To run a DTS task across Alibaba Cloud accounts, the account that owns the database instance must grant the account that creates the task permission to access its cloud resources. This is done by creating a RAM role, attaching the AliyunDTSRolePolicy policy, and updating the trust policy.
Limitations
Cross-account two-way synchronization is only supported between the following instance types:
ApsaraDB RDS for MySQL instances or clusters
Tair (Enterprise Edition) instances
ApsaraDB for MongoDB replica set instances or sharded cluster instances
For a cross-account two-way synchronization task, both the source and destination database accounts must complete RAM authorization separately.
Synchronization between accounts of different cloud types—such as between a Finance Cloud account and a government cloud account—is not supported.
Log in to the RAM console using the Alibaba Cloud account (root account), not a RAM user. Using a RAM user may cause authorization errors when you create the DTS task.
Prerequisites
Before you begin, make sure that DTS has the required permissions to access cloud resources. For details, see Grant permissions to DTS to access cloud resources.
Supported databases
Cross-account access is determined by the combination of Database type and Connection type. The setting for the source database does not affect which database types are available for the destination database.
Source databases
Source databases
| Database type | Connection type |
|---|---|
| MySQL | Alibaba Cloud Instance; Express Connect, VPN Gateway, or Smart Access Gateway; Self-managed Database on ECS |
| PolarDB for MySQL | Alibaba Cloud Instance |
| Tair/Redis | Alibaba Cloud Instance; Express Connect, VPN Gateway, or Smart Access Gateway; Self-managed Database on ECS; Cloud Enterprise Network (CEN); Database Gateway |
| SQL Server | Alibaba Cloud Instance; Express Connect, VPN Gateway, or Smart Access Gateway |
| PostgreSQL | Alibaba Cloud Instance; Express Connect, VPN Gateway, or Smart Access Gateway |
| MongoDB | Alibaba Cloud Instance; Express Connect, VPN Gateway, or Smart Access Gateway; Self-managed Database on ECS; Cloud Enterprise Network (CEN) |
| Oracle | Express Connect, VPN Gateway, or Smart Access Gateway |
| PolarDB (Compatible with Oracle) | Alibaba Cloud Instance; Express Connect, VPN Gateway, or Smart Access Gateway |
| PolarDB for PostgreSQL | Alibaba Cloud Instance |
| PolarDB-X 1.0 | Alibaba Cloud Instance |
| PolarDB-X 2.0 | Alibaba Cloud Instance |
| DB2 for iSeries (AS/400) | Express Connect, VPN Gateway, or Smart Access Gateway |
| DB2 for LUW | Express Connect, VPN Gateway, or Smart Access Gateway; Self-managed Database on ECS |
| MariaDB | Alibaba Cloud Instance; Express Connect, VPN Gateway, or Smart Access Gateway; Self-managed Database on ECS |
| ApsaraDB OceanBase for MySQL | Alibaba Cloud Instance; Express Connect, VPN Gateway, or Smart Access Gateway; Self-managed Database on ECS |
| SLS | Alibaba Cloud Instance |
| AnalyticDB for MySQL 3.0 | Alibaba Cloud Instance |
| Kafka | Alibaba Cloud Instance; Express Connect, VPN Gateway, or Smart Access Gateway; Self-managed Database on ECS |
Destination databases
Destination databases
| Database type | Connection type |
|---|---|
| MySQL | Alibaba Cloud Instance |
| PolarDB for MySQL | Alibaba Cloud Instance |
| AnalyticDB for MySQL 3.0 | Alibaba Cloud Instance |
| Tair/Redis | Alibaba Cloud Instance |
| ClickHouse | Alibaba Cloud Instance |
| SelectDB | Alibaba Cloud Instance |
| MongoDB | Alibaba Cloud Instance |
Cross-account scenarios
There are three scenarios, depending on which database is cross-account. Each scenario determines which account configures RAM authorization, which account ID goes into the trust policy, and which account creates the DTS task.
| Scenario | Source setting | Destination setting | Who configures RAM auth | Trust policy account ID | Who creates the DTS task |
|---|---|---|---|---|---|
| Cross-account source database | Replicate Data Across Alibaba Cloud Accounts = Yes | Replicate Data Across Alibaba Cloud Accounts = No | Source database account (Account A) | Destination database account ID (Account B) | Destination database account (Account B) |
| Cross-account destination database | Replicate Data Across Alibaba Cloud Accounts = No | Replicate Data Across Alibaba Cloud Accounts = Yes | Destination database account (Account B) | Source database account ID (Account A) | Source database account (Account A) |
| Cross-account source and destination databases | Replicate Data Across Alibaba Cloud Accounts = Yes | Replicate Data Across Alibaba Cloud Accounts = Yes | Source database account (Account A) and destination database account (Account B)—each independently | DTS task account ID (Account C) | Designated account (Account C) |
Before you configure RAM authorization
Collect the account IDs you need before starting. Go to the Security SettingsSecurity SettingsSecurity Settings page for each relevant account and note the Account ID.
What you need depends on your scenario:
Cross-account source database: Account A's ID (source database account) and Account B's ID (destination database account, also the task creator)
Cross-account destination database: Account A's ID (source database account, also the task creator) and Account B's ID (destination database account)
Cross-account source and destination databases: Account A's ID (source database account), Account B's ID (destination database account), and Account C's ID (designated task creator account)
You will use these IDs in the trust policy in the steps below.
Scenario 1: Cross-account source database
Account A (source database owner) configures RAM authorization. Account B (destination database owner) creates the DTS task.
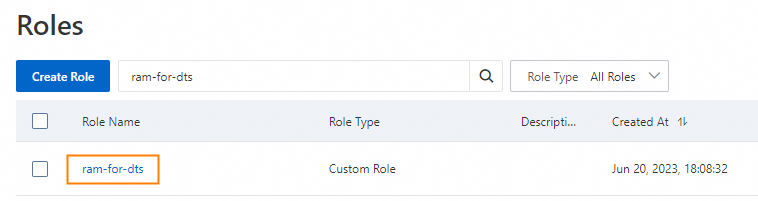
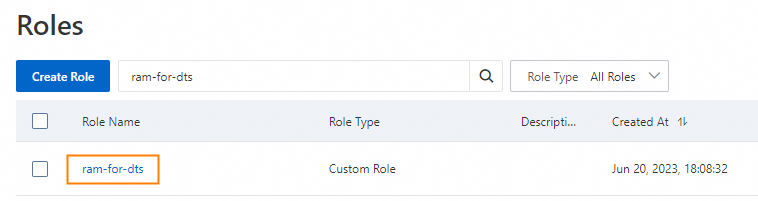
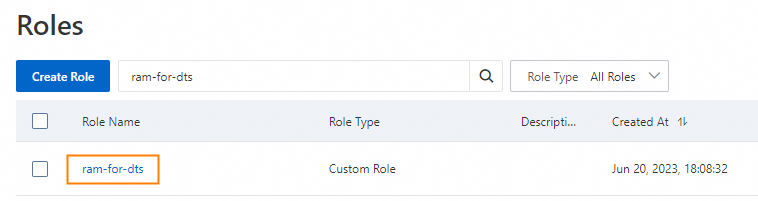
Step 1: Create a RAM role
Log in to the RAM console using Account A.
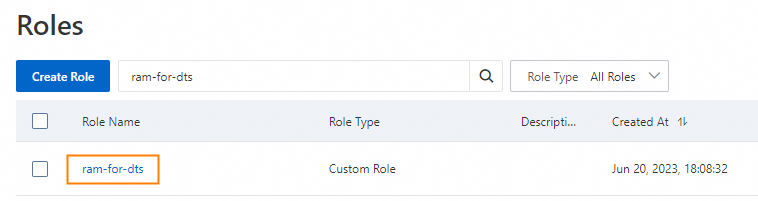
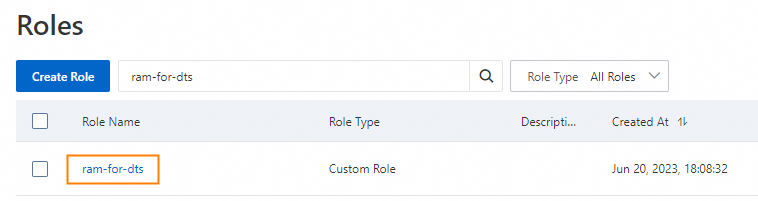
In the left navigation pane, choose Identities > Roles.
ImportantChoose Identities > Roles, not Identities > Users. Using Users causes DTS to fail to access the database instance.

Click Create Role.
In the Create Role panel:
For Principal Type, select Cloud Account.

Set Principal Name to Other Account and enter Account B's ID.

Click OK.
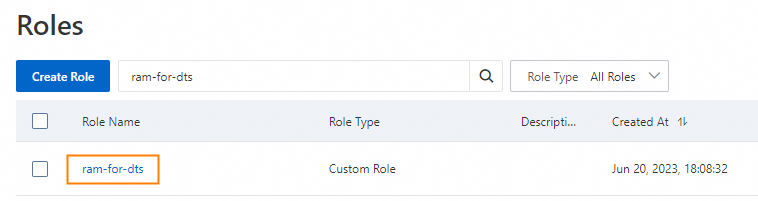
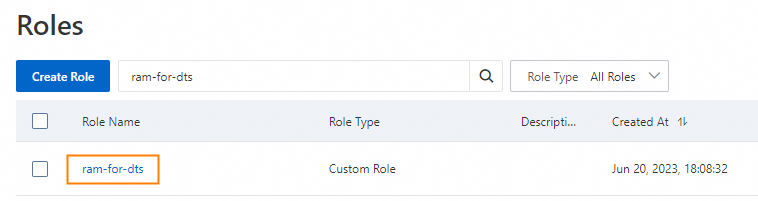
Enter a name for the RAM role (for example,
ram-for-dts) and click OK.
Step 2: Grant permissions to the RAM role
From the page indicating the RAM role is created
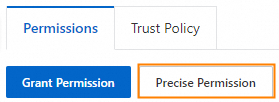
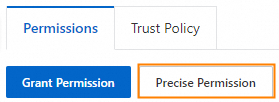
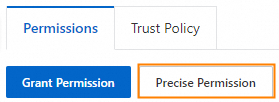
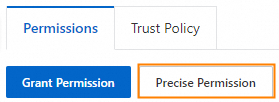
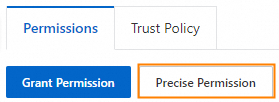
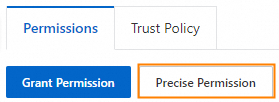
On the Permissions tab, click Precise Permission.
In the Precise Permission panel, set Policy Type to System Policy.

In the Policy Name field, enter
AliyunDTSRolePolicy.Click OK.
Click the
 refresh icon on the Permissions tab to confirm the permission was added.
refresh icon on the Permissions tab to confirm the permission was added.
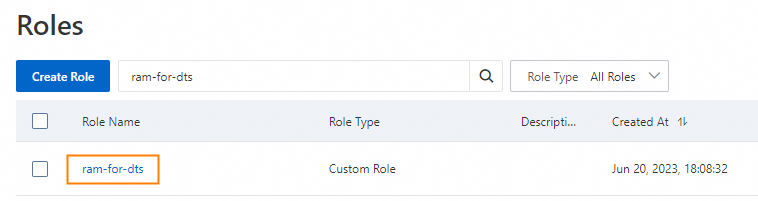
From the RAM role list
Log in to the RAM console using Account A.
In the left navigation pane, choose Identities > Roles.
ImportantChoose Identities > Roles, not Identities > Users.

Click the RAM role you created.
On the Permissions tab, click Precise Permission.
In the Precise Permission panel, set Policy Type to System Policy.

In the Policy Name field, enter
AliyunDTSRolePolicy.Click OK.
Click the
 refresh icon on the Permissions tab to confirm the permission was added.
refresh icon on the Permissions tab to confirm the permission was added.
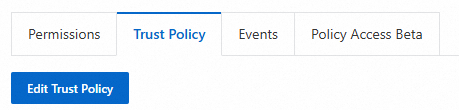
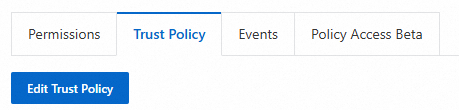
Step 3: Update the trust policy
The trust policy grants Account B permission to use this RAM role and allows DTS to assume it on Account B's behalf. The RAM field specifies who can assume the role; the Service field allows DTS to make requests using that account's identity. Both fields must contain Account B's ID.
From the page indicating the permission is granted
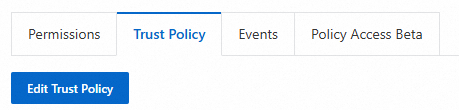
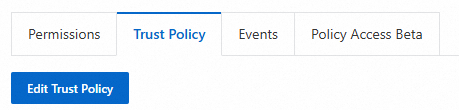
Click the Trust Policy tab.
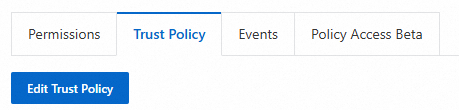
Click Edit Trust Policy.
On the JSON tab, replace the existing content with the following:
{ "Statement": [ { "Action": "sts:AssumeRole", "Effect": "Allow", "Principal": { "RAM": [ "acs:ram::<Alibaba Cloud account ID>:root" ], "Service": [ "<Alibaba Cloud account ID>@dts.aliyuncs.com" ] } } ], "Version": "1" }Replace both
<Alibaba Cloud account ID>placeholders with Account B's ID (the destination database account). <details> <summary>Example (click to expand)</summary>{ "Statement": [ { "Action": "sts:AssumeRole", "Effect": "Allow", "Principal": { "RAM": [ "acs:ram::164682176356****:root" ], "Service": [ "164682176356****@dts.aliyuncs.com" ] } } ], "Version": "1" }</details>
Click OK.
If the
Servicevalue automatically changes to"dts.aliyuncs.com"after saving, the account ID is wrong. This happens when you enter Account A's ID instead of Account B's ID. Correct the ID and save again.
From the RAM role list
Log in to the RAM console using Account A.
In the left navigation pane, choose Identities > Roles.
ImportantChoose Identities > Roles, not Identities > Users.

Click the RAM role you created.
Click the Trust Policy tab.
Click Edit Trust Policy.
On the JSON tab, replace the existing content with the following:
{ "Statement": [ { "Action": "sts:AssumeRole", "Effect": "Allow", "Principal": { "RAM": [ "acs:ram::<Alibaba Cloud account ID>:root" ], "Service": [ "<Alibaba Cloud account ID>@dts.aliyuncs.com" ] } } ], "Version": "1" }Replace both
<Alibaba Cloud account ID>placeholders with Account B's ID.{ "Statement": [ { "Action": "sts:AssumeRole", "Effect": "Allow", "Principal": { "RAM": [ "acs:ram::164682176356****:root" ], "Service": [ "164682176356****@dts.aliyuncs.com" ] } } ], "Version": "1" }</details>
Click OK.
If the
Servicevalue automatically changes to"dts.aliyuncs.com"after saving, the account ID is wrong. Correct the ID and save again.
When you configure the DTS task
When Account B creates the DTS task, set Replicate Data Across Alibaba Cloud Accounts to Yes for the source database. In the Source Database section, enter Account A's ID in the Alibaba Cloud Account field.
Scenario 2: Cross-account destination database
Account B (destination database owner) configures RAM authorization. Account A (source database owner) creates the DTS task.
Step 1: Create a RAM role
Log in to the RAM console using Account B.
In the left navigation pane, choose Identities > Roles.
ImportantChoose Identities > Roles, not Identities > Users. Using Users causes DTS to fail to access the database instance.

Click Create Role.
In the Create Role panel:
For Principal Type, select Cloud Account.

Set Principal Name to Other Account and enter Account A's ID.

Click OK.
Enter a name for the RAM role (for example,
ram-for-dts) and click OK.
Step 2: Grant permissions to the RAM role
From the page indicating the RAM role is created
On the Permissions tab, click Precise Permission.
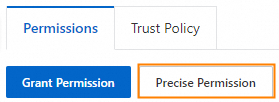
In the Precise Permission panel, set Policy Type to System Policy.

In the Policy Name field, enter
AliyunDTSRolePolicy.Click OK.
Click the
 refresh icon on the Permissions tab to confirm the permission was added.
refresh icon on the Permissions tab to confirm the permission was added.
From the RAM role list
Log in to the RAM console using Account B.
In the left navigation pane, choose Identities > Roles.
ImportantChoose Identities > Roles, not Identities > Users.

Click the RAM role you created.
On the Permissions tab, click Precise Permission.
In the Precise Permission panel, set Policy Type to System Policy.

In the Policy Name field, enter
AliyunDTSRolePolicy.Click OK.
Click the
 refresh icon on the Permissions tab to confirm the permission was added.
refresh icon on the Permissions tab to confirm the permission was added.
Step 3: Update the trust policy
Both fields in the policy must contain Account A's ID (the source database account, which creates the DTS task).
From the page indicating the permission is granted
Click the Trust Policy tab.
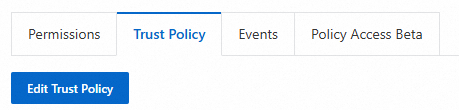
Click Edit Trust Policy.
On the JSON tab, replace the existing content with the following:
{ "Statement": [ { "Action": "sts:AssumeRole", "Effect": "Allow", "Principal": { "RAM": [ "acs:ram::<Alibaba Cloud account ID>:root" ], "Service": [ "<Alibaba Cloud account ID>@dts.aliyuncs.com" ] } } ], "Version": "1" }Replace both
<Alibaba Cloud account ID>placeholders with Account A's ID (the source database account). <details> <summary>Example (click to expand)</summary>{ "Statement": [ { "Action": "sts:AssumeRole", "Effect": "Allow", "Principal": { "RAM": [ "acs:ram::164682176356****:root" ], "Service": [ "164682176356****@dts.aliyuncs.com" ] } } ], "Version": "1" }</details>
Click OK.
If the
Servicevalue automatically changes to"dts.aliyuncs.com"after saving, the account ID is wrong. This happens when you enter Account B's ID instead of Account A's ID. Correct the ID and save again.
From the RAM role list
Log in to the RAM console using Account B.
In the left navigation pane, choose Identities > Roles.
ImportantChoose Identities > Roles, not Identities > Users.

Click the RAM role you created.
Click the Trust Policy tab.
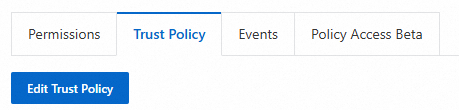
Click Edit Trust Policy.
On the JSON tab, replace the existing content with the following:
{ "Statement": [ { "Action": "sts:AssumeRole", "Effect": "Allow", "Principal": { "RAM": [ "acs:ram::<Alibaba Cloud account ID>:root" ], "Service": [ "<Alibaba Cloud account ID>@dts.aliyuncs.com" ] } } ], "Version": "1" }Replace both
<Alibaba Cloud account ID>placeholders with Account A's ID.{ "Statement": [ { "Action": "sts:AssumeRole", "Effect": "Allow", "Principal": { "RAM": [ "acs:ram::164682176356****:root" ], "Service": [ "164682176356****@dts.aliyuncs.com" ] } } ], "Version": "1" }</details>
Click OK.
If the
Servicevalue automatically changes to"dts.aliyuncs.com"after saving, the account ID is wrong. Correct the ID and save again.
When you configure the DTS task
When Account A creates the DTS task, set Replicate Data Across Alibaba Cloud Accounts to Yes for the destination database. In the Destination Database section, enter Account B's ID in the Alibaba Cloud Account field.
Scenario 3: Cross-account source and destination databases
Both Account A (source database owner) and Account B (destination database owner) must configure RAM authorization independently. Account C is the designated account that creates the DTS task. In both cases, the trust policy must contain Account C's ID.
Step 1: Account A configures RAM authorization
Create a RAM role.
Log in to the RAM console using Account A.
In the left navigation pane, choose Identities > Roles.
 > Important: Choose Identities > Roles, not Identities > Users. Using Users causes DTS to fail to access the database instance.
> Important: Choose Identities > Roles, not Identities > Users. Using Users causes DTS to fail to access the database instance.Click Create Role.
In the Create Role panel:
For Principal Type, select Cloud Account.

Set Principal Name to Other Account and enter Account C's ID.

Click OK.
Enter a name for the RAM role (for example,
ram-for-dts) and click OK.
Grant permissions to the RAM role.
From the page indicating the RAM role is created
On the Permissions tab, click Precise Permission.
In the Precise Permission panel, you can set Policy Type to System Policy.

Enter
AliyunDTSRolePolicyin the Policy Name text box.Click OK.
Click the
 icon on the right side of the Permission tab to refresh the page. Verify that the precise authorization was successful.
icon on the right side of the Permission tab to refresh the page. Verify that the precise authorization was successful.
From the RAM role list
Log in to the RAM console using Account A.
In the left navigation pane, choose Identities > Roles.
 > Important: Choose Identities > Roles, not Identities > Users.
> Important: Choose Identities > Roles, not Identities > Users.Click the RAM role you created.
On the Permissions tab, click Precise Permission.
In the Precise Permission panel, set Policy Type to System Policy.

In the Policy Name field, enter
AliyunDTSRolePolicy.Click OK.
Click the
 refresh icon to confirm the permission was added.
refresh icon to confirm the permission was added.
Update the trust policy. Both fields in the policy must contain Account C's ID (the DTS task creator).
From the page indicating the permission is granted
Click the Trust Policy tab.
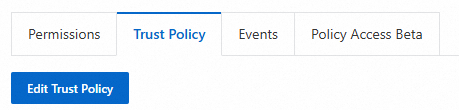
On the Trust Policy tab, click Edit Trust Policy.
On the JSON tab, replace the contents of the policy editor with the following code.
{ "Statement": [ { "Action": "sts:AssumeRole", "Effect": "Allow", "Principal": { "RAM": [ "acs:ram::<Alibaba Cloud account ID>:root" ], "Service": [ "<Alibaba Cloud account ID>@dts.aliyuncs.com" ] } } ], "Version": "1" }Replace the two
<Alibaba Cloud account ID>placeholders with the ID of the Alibaba Cloud account that you will use to create the DTS task.Click OK to save the trust policy.
If the
"<Alibaba Cloud account ID>@dts.aliyuncs.com"in the `Service` section of the code automatically changes to"dts.aliyuncs.com"after you save the trust policy, this indicates that the<Alibaba Cloud account ID>is incorrect. You must enter the ID of the account used to create the DTS task, not the ID of the source database account.
From the RAM role list
Log in to the RAM console using Account A.
In the left navigation pane, choose Identities > Roles.
 > Important: Choose Identities > Roles, not Identities > Users.
> Important: Choose Identities > Roles, not Identities > Users.Click the RAM role you created.
Click the Trust Policy tab.
Click Edit Trust Policy.
On the JSON tab, replace the existing content with the following: ``
json { "Statement": [ { "Action": "sts:AssumeRole", "Effect": "Allow", "Principal": { "RAM": [ "acs:ram::<Alibaba Cloud account ID>:root" ], "Service": [ "<Alibaba Cloud account ID>@dts.aliyuncs.com" ] } } ], "Version": "1" }``Replace both
<Alibaba Cloud account ID>placeholders with Account C's ID.Click OK. > Note: If the
Servicevalue automatically changes to"dts.aliyuncs.com"after saving, the account ID is wrong. Correct the ID and save again.
Step 2: Account B configures RAM authorization
Repeat the same three-step process using Account B (destination database owner). The trust policy must also contain Account C's ID.
Create a RAM role.
Log in to the RAM console using Account B.
In the left navigation pane, choose Identities > Roles.
 > Important: Choose Identities > Roles, not Identities > Users. Using Users causes DTS to fail to access the database instance.
> Important: Choose Identities > Roles, not Identities > Users. Using Users causes DTS to fail to access the database instance.Click Create Role.
In the Create Role panel:
For Principal Type, select Cloud Account.

Set Principal Name to Other Account and enter Account C's ID.

Click OK.
Enter a name for the RAM role (for example,
ram-for-dts) and click OK.
Grant permissions to the RAM role.
From the page indicating the RAM role is created
On the Permissions tab, click Precise Permission.
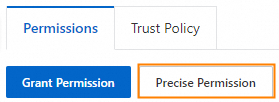
In the Precise Permission panel, you can set Policy Type to System Policy.

Enter
AliyunDTSRolePolicyin the Policy Name text box.Click OK.
Click the
 icon on the right side of the Permission tab to refresh the page. Verify that the precise authorization was successful.
icon on the right side of the Permission tab to refresh the page. Verify that the precise authorization was successful.
From the RAM role list
Log in to the RAM console using Account B.
In the left navigation pane, choose Identities > Roles.
 > Important: Choose Identities > Roles, not Identities > Users.
> Important: Choose Identities > Roles, not Identities > Users.Click the RAM role you created.
On the Permissions tab, click Precise Permission.
In the Precise Permission panel, set Policy Type to System Policy.

In the Policy Name field, enter
AliyunDTSRolePolicy.Click OK.
Click the
 refresh icon to confirm the permission was added.
refresh icon to confirm the permission was added.
Update the trust policy. Both fields in the policy must contain Account C's ID.
From the page indicating the permission is granted
Click the Trust Policy tab.
On the Trust Policy tab, click Edit Trust Policy.
On the JSON tab, replace the contents of the policy editor with the following code.
{ "Statement": [ { "Action": "sts:AssumeRole", "Effect": "Allow", "Principal": { "RAM": [ "acs:ram::<Alibaba Cloud account ID>:root" ], "Service": [ "<Alibaba Cloud account ID>@dts.aliyuncs.com" ] } } ], "Version": "1" }Replace the two
<Alibaba Cloud account ID>placeholders with the ID of the Alibaba Cloud account that you will use to create the DTS task.Click OK to save the trust policy.
If the
"<Alibaba Cloud account ID>@dts.aliyuncs.com"in the `Service` section of the code automatically changes to"dts.aliyuncs.com"after you save the trust policy, this indicates that the<Alibaba Cloud account ID>is incorrect. You must enter the ID of the account used to create the DTS task, not the ID of the destination database account.
From the RAM role list
Log in to the RAM console using Account B.
In the left navigation pane, choose Identities > Roles.
 > Important: Choose Identities > Roles, not Identities > Users.
> Important: Choose Identities > Roles, not Identities > Users.Click the RAM role you created.
Click the Trust Policy tab.
Click Edit Trust Policy.
On the JSON tab, replace the existing content with the following: ``
json { "Statement": [ { "Action": "sts:AssumeRole", "Effect": "Allow", "Principal": { "RAM": [ "acs:ram::<Alibaba Cloud account ID>:root" ], "Service": [ "<Alibaba Cloud account ID>@dts.aliyuncs.com" ] } } ], "Version": "1" }``Replace both
<Alibaba Cloud account ID>placeholders with Account C's ID.Click OK. > Note: If the
Servicevalue automatically changes to"dts.aliyuncs.com"after saving, the account ID is wrong. Correct the ID and save again.
When you configure the DTS task
When Account C creates the DTS task, set Replicate Data Across Alibaba Cloud Accounts to Yes for both the source and destination databases. In the Source Database section, enter Account A's ID in the Alibaba Cloud Account field. In the Destination Database section, enter Account B's ID in the Alibaba Cloud Account field.
What's next
After you complete RAM authorization, create the cross-account DTS task. For details, see Configure a cross-account task.