By default, Resource Access Management (RAM) users and RAM roles do not have permissions to call the OpenAPI of Alibaba Cloud services. Grant system policies or custom policies to RAM users or RAM roles before they can call Container Service for Kubernetes (ACK) OpenAPI operations. This topic describes how to grant cluster-level and cloud resource-level permissions to RAM users and RAM roles.
Grant permissions using system policies
System policies are predefined permission policies that grant read or write access to global resources. Use system policies for quick authorization when a RAM user or RAM role requires operations management permissions on all clusters under your Alibaba Cloud account.
Full-access permissions in system policies pose high security risks. Grant them with caution.
An Alibaba Cloud account has full administrative permissions over all resources in the account. Alternatively, you can create a RAM user and grant the AdministratorAccess permission to designate it as an account administrator. This administrator can manage all cloud resources within the account. For more information, see Create a RAM user as an account administrator.
Log on to the RAM console as a RAM administrator.
In the left-side navigation pane, choose .
On the Users page, find the required RAM user, and click Add Permissions in the Actions column.

You can also select multiple RAM users and click Add Permissions in the lower part of the page to grant permissions to the RAM users at a time.
In the Grant Permissions panel, grant permissions to the RAM user.
Configure the Resource Scope parameter.
Account: The authorization takes effect on the current Alibaba Cloud account.
Resource Group: The authorization takes effect on a specific resource group.
ImportantIf you select Resource Group for the Resource Scope parameter, make sure that the required cloud service supports resource groups. For more information, see Services that work with Resource Group. For more information about how to grant permissions on a resource group, see Use a resource group to restrict a RAM user to managing only specific ECS instances.
Configure the Principal parameter.
The principal is the RAM user to which you want to grant permissions. The current RAM user is automatically selected.
Select the system policies to grant.
Click Grant Permissions.
Click Close.
Grant permissions using custom policies
Custom policies provide fine-grained access control over cloud resources. Use custom policies when you need to:
Restrict permissions to specific clusters
Implement API-level permission control for SDK-based development
Control access based on specific cluster IDs
Before you create a custom policy, familiarize yourself with policy language structure and syntax. For more information, see Policy elements.
Step 1: Create a custom policy
Log on to the RAM console as a RAM user who has administrative rights.
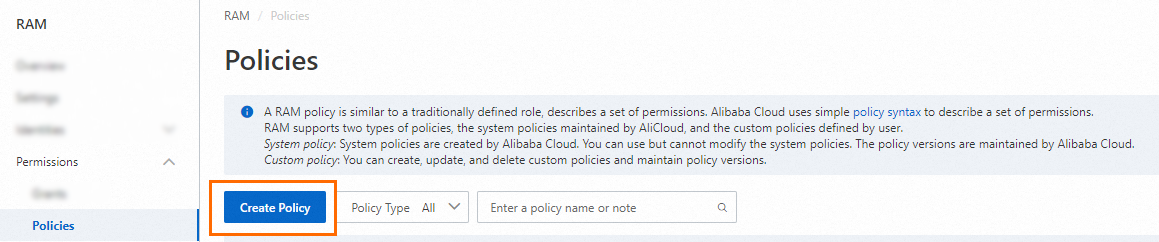
In the left-side navigation pane, choose .
On the Policies page, click Create Policy.
On the Create Access Policy page, click the Script Editor tab and enter the policy document.
Replace
YOUR_CLUSTER_IDwith the ID of the target cluster.{ "Statement": [ { "Action": [ "cs:Get*", "cs:List*", "cs:Describe*", "cs:ScaleCluster", "cs:DeleteCluster" ], "Effect": "Allow", "Resource": [ "acs:cs:*:*:cluster/YOUR_CLUSTER_ID" ] } ], "Version": "1" }Parameter
Description
Action
The permissions to grant. All actions support the wildcard character (*).
Resource
Grant permissions to a single cluster
"Resource": [ "acs:cs:*:*:cluster/YOUR_CLUSTER_ID" ]Grant permissions to multiple clusters
"Resource": [ "acs:cs:*:*:cluster/YOUR_CLUSTER_ID_1", "acs:cs:*:*:cluster/YOUR_CLUSTER_ID_2" ]Grant permissions to all clusters
"Resource": [ "*" ]
On the Create Policy page, click OK.
In the Create Policy dialog box, enter a Policy Name and Description, and then click OK.
Step 2: Grant the custom policy to a RAM user or RAM role
The procedure for granting a custom policy is the same as for granting a system policy. When you select a policy, choose the custom policy that you created. For more information, see Grant permissions using system policies.
Custom policy authorization examples
Example 1: Grant read-only permissions to a specific cluster
{
"Statement": [
{
"Action": [
"cs:Get*",
"cs:List*",
"cs:Describe*"
],
"Effect": "Allow",
"Resource": [
"acs:cs:*:*:cluster/YOUR_CLUSTER_ID"
]
}
],
"Version": "1"
}Example 2: Grant read permissions to a specific OSS bucket
Replace YOUR_OSS_BUCKET_NAME with the name of the target OSS bucket.{
"Version": "1",
"Statement": [
{
"Effect": "Allow",
"Action": [
"oss:ListBuckets",
"oss:GetBucketStat",
"oss:GetBucketInfo",
"oss:GetBucketTagging",
"oss:GetBucketAcl"
],
"Resource": "acs:oss:*:*:*"
},
{
"Effect": "Allow",
"Action": [
"oss:ListObjects",
"oss:GetBucketAcl"
],
"Resource": "acs:oss:*:*:YOUR_OSS_BUCKET_NAME"
},
{
"Effect": "Allow",
"Action": [
"oss:GetObject",
"oss:GetObjectAcl"
],
"Resource": "acs:oss:*:*:YOUR_OSS_BUCKET_NAME/*"
}
]
}Example 3: Grant permissions for OpenAPI operations that do not support cluster-level restrictions
Some OpenAPI operations, such as DescribeEvents, do not support cluster-level authorization. Do not specify a cluster ID in the Resource element for these operations.
RAM access policy before modification | RAM access policy after modification |
| |
What to do next
After you grant RAM authorization, configure RBAC authorization to access Kubernetes resources within the cluster. For more information, see Use RBAC to authorize operations on resources in a cluster.
To improve the security of applications in an ACK cluster that access other Alibaba Cloud services, configure RAM permissions for a ServiceAccount to isolate pod permissions using RRSA. For more information, see Use RRSA to configure RAM permissions for a ServiceAccount and isolate pod permissions.
For more information about fine-grained RAM authorization, see Implement fine-grained permission management using tags and Manually converge the permissions of the Worker RAM role for an ACK managed cluster.
For help with authorization issues, see Authorization management FAQ.