Presto service can be connected to LDAP for user password authentication. You only need to connect the Coordinator node to LDAP. The main steps are as follows:
1. Configure ApacheDS, and enable LDAPS
2. Create user information in ApacheDS
3. Configure Presto Coordinator, and restart it for it to work.
4. Verify the configuration
The relevant steps are described in detail below.
1. Create a keystore for the ApacheDS server, where all passwords are set to '123456 ':
## Create a keystore
> cd /var/lib/apacheds-2.0.0-M24/default/conf/
> keytool -genkeypair -alias apacheds -keyalg RSA -validity 7 -keystore ads.keystore
Enter the keystore password:
Re-enter new password:
What is your first and last name?
[Unknown]: apacheds
What is the name of your organizational unit?
[Unknown]: apacheds
What is the name of your organization?
[Unknown]: apacheds
What is the name of your City or Locality?
[Unknown]: apacheds
What is the name of your State or Province?
[Unknown]: apacheds
What is the two-letter country code for this unit?
[Unknown]: CN
Is CN=apacheds, OU=apacheds, O=apacheds, L=apacheds, ST=apacheds, C=CN correct?
[no]: yes
Enter key password for <apacheds>
(RETURN if same as keystore password):
Re-enter new password:
Warning:
The JKS keystore uses a proprietary format. It is recommended to migrate to PKCS12, which is an industry standard format, using "keytool -importkeystore -srckeystore ads.keystore -destkeystore ads.keystore -deststoretype pkcs12".
## Modify the file user, otherwise, ApacheDS has no permission to read the file
> chown apacheds:apacheds ./ads.keystore
## Export the certificate.
# Password is required. The password is the value set in the previous step, which is 123456
> keytool -export -alias apacheds -keystore ads.keystore -rfc -file apacheds.cer
Enter the keystore password:
Certificate stored in file <apacheds.cer>
Warning:
The JKS keystore uses a proprietary format. It is recommended to migrate to PKCS12, which is an industry standard format, using "keytool -importkeystore -srckeystore ads.keystore -destkeystore ads.keystore -deststoretype pkcs12".
## Import the certificate into the system certificate library for self-authentication
>Keytool-import-file apacheds. cer-alias apacheds-keystore/usr/lib/jvm/java-1.8.0/Jre/lib/security/cacerts2. Modify configuration and enable LDAPs
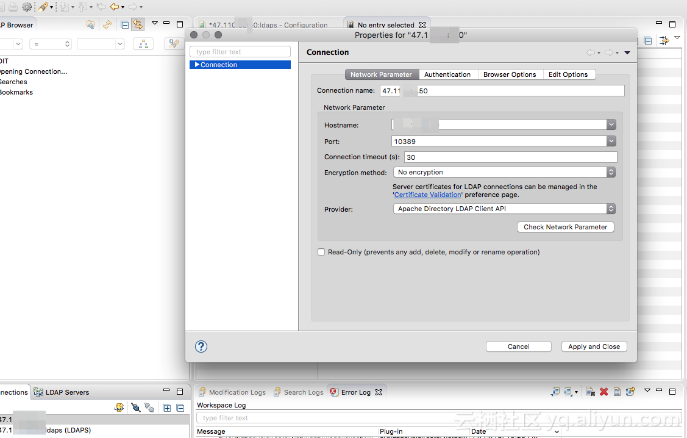
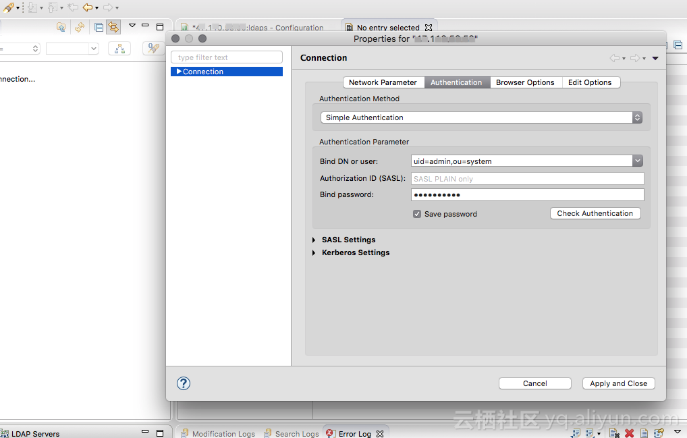
Open ApacheDS Studio, and link to the ApacheDS service on the cluster:
After linking, open the configuration page, enable LDAPS, set the keystore created in the first step to the relevant configuration, and save (ctrl+s).
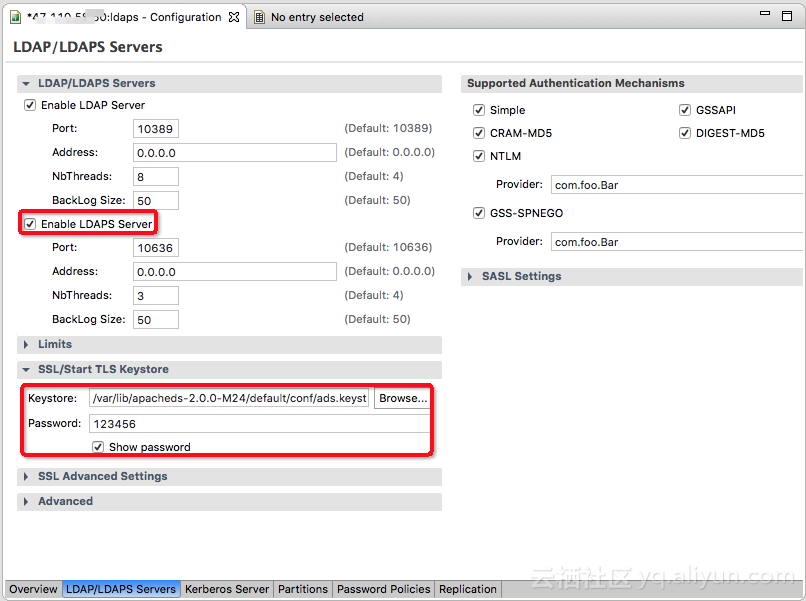
3. Restart ApacheDS
Log on to the cluster and run the following command to restart ApacheDS. At this point, LDAPS is started with service port 10636.
ApacheDS Studio has a bug. When you test the LDAPS service connection on the connection property page, a handshake failure is reported. This is mainly caused by the internal default timeout being too short and does not affect actual use.
> service apacheds-2.0.0-M24-default restartIn this example, create related users under DN: dc=hadoop,dc=apache,dc=org.
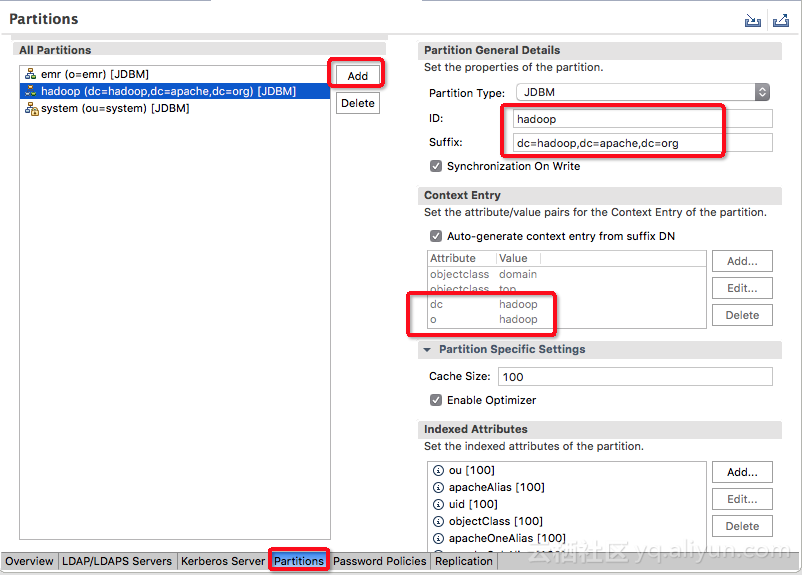
1. Create a partition dc=hadoop,dc=apache,dc=org
Open the configuration page, make the following configuration, and press ctrl+s to save. Restart ApacheDS for it to take effect.
2. Create the users
Log on to the cluster and create the following file: /tmp/users.ldif
# Entry for a sample people container
# Please replace with site specific values
dn: ou=people,dc=hadoop,dc=apache,dc=org
objectclass:top
objectclass:organizationalUnit
ou: people
# Entry for a sample end user
# Please replace with site specific values
dn: uid=guest,ou=people,dc=hadoop,dc=apache,dc=org
objectclass: top
objectclass: person
objectclass: organizationalPerson
objectclass: inetOrgPerson
cn: Guest
sn: User
uid: guest
userPassword: guest-password
# Entry for sample user admin
dn: uid=admin,ou=people,dc=hadoop,dc=apache,dc=org
objectclass: top
objectclass: person
objectclass: organizationalPerson
objectclass: inetOrgPerson
cn: Admin
sn: Admin
uid: admin
userPassword: admin-password
# Entry for sample user sam
dn: uid=sam,ou=people,dc=hadoop,dc=apache,dc=org
objectclass: top
objectclass: person
objectclass: organizationalPerson
objectclass: inetOrgPerson
cn: sam
sn: sam
uid: sam
userPassword: sam-password
# Entry for sample user tom
dn: uid=tom,ou=people,dc=hadoop,dc=apache,dc=org
objectclass: top
objectclass: person
objectclass: organizationalPerson
objectclass: inetOrgPerson
cn: tom
sn: tom
uid: tom
userPassword: tom-password
# Create FIRST Level groups branch
dn: ou=groups,dc=hadoop,dc=apache,dc=org
objectclass: top
objectclass:organizationalUnit
ou: groups
description: generic groups branch
# Create the analyst group under groups
dn: cn=analyst,ou=groups,dc=hadoop,dc=apache,dc=org
objectclass: top
objectclass: groupofnames
cn: analyst
description:analyst group
member: uid=sam,ou=people,dc=hadoop,dc=apache,dc=org
member: uid=tom,ou=people,dc=hadoop,dc=apache,dc=org
# Create the scientist group under groups
dn: cn=scientist,ou=groups,dc=hadoop,dc=apache,dc=org
objectclass: top
objectclass: groupofnames
cn: scientist
description: scientist group
member: uid=sam,ou=people,dc=hadoop,dc=apache,dc=orRun the following command to import the users:
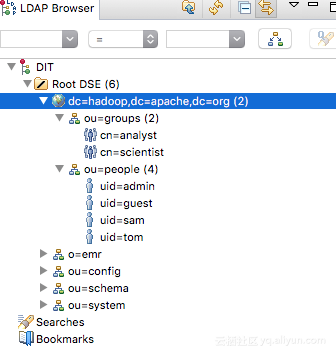
> ldapmodify -x -h localhost -p 10389 -D "uid=admin,ou=system" -w {password} -a -f /tmp/users.ldifOnce the execution is complete, the relevant users can be seen on ApacheDS Studio as follows:
This is mainly divided into two parts:
1. Enable Coordinator HTTPS
Create a keystore for Presto Coordinator
## Generate a keystore using the script that comes with EMR
## Keystore address: /etc/ecm/presto-conf/keystore
# Keystore password : ******
> expect /var/lib/ecm-agent/cache/ecm/service/PRESTO/0.208.0.1.2/package/files/tools/gen-keystore.expConfigure Presto Coordinator
Edit the /etc/ecm/presto-conf/config.properties file, and add the following:
http-server.https.enabled=true
http-server.https.port=7778
http-server.https.keystore.path=/etc/ecm/presto-conf/keystore
http-server.https.keystore.key=******2. Configure the authentication mode and access ApacheDS
Edit the /etc/ecm/presto-conf/config.properties file, and add the following:
http-server.authentication.type=PASSWORDEdit the jvm.config file, and add the following:
-Djavax.net.ssl.trustStore=/usr/lib/jvm/java-1.8.0/jre/lib/security/cacerts
-Djavax.net.ssl.trustStorePassword=changeitCreate the password-authenticator.properties file, and add the following:
password-authenticator.name=ldap
ldap.url=ldaps://emr-header-1.cluster-84423:10636
ldap.user-bind-pattern=uid=${USER},ou=people,dc=hadoop,dc=apache,dc=orgCreate the jndi.properties file, and add the following:
java.naming.security.principal=uid=admin,ou=system
java.naming.security.credentials={password}
java.naming.security.authentication=simplePackage the jndi.properties file into a jar package, and copy it to the Presto library file directory
> jar -cvf jndi-properties.jar jndi.properties
> cp ./jndi-properties.jar /etc/ecm/presto-current/lib/java.naming.security.principal=uid=admin,ou=system
java.naming.security.credentials={LDAP password}
java.naming.security.authentication=simple3. Restart Presto. At this point, all configurations are complete
Use presto cli to verify whether the configuration takes effect.
## Using the user ID sam, enter the correct password
> presto --server https://emr-header-1:7778 --keystore-path /etc/ecm/presto-conf/keystore --keystore-password ****** --catalog hive --schema default --user sam --password
Password: <correct password entered>
Presto:default> show schemas;
Schema
----------------------------------
tpcds_bin_partitioned_orc_5
tpcds_oss_bin_partitioned_orc_10
tpcds_oss_text_10
tpcds_text_5
tst
(5 rows)
Query 20181115_030713_00002_kp5ih, FINISHED, 3 nodes
Splits: 36 total, 36 done (100.00%)
0:00 [20 rows, 331B] [41 rows/s, 694B/s]
## Using the user ID sam, enter the wrong password
> presto --server https://emr-header-1:7778 --keystore-path /etc/ecm/presto-conf/keystore --keystore-password ****** --catalog hive --schema default --user sam --password
Password: <wrong password entered>
Presto:default> show schemas;
Error running command: Authentication failed: Access Denied: Invalid credentialsAlibaba Clouder - July 20, 2020
vboylin - May 10, 2019
Alibaba Cloud Community - February 8, 2023
Alibaba Cloud MaxCompute - June 24, 2019
Alibaba Cloud Data Intelligence - August 8, 2024
Alibaba Cloud Community - February 8, 2023
 Big Data Consulting for Data Technology Solution
Big Data Consulting for Data Technology Solution
Alibaba Cloud provides big data consulting services to help enterprises leverage advanced data technology.
Learn More Big Data Consulting Services for Retail Solution
Big Data Consulting Services for Retail Solution
Alibaba Cloud experts provide retailers with a lightweight and customized big data consulting service to help you assess your big data maturity and plan your big data journey.
Learn More ApsaraDB for HBase
ApsaraDB for HBase
ApsaraDB for HBase is a NoSQL database engine that is highly optimized and 100% compatible with the community edition of HBase.
Learn More E-Commerce Solution
E-Commerce Solution
Alibaba Cloud e-commerce solutions offer a suite of cloud computing and big data services.
Learn MoreMore Posts by vboylin
Dikky Ryan Pratama May 9, 2023 at 6:01 am
Thank you very much vboylin for sharing the information