Sandboxed-Container runtime executes applications in lightweight virtual machines isolated from the rest of the system. This architecture establishes kernel-level isolation for application pods while maintaining strict environmental segregation from the host infrastructure. This mechanism effectively protects the host or other containers against attacks or vulnerabilities within the sandboxed container. In Container Service for Kubernetes (ACK), nodes are managed through node pools. This topic describes how to create and scale a node pool that runs in a sandboxed container.
Usage notes
Cluster versions: Supported only for ACK managed clusters and ACK dedicated clusters running Kubernetes 1.16 or later. To upgrade clusters, see Manually upgrade ACK clusters.
Operating system: Custom images are not supported by node pools that run in sandboxed containers.
Clusters below v1.30: Only Alibaba Cloud Linux 3 and Alibaba Cloud Linux 2 (EOL).
Clusters v1.30+: Only Alibaba Cloud Linux 3.
Instance specifications: Only ECS Bare Metal Instance families.
Network plugins:
Flannel (fully supported)
Terway (with restrictions): Exclusive ENI mode and DataPath V2 mode are unsupported.
Create a node pool in a sandboxed container
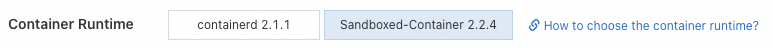
When you create a node pool, select Sandboxed-Container as the container runtime. For more information, see Create and manage a node pool.
Scale the node pool
Log on to the ACK console. In the left-side navigation pane, click Clusters.
On the Clusters page, find the cluster to manage and click its name. In the left-side navigation pane, choose .
Click Scale in the Actions column of the node pool that you want to manage. Select Manual for the Scaling Mode parameter, configure the Expected Nodes parameter, and submit the configurations according to the instructions on the page. After you scale out the node pool, the node pool is scaled out to the expected number of nodes.
References
To create an application that runs in sandboxed containers, see Create a stateless application by using a Deployment.
For more information about how to create clusters and node pools by calling API operations, see CreateCluster and CreateClusterNodePool.