable by Nginx—specifically, those in PEM format.
Only SSL or TLS handshakes that include Server Name Indication (SNI) information are supported.
The uploaded certificate and private key must match. Otherwise, a verification error occurs.
An updated certificate takes approximately five minutes to take effect.
Password-protected private keys are not supported.
Procedure
Step 1: Purchase a certificate
To enable Enable HTTPS, you need a certificate that matches the accelerated domain name. You can go to the Certificate Service page and click Buy Now to purchase a certificate. If you already have your own certificate, you can skip this step.
Step 2: Configure a streaming domain
Enable HTTPS secure acceleration.
Log on to the ApsaraVideo Live console.
In the left-side navigation pane, click Domain Names. The Domain Management page appears.
Select the streaming domain for which you want to configure HTTPS secure acceleration, and click Domain Settings.
Click HTTPS Settings and turn on the HTTPS Certificate switch.
Select a certificate.
Alibaba Cloud Security certificate: For the certificate type, click Alibaba Cloud Security. Select a certificate that you purchased from Certificate Service. Choose the certificate by its name to match the accelerated domain name.
Your own certificate: For the certificate type, click Others. Enter a certificate name, and upload the certificate content and private key. The certificate is saved in the Alibaba Cloud Security console. You can view it in the My Certificates section.
NoteOnly the PEM certificate format is supported.
Step 3: Verify that the certificate is effective
After you complete the configuration, the certificate takes effect globally within approximately one minute. Access a resource using HTTPS. If a lock icon appears in your browser, HTTPS secure acceleration is enabled.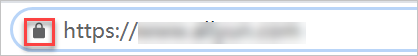
Configure HTTP/2
Introduction
HTTP/2, also known as HTTP 2.0, introduces features such as multiplexing, HTTP header compression, request prioritization, and server push compared to HTTP 1.1. It resolves limitations in HTTP 1.1, optimizes request performance, and maintains compatibility with HTTP 1.1 semantics. Browsers including Chrome, Edge, Safari, and Firefox support the HTTP/2 protocol.
Benefits of HTTP/2
Binary protocol: Unlike HTTP 1.x, which relies on text-based parsing, HTTP/2 splits all transmitted information into smaller messages and frames encoded in binary format. This binary structure enhances protocol extensibility—for example, by enabling dedicated frames for data and instructions.
Multiplexing: In HTTP 1.x, performance optimizations often involve techniques like sprites or multiple domain names due to browser-imposed limits on concurrent requests per domain. When a page requires many resources, head-of-line (HOL) blocking forces subsequent requests to wait. HTTP/2, built on a binary framing layer, allows simultaneous transmission of multiple requests and responses over a single TCP connection. These are reassembled at the receiving end using stream identifiers and headers, eliminating HOL blocking and significantly improving transmission performance.
Header compression: HTTP request headers contain substantial repeated information. HTTP/2 uses the HPACK compression format, where both endpoints maintain a cached index table of header fields. For identical headers, only the index number is transmitted, enhancing efficiency and speed.
Server Push: The server can proactively send multiple responses for a single client request, delivering resources to the client without waiting for explicit requests.
Precautions
Before performing this operation, ensure that HTTPS secure acceleration is configured.
If you are configuring an HTTPS certificate for the first time, wait until the certificate configuration is complete and effective before enabling HTTP/2.
If you disable the HTTPS certificate feature, the HTTP/2 setting becomes unavailable and cannot be enabled.
If you enable HTTP/2 and then disable the HTTPS certificate feature, HTTP/2 also becomes invalid.
Enable or disable HTTP/2
- Log on to the ApsaraVideo Live console.
In the left-side navigation pane, click Domain Names. The Domain Management page appears.
Find the streaming domain that you want to configure and click Domain Settings in the Actions column.
In the navigation pane on the left for the domain, click HTTPS Settings.
In the HTTP/2 section, turn the HTTP/2 feature on or off.
Force redirect
Before performing this operation, ensure that HTTPS secure acceleration is configured.
Introduction
If you have enabled HTTPS secure acceleration for your accelerated domain name, you can customize settings to force a redirect of the original request from an end user.
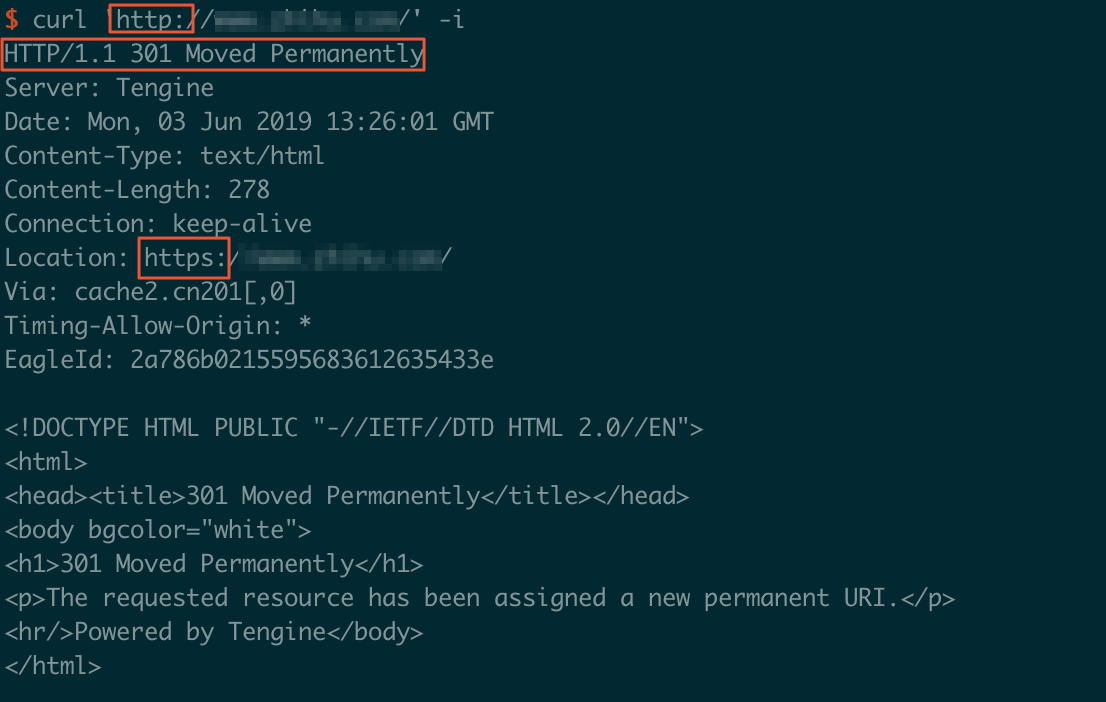
For example, if you enable HTTP > HTTPS, an end user sends an HTTP request. The server returns an HTTP 301 status code response, forcibly redirecting the original HTTP request to an HTTPS request, as shown in the following figure.
Procedure
- Log on to the ApsaraVideo Live console.
In the left-side navigation pane, click Domain Names. The Domain Management page appears.
Find the streaming domain that you want to configure and click Domain Settings in the Actions column.
Click .
Click Change Settings.
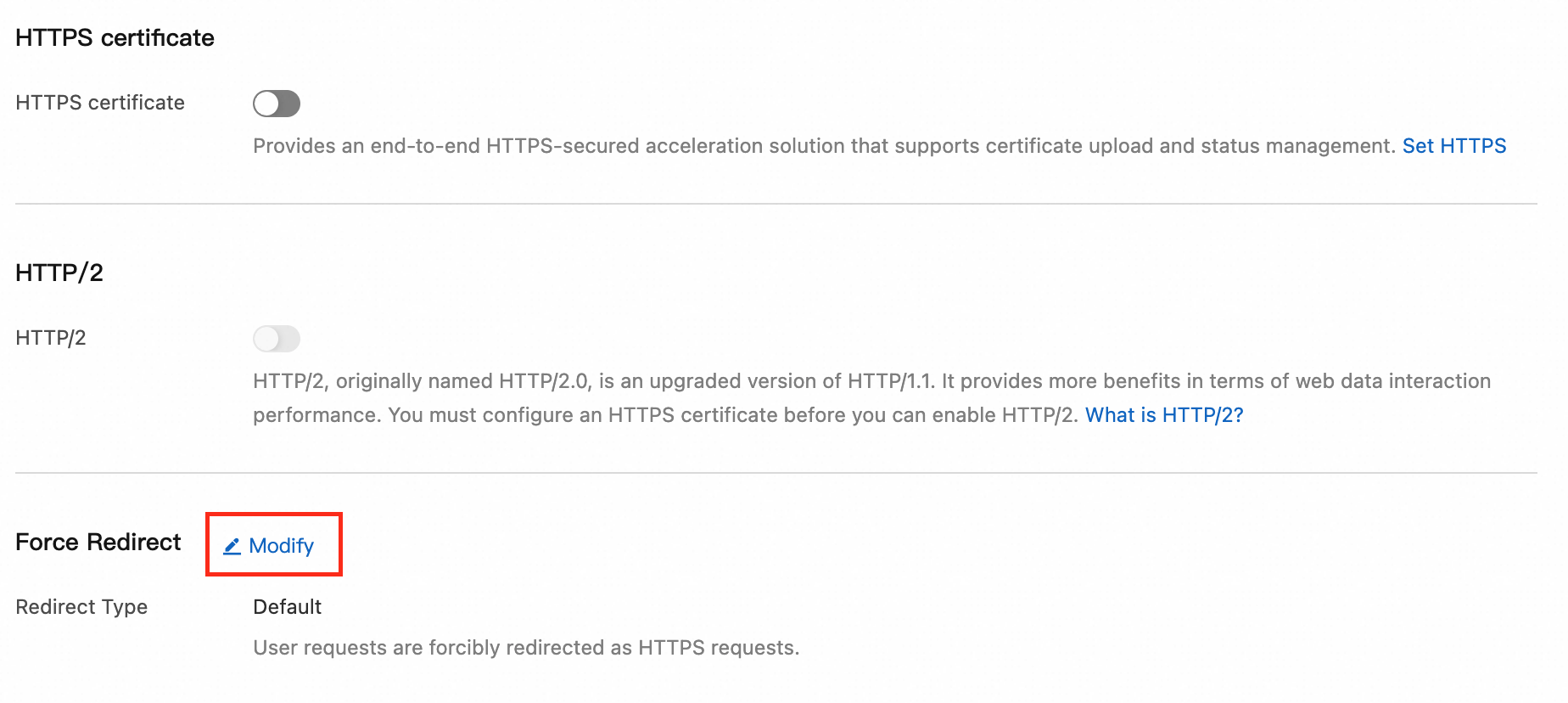
Select a Redirect Type.
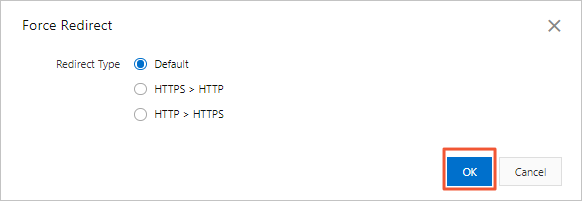
Redirect Type
Description
Default
Both HTTP and HTTPS requests are supported.
HTTPS > HTTP
Requests from clients to points of presence (POPs) are forcibly redirected to HTTP.
HTTP > HTTPS
Requests from clients to POPs are forcibly redirected to HTTPS to ensure access security.
Click OK.
Certificate format description
This section describes the certificate formats that ApsaraVideo Live supports and how to convert certificates to the required format.
Certificates issued by a root CA
Certificates issued by a root certificate authority (CA) can be used for various types of server software, such as Apache, IIS, Nginx, and Tomcat. ApsaraVideo Live uses Nginx servers to process certificates. The certificate file usually has a .crt extension, and the private key file usually has a .key extension.
When you upload a certificate, follow these formatting rules:
Include the header
-----BEGIN CERTIFICATE-----and the footer-----END CERTIFICATE-----.Each line must contain 64 characters. The last line can contain fewer than 64 characters.
The following figure shows an example of a certificate in PEM format in a Linux environment.

Certificates issued by an intermediate authority
If your certificate is issued by an intermediate authority, the certificate file contains multiple certificates. You must combine the server certificate and the intermediate certificate into a single file before you upload it.
Concatenation rule: The server certificate must be placed before the intermediate certificate. The issuing authority typically provides instructions with the certificate. Make sure to follow the provided rules.
Certificate chain issued by an intermediate authority:
-----BEGIN CERTIFICATE-----
-----END CERTIFICATE-----
-----BEGIN CERTIFICATE-----
-----END CERTIFICATE-----
-----BEGIN CERTIFICATE-----
-----END CERTIFICATE-----
Certificate chain rules:
Do not include empty lines between certificates.
Each certificate must comply with the formatting requirements.
RSA private key format requirements
Follow these rules for RSA private keys:
To generate a private key locally, run the following command:
openssl genrsa -out privateKey.pem 2048. In this command,privateKey.pemis your private key file.The key must start with
-----BEGIN RSA PRIVATE KEY-----and end with-----END RSA PRIVATE KEY-----. Include these header and footer lines when you upload the key.Each line must contain 64 characters. The last line can contain fewer than 64 characters.

If you did not generate your private key using the method described above, and it is in a format that includes -----BEGIN PRIVATE KEY----- and -----END PRIVATE KEY-----, you can convert it as follows:
openssl rsa -in old_server_key.pem -out new_server_key.pemThen, upload the content of new_server_key.pem together with the certificate.
Methods to convert certificate formats
HTTPS secure acceleration supports only certificates in PEM format. If your certificate is in a different format, you must convert it to PEM. You can use the OpenSSL tool to perform the conversion. The following table describes how to convert certificates from several common formats to the PEM format.
Conversion method | Description |
Convert DER to PEM | The DER format is common on the Java platform.
|
Convert P7B to PEM | The P7B format is common on Windows Server and Tomcat.
|
Convert PFX to PEM | The PFX format is common on Windows Server.
|