Without access controls, O&M engineers can run any command, connect from any source IP, and log on to assets without oversight. Control policies let you enforce security boundaries on O&M operations in Bastionhost—blocking or requiring approval for high-risk commands, restricting protocol access, limiting source IP addresses, and requiring logon approval before engineers can reach assets.
Prerequisites
Before you begin, ensure that you have:
Step 1: Create a control policy
Log on to the Bastionhost console. In the top navigation bar, select the region where your bastion host resides.
In the bastion host list, find the bastion host you want to manage and click Manage.
In the left-side navigation pane, click Control Policies.
On the Control Policies page, click Create Control Policy.
Configure the parameters described below, then click Create Control Policy.
Priority
Valid values: 1–100. Default: 1 (highest priority).
When multiple policies share the same priority, the most recently created policy takes precedence. When a command control policy and a command approval policy both match the same command, the enforcement order is: reject > allow > approve.
Command policy
Host command policy
Note Host command policies apply to Linux hosts only.
Use Commands That Require Control to specify which commands are allowed or blocked for the users and hosts the policy covers:
(Blacklist) Listed commands are not allowed — Blocks the listed commands. You can leave the field blank. Use this mode when most commands are acceptable and you only need to block a known set of high-risk operations.
(Whitelist) Only listed commands are allowed — Allows only the listed commands. The field is required. Use this mode when you need strict control and can enumerate all permitted commands.
Use Commands That Require Approval to flag commands that need administrator review before running. When a user runs a flagged command, it is held until an administrator approves or rejects it in the Bastionhost console. For details, see Review commands.
Note The command control policy (blacklist/whitelist) takes precedence over the command approval policy. A command blocked by the control policy is never sent for approval.
Recommended policies for host commands
The following table lists high-risk commands and the recommended policy for each.
| Command | Description | Recommended policy |
|---|
reboot | Restarts the system | Require approval |
restart | Restarts the system | Require approval |
shutdown | Shuts down the system | Require approval |
halt | Shuts down the system | Require approval |
poweroff | Shuts down the system | Require approval |
init 0 | Stops the system | Require approval |
pkill | Terminates multiple processes | Require approval |
kill | Terminates a single process | Require approval |
rm -rf | Recursively deletes directories without prompts | Require approval |
mount | Mounts a file system (virus replication risk) | Require approval |
umount | Unmounts a file system | Require approval |
parted | Partitions a file system | Require approval |
format | Formats the disk | Blacklist |
dd if=/dev/zero of=/dev/had | Clears the disk | Blacklist |
:(){:|:&};: | Creates a fork bomb | Blacklist |
(mv)(|.*)(/dev/null) | Moves a directory to /dev/null | Blacklist |
(wget)(|.*)(-O- | sh) | Downloads and immediately runs a file | Blacklist |
mkfs.ext3 * | Formats the disk | Blacklist |
dd if=/dev/random of=/dev/* | Writes random data to a block device | Blacklist |
Database command policy
Use Commands That Require Control to specify which database commands are allowed or blocked:
(Blacklist) Listed commands are not allowed — Blocks the listed commands. You can leave the field blank.
(Whitelist) Only listed commands are allowed — Allows only the listed commands. The field is required.
For Match Method, choose between SQL parsing and regular expression matching.
Protocol control
Configure RDP Options, SSH Options, and SFTP Options to define which operations the policy allows. For example, enabling File Upload lets users upload files during O&M sessions.
Avoiding channel lockout
Important Select at least one of SSH Channel or SFTP Channel. Clearing SSH Channel disables SSH-based logon for all accounts the policy covers—proceed with caution.
If Enable Only SFTP Permission is set for a host account, do not disable both SSH Channel and SFTP Channel in the control policy. Doing so prevents the host account from accessing the host through Bastionhost.
Access control
Control which source IP addresses can reach the assets the policy covers:
(Whitelist) Only listed IP addresses are allowed — Only the IPs in the IP Addresses field can connect. The field is required.
(Blacklist) Listed IP addresses are not allowed — The IPs in the IP Addresses field are blocked. You can leave the field blank.
Logon control
O&M Approval — When enabled, O&M engineers must submit an O&M application and wait for administrator approval before they can log on to assets. For details, see Review an O&M application.
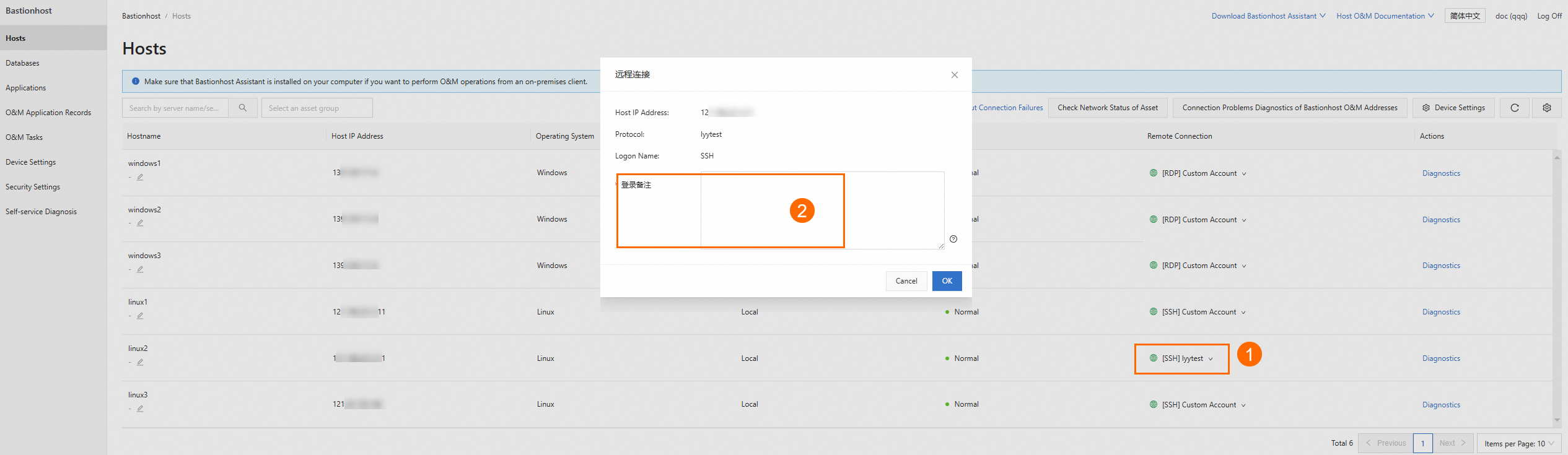
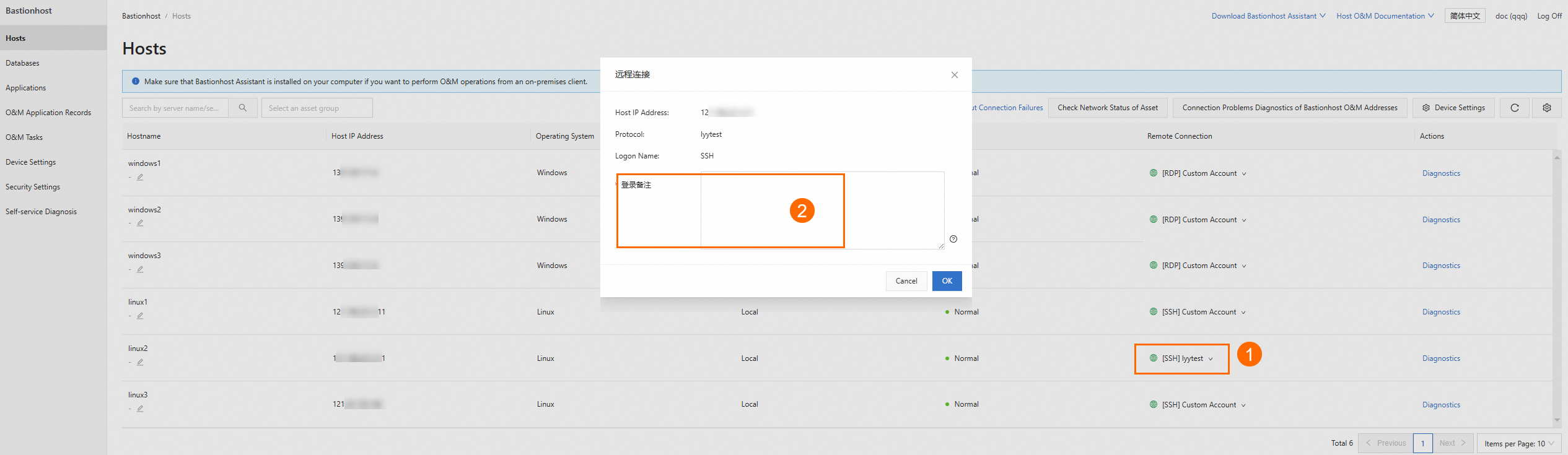
Logon Remarks — When enabled, O&M personnel must enter remarks before performing web page-based O&M, SSO-based O&M, or applying for O&M tokens. The following figure shows the logon remarks prompt in the O&M portal.
Step 2: Associate the policy with assets and users
A control policy has no effect until it is associated with both assets and users. On the Assets and Users to Which Policy Is Attached page, associate the control policy with assets and users for the policy to take effect.
Associate with assets
Choose one of the following options based on your scope:
| Option | When to use | Next step |
|---|
| Takes Effect on All Assets | Apply the policy to every asset account in the bastion host | No further selection needed |
| Takes Effect on Selected All Assets | Apply the policy to specific assets only | Select the assets, then choose Associate All Accounts or Associate Specific Accounts |
Note To apply a policy to multiple assets at once, add them to an asset group first, then associate the policy with the group.
Associate with users
Choose one of the following options: