Database Autonomy Service (DAS) scans your MySQL, PolarDB for MySQL, and PolarDB-X 2.0 instances for five categories of security risk—weak passwords, open whitelists, disabled SSL, missing backups, and absent audit logs—and assigns each finding a color-coded severity level so you can prioritize remediation without manually auditing every instance.
Background information
The Verizon 2023 report indicates that approximately 50% of database breaches are related to weak passwords and dictionary attacks.
A report from the Cyberspace Administration of China reveals that thousands of domestic databases were exposed to unauthorized access and weak password risks in 2023, with 11.3% of 8,000 database instances identified as problematic.
These issues include weak password vulnerabilities and unchanged default administrator passwords. Database instances that are exposed to the Internet face higher risks from weak passwords.
Limitations
Supported regions
| Deployment | Regions |
|---|---|
| Alibaba Cloud public cloud | China (Hangzhou), China (Shanghai), China (Qingdao), China (Beijing), China (Shenzhen), China (Heyuan), China (Zhangjiakou), China (Hohhot), China (Chengdu), China (Guangzhou), China (Ulanqab), Indonesia (Jakarta), US (Virginia), US (Silicon Valley), Japan (Tokyo), Germany (Frankfurt), UK (London), Philippines (Manila), Malaysia (Kuala Lumpur), Singapore, and China (Hong Kong) |
| Alibaba Finance Cloud | China East 1 Finance, China East 2 Finance, China North 2 Finance (invitational preview), and China South 1 Finance |
Supported database engines
MySQL, PolarDB for MySQL, and PolarDB-X 2.0.
Backup detection is not supported for PolarDB-X 2.0 instances.
How it works
Each inspection scans the selected instances across five security areas:
| Check area | What is checked |
|---|---|
| Database configuration | Password policy complexity, such as strong password enforcement for ApsaraDB RDS for MySQL |
| Network configuration | IP whitelist rules and SSL certificate status |
| Access control | Weak password detection |
| Storage pool | Backup recency |
| Post-event security | Whether the audit log feature is enabled |
Check mechanism: Immediate check allows you to manually initiate a specific compliance check.
Weak password detection uses a dictionary library of tens of millions of common weak passwords found on the Internet, and works with the cloud security team to identify new weak passwords. It supports batch detection across multiple accounts and triggers alerts when weak passwords are found.
Inspection results are color-coded: red (danger), yellow (warning), and green (safe).
Scans use a lightweight data collection agent and do not affect database performance. Scans are automatically delayed during peak business hours.
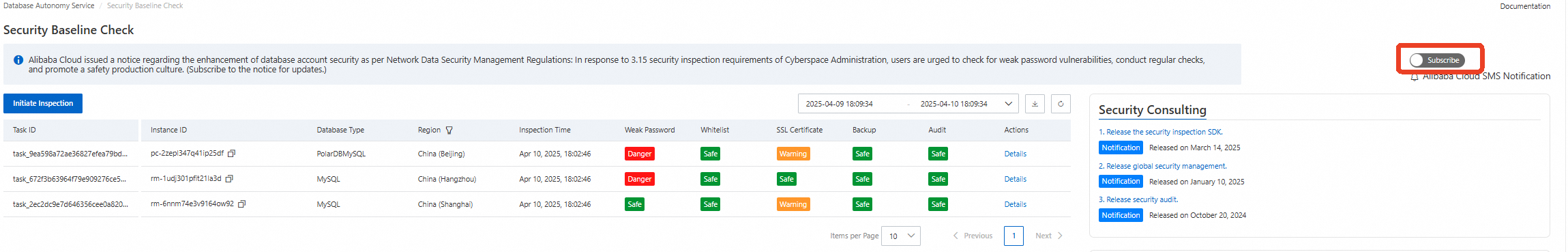
Run a security baseline check
Prerequisites
Before you begin, make sure you have:
Access to the DAS console
At least one MySQL, PolarDB for MySQL, or PolarDB-X 2.0 instance in a supported region
Initiate an inspection
Log on to the DAS console.
In the left-side navigation pane, choose Security Center > Security Baseline Check.
Click Initiate Inspection. In the dialog box, select the instances to inspect, click the
 icon to move them to the Selected Instances section, and then click OK.
icon to move them to the Selected Instances section, and then click OK.Inspection duration varies from a few minutes to tens of minutes, depending on the number and complexity of the selected instances.
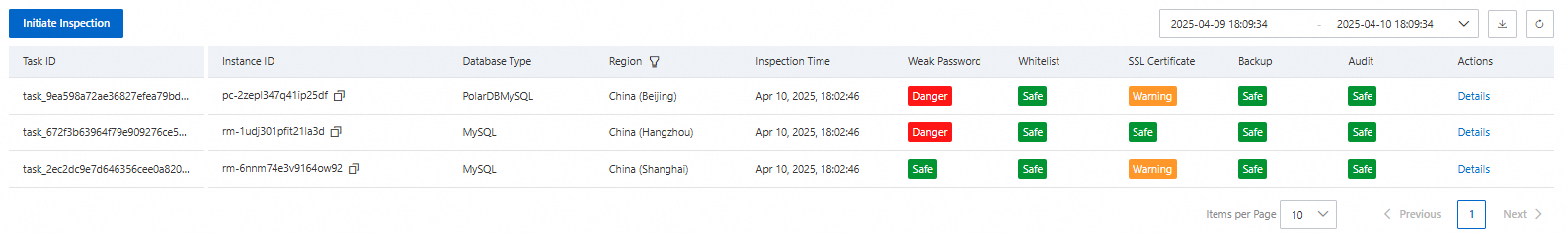
Review inspection results
After the inspection completes, return to the Security Baseline Check page. Each instance appears as a single row with color-coded results.
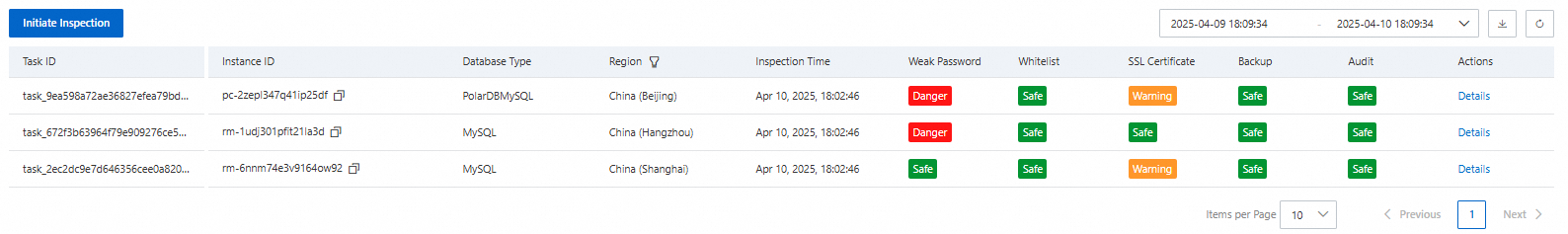
The table below describes each check item, its risk levels, and remediation steps.
| Check item | Danger | Warning | Safe | Remediation |
|---|---|---|---|---|
| Weak password | Weak passwords detected | N/A | No weak passwords detected | Set a password that is 8–32 characters long and contains at least three of the following character types: uppercase letters, lowercase letters, digits, and special characters (! @ # $ % ^ & * ( ) _ + - =). For ApsaraDB RDS for MySQL, install validate_password to enforce the policy, then run SHOW VARIABLES LIKE 'validate_password%' to confirm it is active. Reset passwords: RDS MySQL, PolarDB-X 2.0, PolarDB MySQL. |
| Whitelist | 0.0.0.0/0 in the whitelist, allowing all IP addresses | A large public CIDR block /8 is configured | No high-risk whitelist configuration detected | Remove unnecessary IP addresses from the whitelist. For internet-facing databases, allow only trusted IP addresses and CIDR blocks. |
| SSL certificate | N/A | SSL is disabled | SSL is enabled | Enable SSL encryption for all internet-facing databases to protect data in transit from interception and tampering. |
| Backup | No backup sets generated in the previous seven days | Backup sets generated within the previous two to seven days | Backup sets generated within the previous day | Schedule regular backups—daily or weekly—based on your business requirements. If no automatic backup policy is configured and no backups are generated for seven consecutive days, the instance is marked as Danger. PolarDB-X 2.0 is not supported. |
| Audit | N/A | Audit log feature is disabled | Audit log feature is enabled | Enable the audit log feature to support compliance tracking and real-time security risk detection. |
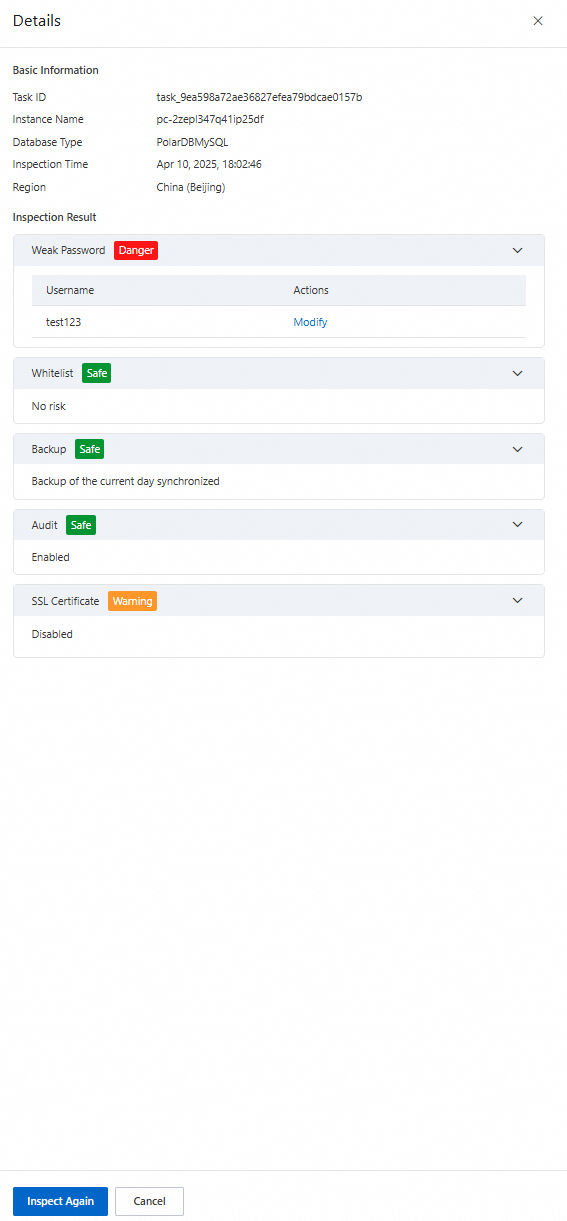
View inspection details
Find the inspection task in the list and click Details in the Actions column to see a per-check breakdown.
In the Details panel, click Inspect Again to rerun the inspection for that instance.
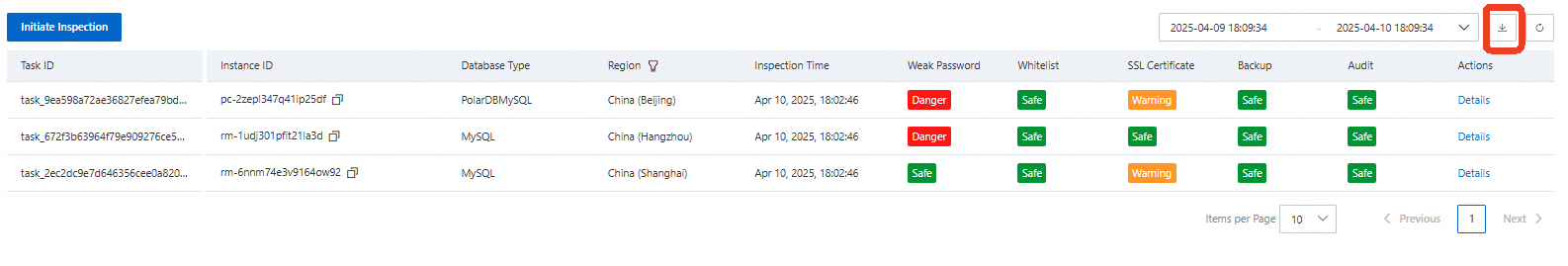
Download results
Click the ![]() icon in the upper-right corner of the Security Baseline Check page to download the inspection results.
icon in the upper-right corner of the Security Baseline Check page to download the inspection results.
Subscribe to security notifications
Turn on the Subscribe switch in the upper-right corner to receive security notifications. After you enable this, Alibaba Cloud sends alerts via internal messages and SMS when:
A security threat is received or discovered.
Regulatory authorities issue new compliance requirements.
FAQ
Does the security baseline check affect database performance?
No. The detection process uses a lightweight data collection agent. Scans are automatically delayed during peak business hours to minimize disruption.
Get support
Join the DingTalk group 58255008752 for technical support.