The Secure Sockets Layer (SSL) encryption feature of ApsaraDB RDS for SQL Server is used to encrypt data in transit. This feature is suitable for scenarios that require compliance and security of connections over an internal network or the Internet. This feature allows you to use certificates that are provided by Alibaba Cloud or custom certificates to encrypt data in transit. This feature also allows you to perform forceful SSL encryption on connections that are established to the internal endpoint of your RDS instance. This ensures the confidentiality of data in transit.
Feature description
The SSL encryption feature can be used to encrypt data that is transmitted between RDS instances and clients. This prevents data from being eavesdropped, intercepted, or tampered with by third parties.
If you enable the SSL encryption feature, you can determine whether to perform forceful SSL encryption on connections that are being established between RDS instances and clients.
When you enable the SSL encryption feature for your RDS instance, a server certificate, a public key, and a private key are generated.
When an encrypted connection is established, the system sends the server certificate, including the public key, to the client. The client encrypts the generated symmetric key by using the received public key. Then, the system uses the private key to decrypt the symmetric key. This way, the RDS instance and the client use the symmetric key to encrypt and decrypt data. This ensures the confidentiality of communication. The client can also use the certificate authority (CA) certificate to verify the received server certificate to confirm the identity of the RDS instance and prevent man-in-the-middle attacks.
Transport Layer Security (TLS) is the direct successor to SSL. In this topic, SSL refers to TLS and SSL.
ApsaraDB RDS for SQL Server supports TLS 1.0, TLS 1.1, and TLS 1.2.
Prerequisites
Before you use a custom key for encryption, make sure that the following requirements are met:
Object Storage Service (OSS) is activated. For more information, see Activate OSS.
The service account of ApsaraDB RDS is authorized by using your Alibaba Cloud account to access the OSS bucket.
The custom certificate is in the
PFXformat and is uploaded to an OSS bucket.For more information, see Get started by using the OSS console, Multipart upload, and Common operations.
Usage notes
An SSL certificate remains valid for one year. Before the used SSL certificate expires, you must update the validity period of the SSL certificate. If you do not update the validity period of the SSL certificate, your application or client that uses encrypted network connections cannot connect to your RDS instance. For more information about how to update the validity period of an SSL certificate, see Update the validity period of the SSL certificate.
When you enable or disable the SSL encryption feature or update the SSL certificate for your RDS instance, the RDS instance restarts. The RDS instance is unavailable for a few minutes during the restart. Therefore, we recommend that you perform these operations during off-peak hours.
SSL encryption may cause a significant increase in CPU utilization. We recommend that you enable the SSL encryption feature only if you need to encrypt the connections to the public endpoint of your RDS instance.
Limits
The SSL encryption feature is not supported by serverless RDS instances. For more information, see Serverless ApsaraDB RDS for SQL Server instances.
The SSL encryption feature is not supported for the connections to the read/write splitting endpoint of your RDS instance. For more information about the feature, see Enable read/write splitting by enabling the read-only routing endpoint.
If the SSL encryption feature is enabled for your RDS instance, you cannot upgrade the major engine version, update the minor engine version, create a temporary RDS instance that runs a later major engine version than your RDS instance, and migrate your RDS instance across zones. For more information, see Upgrade the major engine version, Update the minor engine version, Create a temporary RDS instance that runs the required SQL Server version, and Migrate an ApsaraDB RDS for SQL Server instance across zones.
1. Enable the SSL encryption feature for your RDS instance
Log on to the ApsaraDB RDS console and go to the Instances page. In the top navigation bar, select the region in which the RDS instance resides. Then, find the RDS instance and click the instance ID.
In the left-side navigation pane, click Data Security.
On the SSL tab, turn on Disabled.
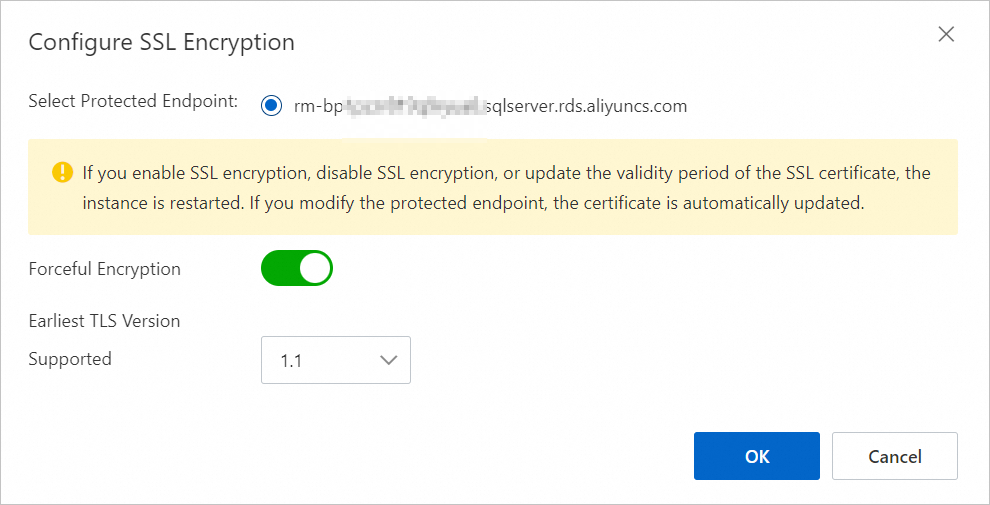
In the Configure SSL dialog box, select an encryption method and configure the settings.
Use keys automatically generated by Alibaba Cloud
Parameter
Required
Description
Select Protected Endpoint:
Yes
Select the endpoint for which you want to enable the SSL encryption feature. You can encrypt connections that are established to the internal or public endpoint of the RDS instance based on your business requirements. You cannot encrypt both types of connections.
NoteIf you want to encrypt connections that are established to the public endpoint of the RDS instance, make sure that you have applied for a public endpoint. For more information, see Apply for or release a public endpoint.
Forceful Encryption
No
Specify whether to support forceful SSL encryption. Forceful SSL encryption is supported only on connections that are established to the internal endpoint of the RDS instance. After you turn on Forceful Encryption, you do not need to upload the CA certificate, and non-encrypted connections are not supported.
NoteYou can enable this feature only for RDS instances that reside in virtual private clouds (VPCs). For more information, see Change the network type.
Forceful SSL encryption is not supported on connections that are established to the public endpoint of the RDS instance. When connections that are established to the internal endpoint and public endpoint of the RDS instance exist, if you want to turn on Forceful Encryption for connections established to the internal endpoint of the RDS instance, you must release the public endpoint first. For more information, see Apply for or release a public endpoint.
Earliest TLS Version Supported
No
Select the minimum TLS version that is supported. Valid values: 1.0, 1.1, and 1.2.
For example, if you set this parameter to 1.1, the server only accepts connections over TLS 1.1 and TLS 1.2 protocols.
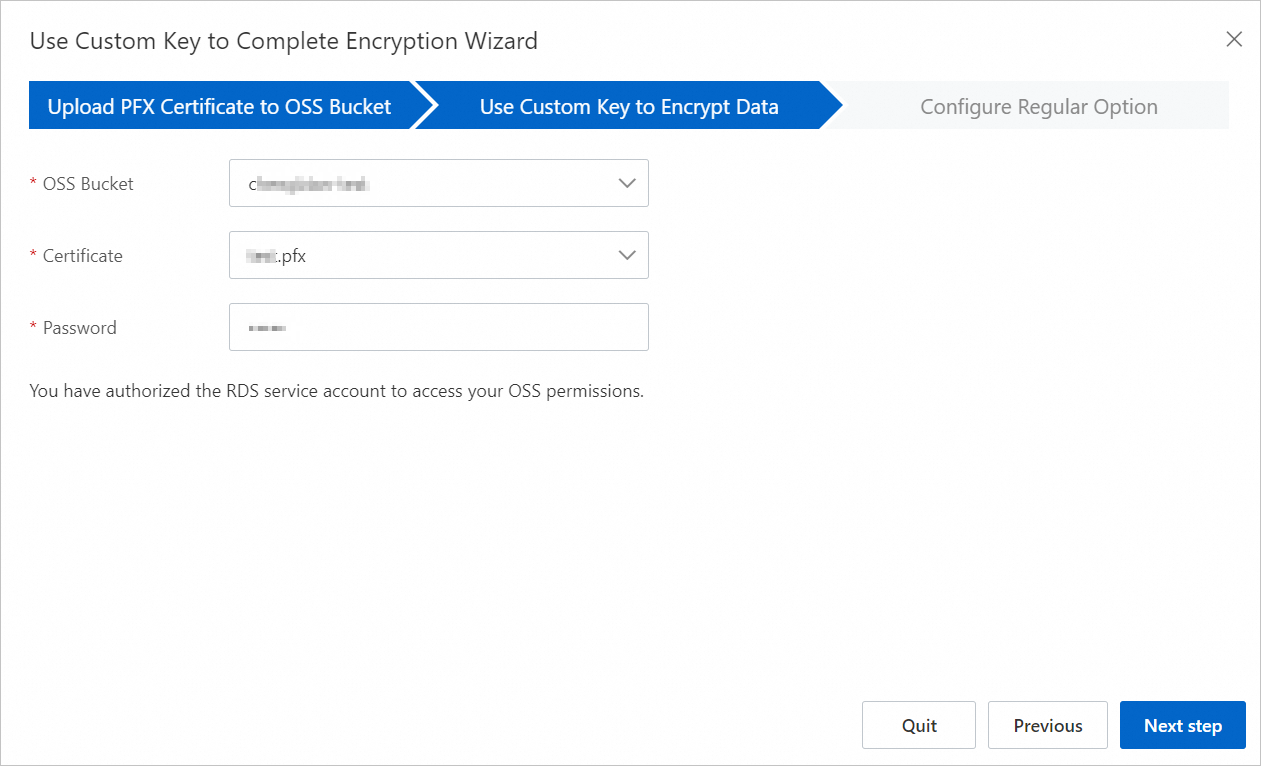
Use custom keys for encryption
NoteBefore you use a custom key for encryption, make sure that the requirements described in Prerequisites are met.
In the Upload PFX format certificate to OSS step, click Next step.
In the Use custom key encryption step, configure the required parameters and click Next step. The following table describes the parameters.
Parameter
Description
OSS Bucket
Select the OSS bucket where the certificate resides.
Certificate
Select the required
PFXcertificate.Password
Enter the certificate password.
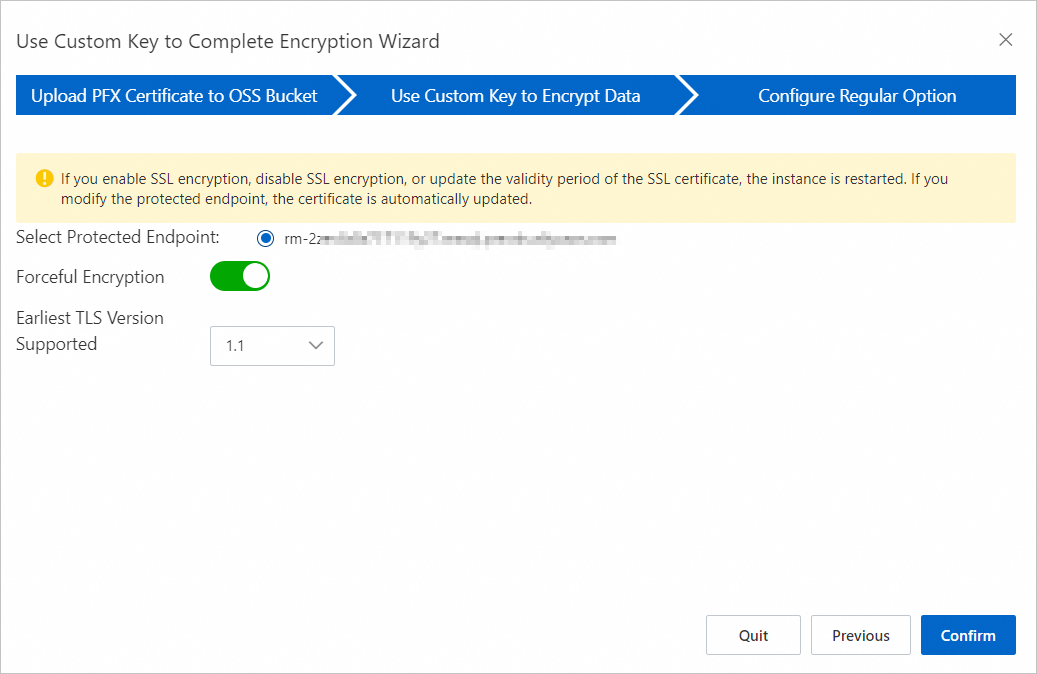
In the Set General Options step, configure the following parameters.
Parameter
Required
Description
Select Protected Endpoint:
Yes
Select the endpoint for which you want to enable the SSL encryption feature. You can encrypt connections that are established to the internal or public endpoint of the RDS instance based on your business requirements. You cannot encrypt both types of connections.
NoteIf you want to encrypt connections that are established to the public endpoint of the RDS instance, make sure that you have applied for a public endpoint. For more information, see Apply for or release a public endpoint.
Forceful Encryption
No
Specify whether to support forceful SSL encryption. Forceful SSL encryption is supported only on connections that are established to the internal endpoint of the RDS instance. After you turn on Forceful Encryption, you do not need to upload the CA certificate, and non-encrypted connections are not supported.
NoteYou can enable this feature only for RDS instances that reside in virtual private clouds (VPCs). For more information, see Change the network type.
Forceful SSL encryption is not supported on connections that are established to the public endpoint of the RDS instance. When connections that are established to the internal endpoint and public endpoint of the RDS instance exist, if you want to turn on Forceful Encryption for connections established to the internal endpoint of the RDS instance, you must release the public endpoint first. For more information, see Apply for or release a public endpoint.
Earliest TLS Version Supported
No
Select the minimum TLS version that is supported. Valid values: 1.0, 1.1, and 1.2.
For example, if you set this parameter to 1.1, the server only accepts connections over TLS 1.1 and TLS 1.2 protocols.
Click OK.
It takes about 1 minute to enable the SSL encryption feature. You can refresh the page to view the status of the RDS instance.
2. Download an SSL certificate
You can use the SSL encryption feature to connect to an RDS instance without a CA certificate. We recommend that you download and use the CA certificate. You can use the CA certificate to verify the server certificate that is received during an SSL handshake. This helps confirm the identity of the RDS instance and prevent man-in-the-middle attacks.
Log on to the ApsaraDB RDS console and go to the Instances page. In the top navigation bar, select the region in which the RDS instance resides. Then, find the RDS instance and click the instance ID.
In the left-side navigation pane, click Data Security.
On the SSL tab, click Download CA Certificate.
The file that you downloaded is a package that contains the following files:
P7B file: the SSL certificate file that is used for a Windows operating system.
PEM file: the SSL certificate file that is used for an operating system other than Windows or an application that is not run on Windows.
JKS file: the SSL certificate file that is stored in the Java-supported truststore. You can use this file to import the SSL certificate files from an SSL certificate chain into Java-based applications. The default password is apsaradb.
ImportantWhen you use the JKS file in JDK 7 or JDK 8, you must modify the following default JDK security configuration items in the
jre/lib/security/Java.securityfile on the host on which your application resides:jdk.tls.disabledAlgorithms=SSLv3, RC4, DH keySize < 224 jdk.certpath.disabledAlgorithms=MD2, RSA keySize < 1024If you do not modify these configurations, the following error is reported. In most cases, other similar errors are also caused by invalid Java security configurations:
javax.net.ssl.SSLHandshakeException: DHPublicKey does not comply to algorithm constraints
3. Configure an SSL certificate
After you enable the SSL encryption feature, you must configure an SSL certificate on your application or client. This topic provides an example on how to use SQL Server Management Studio (SSMS) to install an SSL certificate. If you want to use other applications or clients, see the related instructions.
3.1 Import the SSL certificate
In the search box in the lower-left corner of the desktop, enter certmgr.msc and open certmgr.msc.
In the certmgr dialog box, right-click Trusted Root Certification Authorities.
Choose .
Click Next.
In the Certificate Import Wizard dialog box, click Browse to import the SSL certificate that you download, and click Next. For more information about how to download an SSL certificate, see 2. Download an SSL certificate.
Select a directory to store the SSL certificate and click Next.
Click Finish and wait until the certificate is imported.
3.2 Configure SSMS
Open SSMS and click Options in the lower-right corner of the dialog box.
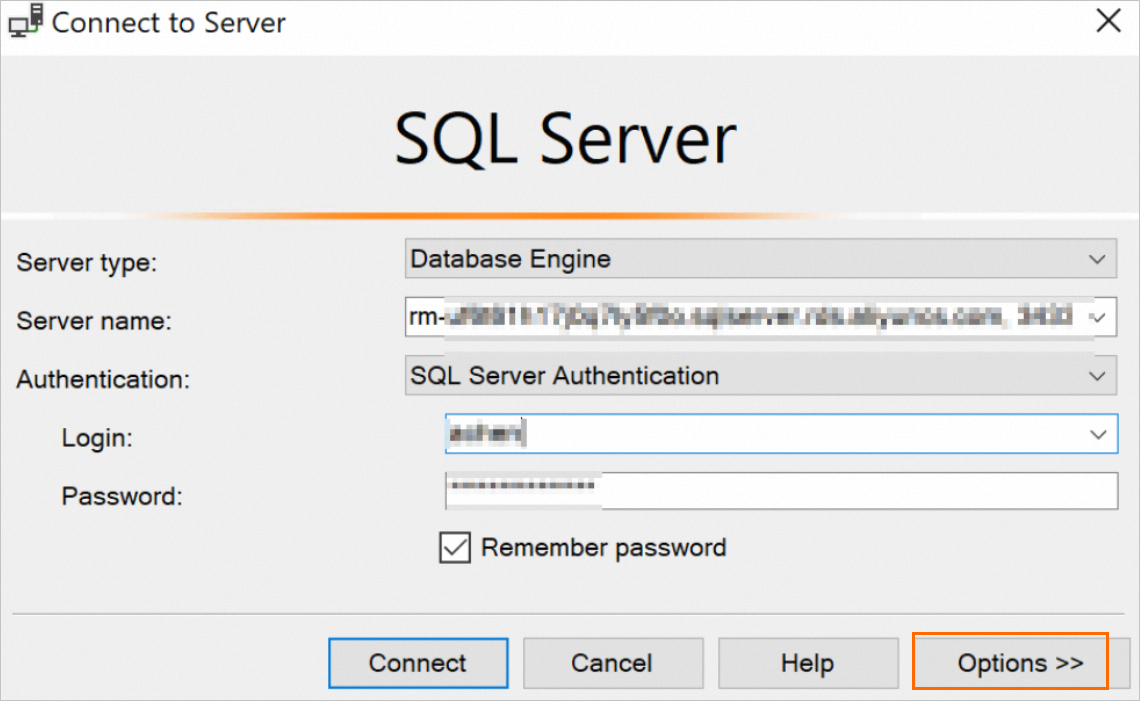
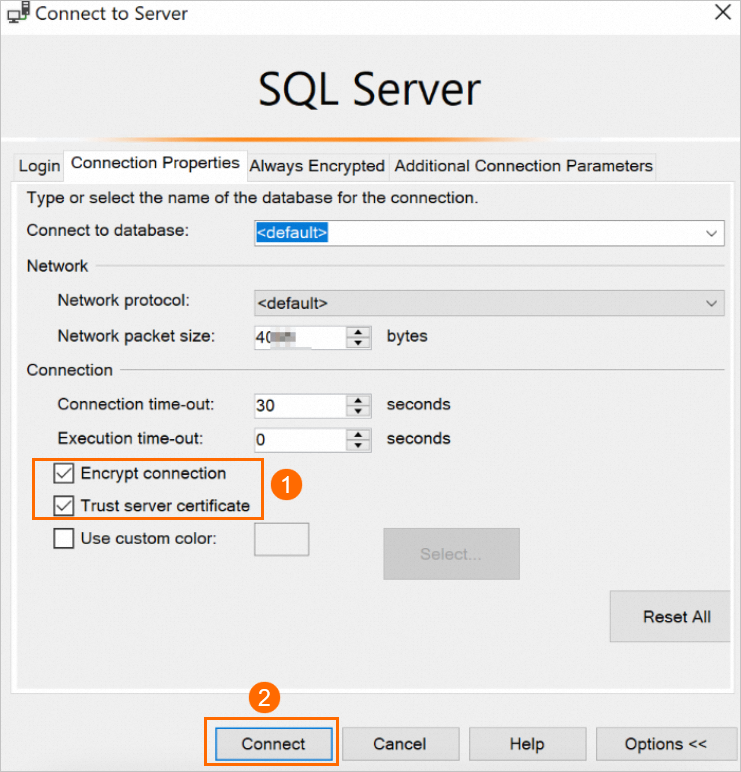
On the Connection Properties tab, select Encrypt connection and Trust server certificate, and click Connect.
Execute the following statement. If TRUE is returned, the connection is encrypted.
SELECT ENCRYPT_OPTION FROM SYS.DM_EXEC_CONNECTIONS WHERE SESSION_ID = @@SPID
Appendix: Sample code for connections over SSL
# -*- coding:utf-8 -*-
import ssl
import pyodbc
# Create an SSL context for establishing an SSL connection in Python.
context = ssl.create_default_context(purpose=ssl.Purpose.SERVER_AUTH, cafile="D:\ca\ApsaraDB-CA-Chain.pem")
# Establish a connection.
# SERVER specifies the IP address of the server on which the required database resides. DATABASE specifies the name of the database that you want to connect. UID specifies the username that is required to log on to the database. PWD specifies the password that is required to log on to the database. Encrypt specifies whether to enable SSL encryption. The value of yes indicates that SSL encryption is enabled.
conn = pyodbc.connect('DRIVER={ODBC Driver 17 for SQL Server};SERVER=rm-2zec********.sqlserver.rds.aliyuncs.com;DATABASE=master;UID=zhttest;PWD=zht****;Encrypt=yes', ssl=context)
cursor = conn.cursor()
cursor.execute('SELECT @@version')
rows = cursor.fetchall()
for row in rows:
print(row)
# Close the connection.
conn.close()using System;
using System.Data.SqlClient;
namespace SqlConnectionSSLExample
{
class Program
{
static void Main(string[] args)
{
// Establish a connection.
// Data Source specifies the IP address of the server on which the required SQL Server database resides. Initial Catalog specifies the name of the required database that you want to connect. User ID specifies the username that is required to connect to the database. Password specifies the password that is required to connect to the database. Encrypt specifies whether to enable SSL-encrypted transmission. The value of true indicates that SSL encryption is enabled.
string connectionString = "Data Source=rm-2ze********.sqlserver.rds.aliyuncs.com;Initial Catalog=master;User ID=zhttest;Password=zht****;Encrypt=true;";
using (SqlConnection connection = new SqlConnection(connectionString))
{
// Open the connection.
connection.Open();
try
{
// Execute an SQL statement.
SqlCommand cmd = new SqlCommand("SELECT @@version", connection);
string result = cmd.ExecuteScalar().ToString();
Console.WriteLine(result);
}
catch (Exception ex)
{
Console.WriteLine($"Error: {ex.Message}");
}
}
}
}
}Related operations
What to do next
Update the validity period of a certificate
An SSL certificate remains valid for one year. Before the used SSL certificate expires, you must update the validity period of the SSL certificate. If you do not update the validity period of the SSL certificate, your application or client that uses encrypted network connections cannot connect to your RDS instance. If an SSL certificate is about to expire, Alibaba Cloud notifies users who enable SSL encryption by using custom certificates by email and internal message. You can view internal messages on the Event Center page. Before an SSL certificate expires, you must update the validity period of the SSL certificate to ensure that your application or client can connect to your RDS instance.
Updating the validity period of an SSL certificate causes your RDS instance to restart. Proceed with caution when you update the validity period of the SSL certificate.
Log on to the ApsaraDB RDS console and go to the Instances page. In the top navigation bar, select the region in which the RDS instance resides. Then, find the RDS instance and click the instance ID.
In the left-side navigation pane, click Data Security.
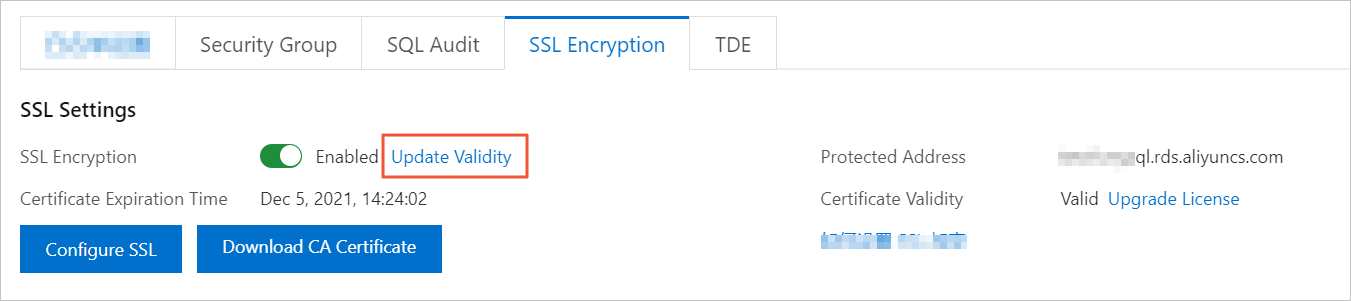
On the SSL tab, click Update Validity.
Disable the SSL encryption feature
When you disable the SSL encryption feature, your RDS instance restarts. In this case, the system triggers a primary/secondary switchover to reduce the impacts on your workloads. We still recommend that you disable the SSL encryption feature during off-peak hours.
After you disable the SSL encryption feature, access performance increases, but security decreases. We recommend that you disable the SSL encryption feature only in secure environments.
If you disable the SSL encryption feature, your application can connect to your RDS instance only over a non-SSL connection.
Go to the Instances page. In the top navigation bar, select the region in which the RDS instance resides. Then, find the RDS instance and click the ID of the instance.
In the left-side navigation pane, click Data Security.
On the page that appears, click the SSL tab.
Turn off SSL Encryption. In the message that appears, click OK.
View the details about connection encryption
In SQL Server, you can execute the following statements to check whether the SSL encryption feature is enabled for the current connection:
SELECT session_id,encrypt_option
FROM sys.dm_exec_connections;
GOIf the session ID of the current connection is returned when the sys.dm_exec_connections dynamic management view is queried and the value of the encrypt_option parameter is true, the SSL encryption feature is enabled for the connection.
FAQ
What are the impacts on my business if I do not renew an expired SSL certificate? Does an error occur on my RDS instance or is data security decreased?
If you do not update the expired SSL certificate, the RDS instance still runs as expected and no security risks occur. However, your application cannot establish encrypted connections to the RDS instance.