When sensitive fields—such as phone numbers, email addresses, or ID numbers—pass through a data pipeline, writing them to a target table without protection creates compliance and security risks. The Data Masking node lets you apply field-level masking rules inline as data flows from a source to a target table in a Single-Table Real-Time synchronization task.
Prerequisites
Before you begin, make sure you have:
-
A data source configured in Data Integration. For more information, see Data source management
-
A Single-Table Real-Time synchronization task. For more information, see Configure a single-table real-time synchronization task
Data processing nodes, including the Data Masking node, can only be added to Single-Table Real-Time tasks, between the Source and Destination nodes. For a full list of supported data sources, see Supported data sources and synchronization solutions.
How it works
-
Enable data processing in your Single-Table Real-Time task.
-
Add a Data Masking node and configure a masking rule for each sensitive field.
-
Preview the node output to verify the masked results meet your requirements.
-
Run the task. The masked data is written to the target table.
Add a Data Masking node
Step 1: Set up the task
-
Create a data source. For more information, see Data source management.
-
Create a Single-Table Real-Time synchronization task. For more information, see Configure a single-table real-time synchronization task.
Step 2: Configure the Data Masking node
-
In the task canvas, enable the Data Processing toggle.
-
Click + Add Node and select Data Masking.
-
Configure the node name and description.
-
Click Add to add a row for a masking rule, then configure each row:
-
Upstream Field: Select the source field to mask.
-
Data Masking Rule: Select an existing masking rule, or click New Desensitization Rule to create one.
-
Create a masking rule
When you click New Desensitization Rule, a panel opens. Configure the following:
-
Sensitive Data Type: Select Existing Data Type to use a predefined sensitive data category, or select New Type to define a custom one.
-
Masking method: Choose one of the three methods below.
-
Alias
Replaces a value with a masked value that has similar characteristics. The data format is preserved after masking.
Set the Security domain to an integer from
0to9. Different security domains apply different masking policies, so the same source value produces different masked results across domains.Source value Security domain Masked result john.doe@example.com0 An email-format value with the same structure john.doe@example.com1 A different email-format value Hashing
Transforms source data into a fixed-length string. The result is deterministic: the same source value and security domain always produce the same hash.
Set the Security domain to an integer from
0to9. Different domains use different hashing rules, so the same source value produces a different hash in each domain.Source value Security domain Masked result a1230 ea9da0c87fb455df9013be83bdc20014a1231 9738f2cce017c52099ea530fa34eb128Masking
Replaces characters at specified positions with asterisks (
*). Choose a preset or define a custom pattern.Preset options:
Preset Source value Result Show only the first and last character 138123456781*********8Show only the first three and last two characters 13812345678138******78Show only the first three and last four characters 13812345678138****5678Custom:
Define up to 10 segments. At least one segment must be set to Remaining Digits.
-
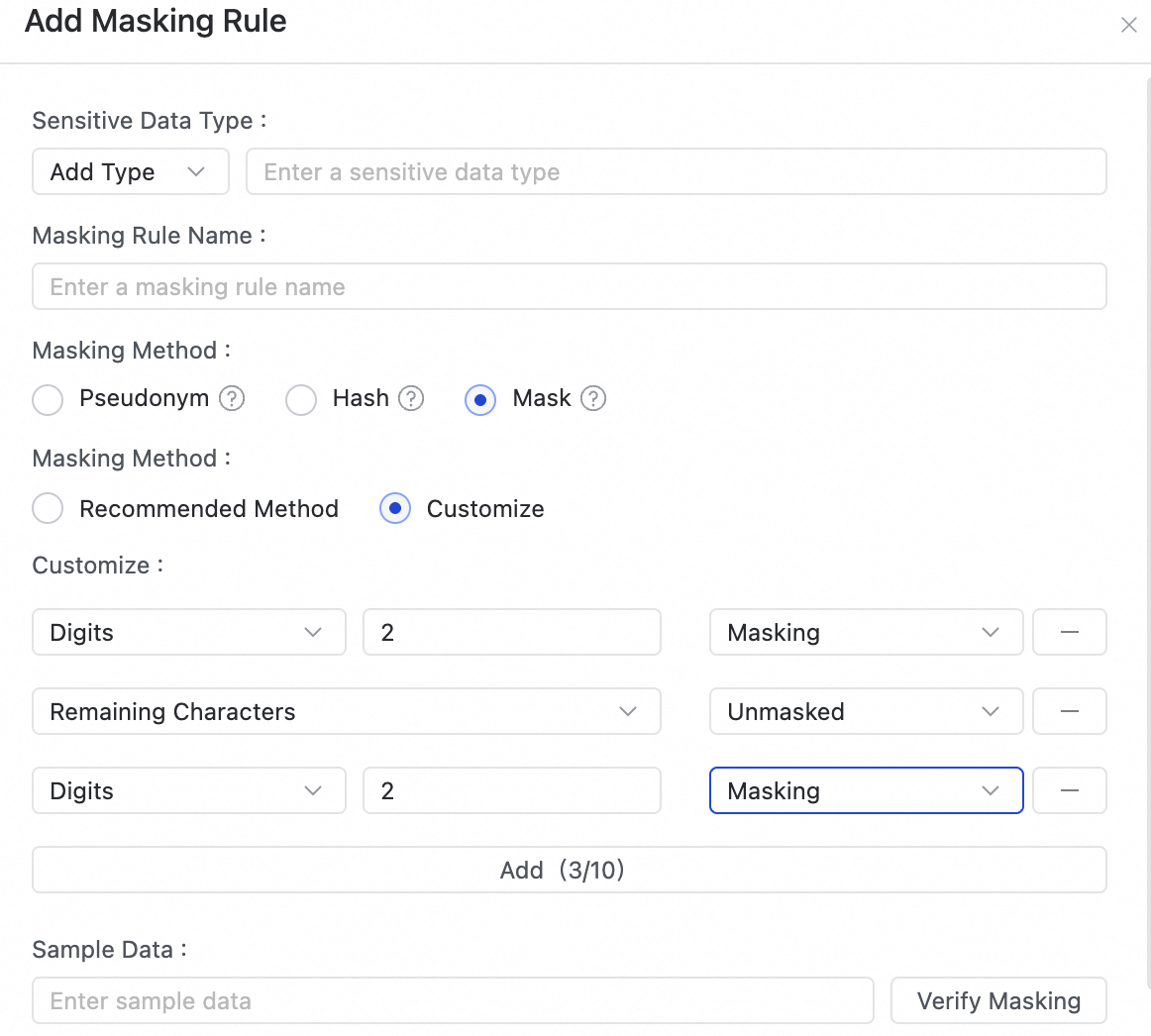
Icon Description ① Select Digits or Remaining Digits ② Enter a value from 1 to 100 ③ Select Mask or Do Not Mask Examples:
Configuration Result Mask the first three digits; do not mask the remaining digits ***12345678Mask the last three digits; do not mask the remaining digits 13812345***Preserve the first three and last three digits; mask all digits in the middle 138*****678
-
-
Test the masking rule: Enter sample data and click Test. The output appears in the Data Masking Effect section. Verify the result looks correct before saving.
-
Click Determine to save the masking rule.
-
Step 3: Verify the output
After configuring the Upstream Field and Data Masking Rule for each field, click Preview Data Output. Review the preview to confirm the masked results meet your requirements before running the task.