LDAP authentication requires users to provide their LDAP credentials when connecting to Hive services, adding access control to your EMR cluster. EMR integrates with OpenLDAP out of the box, so you can enable authentication with a single switch — no manual LDAP configuration required for most setups.
If you are running an earlier EMR version or connecting to a self-managed LDAP server, follow the manual configuration path instead.
Prerequisites
Before you begin, ensure that you have:
A DataLake or custom cluster with both Hive and OpenLDAP services selected during creation. For more information, see Create a cluster
An EMR user added to OpenLDAP. For more information, see Add a user
Enable LDAP authentication with one click
This method uses the enableLDAP switch in the EMR console. The steps vary depending on your EMR version — both EMR V5.11.1 or later (EMR V3.45.1 or later) and earlier versions are supported. For connecting to a self-managed LDAP server, see Manually configure LDAP authentication.
Steps overview:
Go to the Services tab for your cluster.
Enable the enableLDAP switch for Hive.
Restart HiveServer.
Connect to HiveServer using your LDAP credentials.
Step 1: Go to the Services tab
Log on to the EMR console.
In the left-side navigation pane, click EMR on ECS.
In the top navigation bar, select the region where your cluster resides and select a resource group.
On the EMR on ECS page, find your cluster and click Services in the Actions column.
Step 3: Restart HiveServer
In the Components section, click Restart in the Actions column of HiveServer.
In the dialog box, enter a reason in the Execution Reason field and click OK.
In the Confirm dialog box, click OK.
Step 4: Connect to HiveServer
After HiveServer restarts, use your LDAP credentials to connect. SSH into your cluster (see Log on to a cluster), then run one of the following commands:
Beeline:
beeline -u jdbc:hive2://master-1-1:10000 -n <user> -p <password>Java Database Connectivity (JDBC) connection string:
jdbc:hive2://master-1-1:10000/default;user=<user>;password=<password>Replace <user> with the LDAP username and <password> with the LDAP password of the user you added in the prerequisite step.
Manually configure LDAP authentication
Use this path if you are on an earlier EMR version or connecting to a self-managed LDAP server instead of the built-in OpenLDAP service.
Before you start, collect the following information about your LDAP server:
| Information | EMR built-in OpenLDAP | Self-managed LDAP |
|---|---|---|
| Hostname | emr-header-1 | Your LDAP server hostname or IP address |
| Port | 10389 | Your LDAP server port |
| Base DN | ou=people,o=emr | The base distinguished name (DN) for your users |
Add configuration items to hiveserver2-site.xml
On the Configure page of the Hive service, go to the hiveserver2-site.xml tab and add the following configuration items. For more information, see Manage configuration items.
| Configuration item | Value | Description |
|---|---|---|
hive.server2.authentication | LDAP | Sets the authentication method for HiveServer2. |
hive.server2.authentication.ldap.url | ldap://{ldap_hostname}:{port} (e.g., ldap://master-1-1:10389) | The URL of your LDAP server. Replace {ldap_hostname} with the hostname or IP address, and {port} with the port number. |
hive.server2.authentication.ldap.baseDN | ou=people,o=emr | The base DN for user lookups. For the built-in OpenLDAP service, use ou=people,o=emr. For a self-managed LDAP server, set this to match your directory structure. |
After saving the configuration, restart HiveServer2 for the changes to take effect.
Verify the connection
SSH into your cluster (see Log on to a cluster) and connect using LDAP credentials:
Beeline:
beeline -u jdbc:hive2://master-1-1:10000 -n <user> -p <password>JDBC connection string:
jdbc:hive2://master-1-1:10000/default;user=<user>;password=<password>A successful connection opens a Beeline prompt. If authentication fails, verify that the username and password match a valid entry in your LDAP directory.
Restrict access to specific users or groups
By default, any valid LDAP user can connect to HiveServer2. To limit access to specific users or groups, add the following configuration items to the hiveserver2-site.xml tab on the Configure page of the Hive service.
| Configuration item | Example value | Action | Description |
|---|---|---|---|
hive.server2.authentication.ldap.userDNPattern | uid=%s,ou=people,o=emr | Add | The DN pattern for user lookups. HiveServer2 replaces %s with the actual username during authentication. |
hive.server2.authentication.ldap.groupFilter | username | Add | A comma-separated list of LDAP groups. Only users in these groups can connect to HiveServer2. |
hive.server2.authentication.ldap.groupClassKey | posixGroup | Add | The objectClass value for LDAP group objects. |
hive.server2.authentication.ldap.groupMembershipKey | memberUid | Add | The LDAP attribute that stores group membership. |
hive.server2.authentication.ldap.baseDN | o=emr | Modify | Update the base DN to a path that covers both users and groups, so group filtering works correctly. |
After saving the configuration, restart HiveServer2. Connect using a user that belongs to one of the groups specified in hive.server2.authentication.ldap.groupFilter.
Troubleshooting
Connection fails after enabling LDAP authentication for Hive
If you see the following error when running a Beeline command:
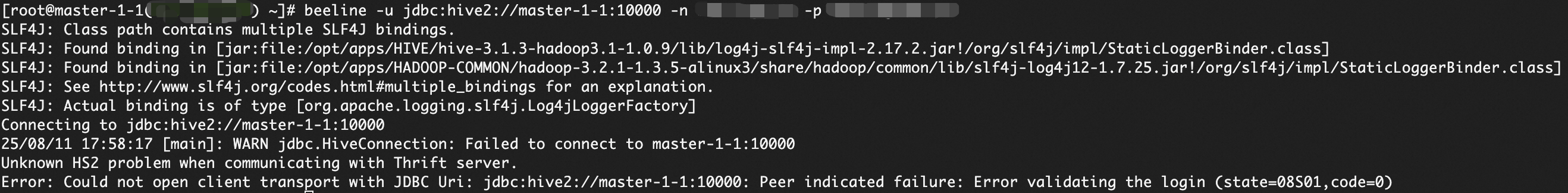
The user you specified in the connection command failed LDAP authentication. This usually means the user is not included in the hive.server2.authentication.ldap.groupFilter configuration.
To fix this, add the user to hive.server2.authentication.ldap.groupFilter in hiveserver2-site.xml, then restart HiveServer2. Alternatively, connect using a user that is already listed in groupFilter.
 > enableLDAP
> enableLDAP