After you add a service to Anti-DDoS Proxy, the proxy scrubs inbound traffic and forwards it to the origin server. Because the origin server receives connections from Anti-DDoS Proxy rather than from the client directly, additional configuration is required to retrieve originating IP addresses.
The retrieval method depends on the service type:
Non-website service (Layer 4, port-based) -- Install the TOA (TCP Option Address) kernel module. Anti-DDoS Proxy embeds the originating IP address and port in the TCP Option field of the connection handshake.
Website service (Layer 7, domain-based) -- Read the
X-Forwarded-Forheader. Anti-DDoS Proxy appends the originating IP address to this HTTP header before forwarding the request.
To prevent the origin server from blocking legitimate traffic, add the back-to-origin CIDR blocks of your Anti-DDoS Proxy instance to the origin server whitelist. For details, see Allow back-to-origin CIDR blocks to access the origin server.
If the origin server is an Elastic Compute Service (ECS) instance, add the back-to-origin CIDR blocks to the ECS security group. See Add a security group rule.
If the origin server is an ECS instance behind a Server Load Balancer (SLB) instance, add the back-to-origin CIDR blocks to the SLB whitelist. See Enable access control.
Non-website service (Layer 4)
For non-website services forwarded at Layer 4, install the TOA kernel module on the origin server to extract originating IP addresses from the TCP Option field. For instructions, see Install the TOA kernel module to obtain the originating IP addresses of requests.
If the TOA kernel module cannot be installed in your environment, contact technical support.
The TCP Option encoding varies by Anti-DDoS Proxy instance type. The following sections describe the byte layout for each scenario.
Anti-DDoS Proxy instance with an IPv4 address
After you add a non-website service at Layer 4, Anti-DDoS Proxy establishes a TCP connection to the origin server through a three-way handshake. In the last ACK packet, the proxy inserts the originating IP information into the TCP Option field with the following layout:
| Field | Value |
|---|---|
| Option type | 254 |
| Total size | 8 bytes |
| Contents | Source port + source IP address |
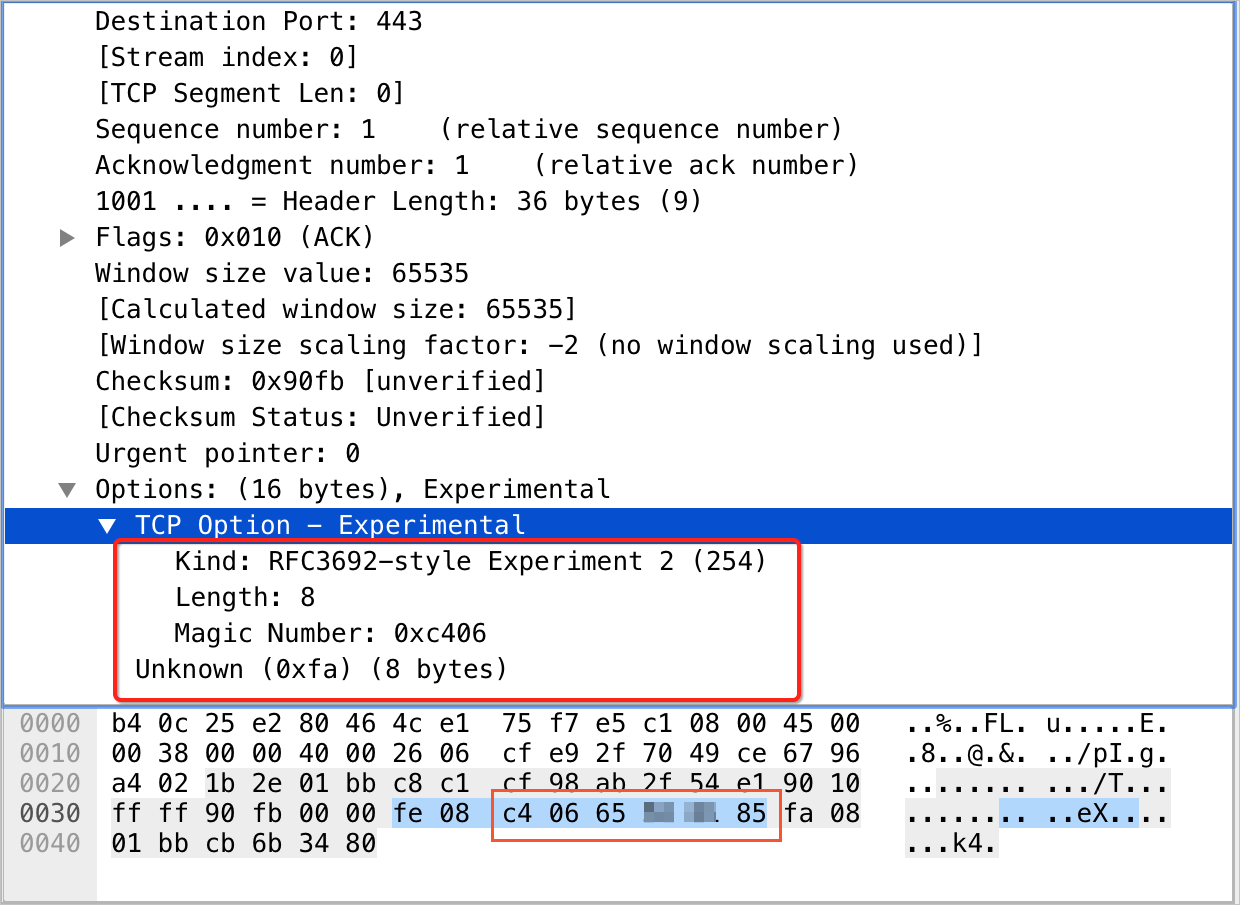
Port number: The Magic Number field contains the port number in hexadecimal. For example, c4 06 converts to decimal 50182.
Source IP address: The four consecutive bytes after the port number represent the IPv4 address in hexadecimal. For example, 65 ** ** 85 converts to 101.*.*.133.
Anti-DDoS Proxy instance with an IPv6 address
V6tov4 mode
When the Anti-DDoS Proxy instance uses an IPv6 address and the origin server uses IPv4, the proxy uses v6tov4 mode. After the three-way handshake completes, the last ACK packet carries the originating IP information in the TCP Option field with the following layout:
| Field | Value |
|---|---|
| Option type | 249 |
| Total size | 40 bytes |
| Contents | Source port + source IP address + Anti-DDoS Proxy IP |
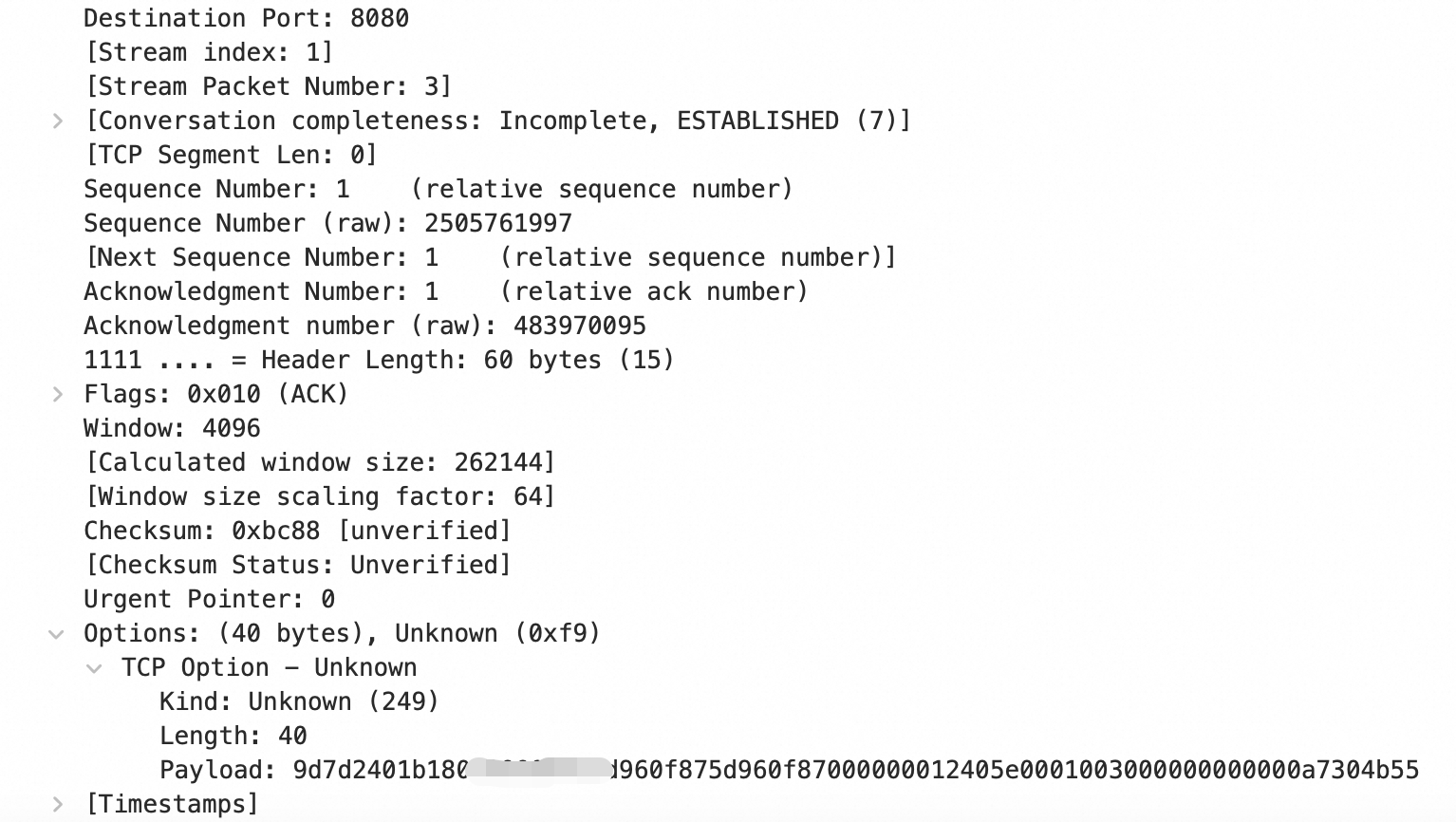
Port number: The first two bytes of the Payload field contain the port number in hexadecimal. For example, 9d7d converts to decimal 40317.
Source IP address: The next 16 bytes after the port number represent the IPv6 source address in hexadecimal. For example, 2401*****0f87 maps to 2401:b180:100*:*:*:f87:5d96:f87.
The remaining 20 bytes in the Payload field contain the Anti-DDoS Proxy IP information.V6tov6 mode
When both the Anti-DDoS Proxy instance and the origin server use IPv6, the proxy uses v6tov6 mode. After the three-way handshake completes, the last ACK packet carries the originating IP information in the TCP Option field with the following layout:
| Field | Value |
|---|---|
| Option type | 253 |
| Total size | 20 bytes |
| Contents | Source port + source IP address |

Port number: The Experiment Identifier field contains the port number in hexadecimal. For example, eb98 converts to decimal 60312.
Source IP address: The Data field contains the IPv6 source address in hexadecimal. For example, 2401*****0f87 maps to 2401:b180:100*:*:*:f87:5d96:f87.
Website service (Layer 7)
When a Layer 7 proxy such as Anti-DDoS Proxy forwards requests to the origin server, the IP address visible to the origin server is the back-to-origin IP address of the proxy, not the originating IP address of the client. Anti-DDoS Proxy records the originating IP address in the X-Forwarded-For header using the following format:
X-Forwarded-For: <originating IP address>, <back-to-origin IP address of Anti-DDoS Proxy>If the request passes through multiple proxy servers, such as a Web Application Firewall (WAF) instance or Alibaba Cloud CDN, each proxy appends its IP address to the header:
X-Forwarded-For: <originating IP address>, <proxy 1 IP>, <proxy 2 IP>, <proxy 3 IP>, ...The first IP address in the X-Forwarded-For header (before the first comma) is the originating IP address of the client.
Retrieve the originating IP address in application code
Use one of the following code snippets to read the X-Forwarded-For header value in your application:
ASP
Request.ServerVariables("HTTP_X_FORWARDED_FOR")ASP.NET (C#)
Request.ServerVariables["HTTP_X_FORWARDED_FOR"]PHP
$_SERVER["HTTP_X_FORWARDED_FOR"]JSP
request.getHeader("HTTP_X_FORWARDED_FOR")Parse the returned value and extract the first IP address (before the first comma) to obtain the originating IP address.
Configure web servers to use originating IP addresses
Common web servers such as NGINX, IIS 6, IIS 7, Apache, and Tomcat can also be configured to resolve originating IP addresses from the X-Forwarded-For header. For configuration instructions, see Retrieve the originating IP addresses of clients.