Join us at the Alibaba Cloud ACtivate Online Conference on March 5-6 to challenge assumptions, exchange ideas, and explore what is possible through digital transformation.
By Hitesh Jethva, Alibaba Cloud Tech Share Author. Tech Share is Alibaba Cloud's incentive program to encourage the sharing of technical knowledge and best practices within the cloud community.
Tripwire is a free, open source host-based Intrusion Detection System (IDS) that can be used to detect if unauthorized filesystem changes occurred over time. Tripwire continuously monitor computer's filesystem, when an expected change occurs, such as upgrading a package, the baseline database can be updated to the new known-good state. Tripwire works by collecting detail information of your filesystem and stores this information to reference and validate the current state of the system. If changes are found between the known-good state and the current state, Tripwire will send an alert to you. The baseline and check behavior are controlled by a policy file, which specifies which files or directories to monitor, and which attributes to monitor on them, such as hashes, file permissions, and ownership. Tripwire allows the system admin to know immediately what was compromised and fix it.
In this tutorial, we will be installing and using Tripwire IDS on an Alibaba Cloud Elastic Compute Service (ECS) with Ubuntu 16.04.
First, log in to your Alibaba Cloud ECS Console. Create a new ECS instance, choosing Ubuntu 16.04 as the operating system with at least 2GB RAM. Connect to your ECS instance and log in as the root user.
Once you are logged into your Ubuntu 16.04 instance, run the following command to update your base system with the latest available packages.
apt-get update -yBy default, Tripwire is available in the Ubuntu 16.04 default repository. You can install it by just running the following command:
apt-get install tripwire -yDuring the installation, you'll be prompted with several messages with various options.
First, you will be asked to provide SMTP configuration. Select Internet Site and click OK to continue the installation.
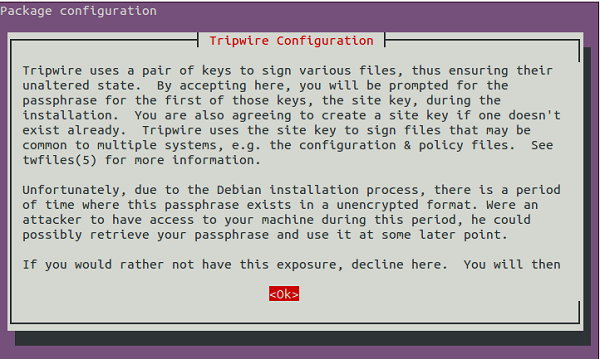
Here, you will be asked for Tripwire configuration agreement. Click OK. You will be redirected to site-key creation page.
Click Yes to create a site key passphrase.
Click Yes to rebuild the Tripwire configuration.
Click Yes to rebuild the Tripwire policy file. You should see the following page:
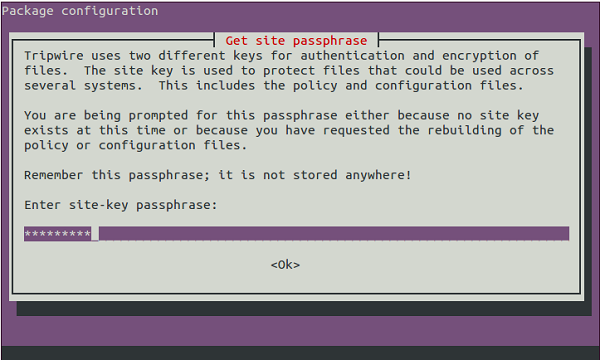
Provide your site-key passphrase and click Ok. You should see the following page:
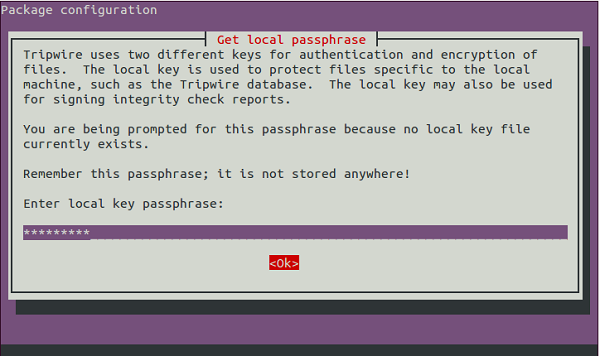
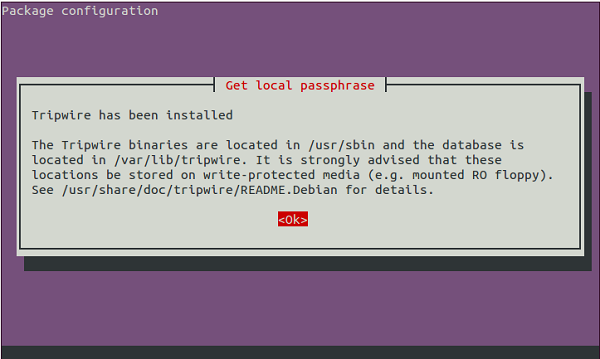
Provide your local key passphrase and click Ok. Once the installation has been completed. You should see the following page:
Before starting, you will need to initialize the Tripwire database system. You can do this by running the following command:
tripwire --initYou should see the following output:
Please enter your local passphrase:
Parsing policy file: /etc/tripwire/tw.pol
Generating the database...
*** Processing Unix File System ***
### Warning: File system error.
### Filename: /var/lib/tripwire/mail.example.com.twd
### No such file or directory
### Continuing...
### Warning: File system error.
### Filename: /etc/rc.boot
### No such file or directory
### Continuing...
### Warning: File system error.
### Filename: /root/mail
### No such file or directory
### Continuing...
### Warning: File system error.
### Filename: /root/Mail
### No such file or directory
### Continuing...
### Warning: File system error.
### Filename: /root/.xsession-errors
### No such file or directory
### Continuing...
### Warning: File system error.
### Filename: /root/.xauth
### No such file or directory
### Continuing...
### Warning: File system error.
### Filename: /root/.tcshrc
### No such file or directory
### Continuing...
### Warning: File system error.
### Filename: /root/.sawfish
### No such file or directoryIn the above output, you should get "No such directory" error. To resolve this error, you will need to edit Tripwire policy configuration file and regenerate the configuration.
First, list out all the files and directory that does not exist by running the following command:
sh -c "tripwire --check | grep Filename > list.txt"
cat list.txt You should see all the files and directories in the following output:
Filename: /etc/rc.boot
Filename: /root/mail
Filename: /root/Mail
Filename: /root/.xsession-errors
Filename: /root/.xauth
Filename: /root/.tcshrc
Filename: /root/.sawfish
Filename: /root/.pinerc
Filename: /root/.mc
Filename: /root/.gnome_private
Filename: /root/.gnome-desktop
Filename: /root/.gnome
Filename: /root/.esd_auth
Filename: /root/.elm
Filename: /root/.cshrc
Filename: /root/.bash_profile
Filename: /root/.bash_logout
Filename: /root/.amandahosts
Filename: /root/.addressbook.lu
Filename: /root/.addressbook
Filename: /root/.Xresources
Filename: /root/.Xauthority
Filename: /root/.ICEauthority
Filename: /proc/3776/fd/3
Filename: /proc/3776/fdinfo/3
Filename: /proc/3776/task/3776/fd/3
Filename: /proc/3776/task/3776/fdinfo/3Now, open the Tripwire policy configuration file twpol.txt.
nano /etc/tripwire/twpol.txtComment out the lines as shown below:
(
rulename = "Boot Scripts",
severity = $(SIG_HI)
)
{
/etc/init.d -> $(SEC_BIN) ;
#/etc/rc.boot -> $(SEC_BIN) ;
/etc/rcS.d -> $(SEC_BIN) ;
/etc/rc0.d -> $(SEC_BIN) ;
/etc/rc1.d -> $(SEC_BIN) ;
/etc/rc2.d -> $(SEC_BIN) ;
/etc/rc3.d -> $(SEC_BIN) ;
/etc/rc4.d -> $(SEC_BIN) ;
/etc/rc5.d -> $(SEC_BIN) ;
/etc/rc6.d -> $(SEC_BIN) ;
}
(
rulename = "System boot changes",
severity = $(SIG_HI)
)
{
#/var/lock -> $(SEC_CONFIG) ;
#/var/run -> $(SEC_CONFIG) ; # daemon PIDs
/var/log -> $(SEC_CONFIG) ;
}
(
rulename = "Root config files",
severity = 100
)
{
/root -> $(SEC_CRIT) ; # Catch all additions to /root
#/root/mail -> $(SEC_CONFIG) ;
#/root/Mail -> $(SEC_CONFIG) ;
#/root/.xsession-errors -> $(SEC_CONFIG) ;
#/root/.xauth -> $(SEC_CONFIG) ;
#/root/.tcshrc -> $(SEC_CONFIG) ;
#/root/.sawfish -> $(SEC_CONFIG) ;
#/root/.pinerc -> $(SEC_CONFIG) ;
#/root/.mc -> $(SEC_CONFIG) ;
#/root/.gnome_private -> $(SEC_CONFIG) ;
#/root/.gnome-desktop -> $(SEC_CONFIG) ;
#/root/.gnome -> $(SEC_CONFIG) ;
#/root/.esd_auth -> $(SEC_CONFIG) ;
#/root/.elm -> $(SEC_CONFIG) ;
#/root/.cshrc -> $(SEC_CONFIG) ;
/root/.bashrc -> $(SEC_CONFIG) ;
#/root/.bash_profile -> $(SEC_CONFIG) ;
#/root/.bash_logout -> $(SEC_CONFIG) ;
/root/.bash_history -> $(SEC_CONFIG) ;
#/root/.amandahosts -> $(SEC_CONFIG) ;
#/root/.addressbook.lu -> $(SEC_CONFIG) ;
#/root/.addressbook -> $(SEC_CONFIG) ;
#/root/.Xresources -> $(SEC_CONFIG) ;
#/root/.Xauthority -> $(SEC_CONFIG) -i ; # Changes Inode number on login
#/root/.ICEauthority -> $(SEC_CONFIG) ;
}
(
rulename = "Devices & Kernel information",
severity = $(SIG_HI),
)
{
/dev -> $(Device) ;
# /proc -> $(Device) ;
}Save and close the file, when you are finished. Then, recreate the encrypted policy file with the following command:
twadmin -m P /etc/tripwire/twpol.txtEnter your site-key passphrase and press Enter.
Now, reinitialize the Tripwire database with the following command:
tripwire --initEnter your local-key passphrase. You should see the following output:
Wrote database file: /var/lib/tripwire/mail.example.com.twd
The database was successfully generated.Now, you will need to check the integrity of system files. You can do this with the following command:
tripwire --checkYou should see the following output with no errors:
Total objects scanned: 27492
Total violations found: 0
===============================================================================
Object Summary:
===============================================================================
-------------------------------------------------------------------------------
# Section: Unix File System
-------------------------------------------------------------------------------
No violations.
===============================================================================
Error Report:
===============================================================================
No Errors
-------------------------------------------------------------------------------
*** End of report ***
Open Source Tripwire 2.4 Portions copyright 2000 Tripwire, Inc. Tripwire is a registered
trademark of Tripwire, Inc. This software comes with ABSOLUTELY NO WARRANTY;
for details use --version. This is free software which may be redistributed
or modified only under certain conditions; see COPYING for details.
All rights reserved.
Integrity check complete.Now, create some file and directory with the following command:
touch test1.txt test2.txt test3.txt
mkdir test1 test2 test3Next, check the system using Tripwire again:
tripwire --checkYou should see files and directory which you have added earlier in the following output:
Total objects scanned: 27498
Total violations found: 7
===============================================================================
Object Summary:
===============================================================================
-------------------------------------------------------------------------------
# Section: Unix File System
-------------------------------------------------------------------------------
-------------------------------------------------------------------------------
Rule Name: Root config files (/root)
Severity Level: 100
-------------------------------------------------------------------------------
Added:
"/root/test3"
"/root/test3.txt"
"/root/test1"
"/root/test2"
"/root/test2.txt"
"/root/test1.txt"
Modified:
"/root"
===============================================================================
Error Report:
===============================================================================
No Errors
-------------------------------------------------------------------------------
*** End of report ***
Open Source Tripwire 2.4 Portions copyright 2000 Tripwire, Inc. Tripwire is a registered
trademark of Tripwire, Inc. This software comes with ABSOLUTELY NO WARRANTY;
for details use --version. This is free software which may be redistributed
or modified only under certain conditions; see COPYING for details.
All rights reserved.
Integrity check complete.Next, create a new Tripwire Rule for Apache named "Apache Ruleset" with severity 'High/SIG_HI' and all files on that directory is critical cannot be changed
First, open the Tripwire policy configuration file:
nano /etc/tripwire/twpol.txtAdd the following lines:
## Ruleset for Apache ##
(
rulename = "Apache Ruleset",
severity= $(SIG_HI)
)
{
/var/www/html -> $(SEC_CRIT);
}Save and close the file, when you are finished. Then, regenerate the tripwire config file and reinitialize the Tripwire database with the following command:
twadmin -m P /etc/tripwire/twpol.txt
tripwire --initNow, try to create a new file test.html inside /var/www/html directory with the following command:
echo "<h1> Test Apache</h1>" > /var/www/html/test.htmlNext, check the system with the following command:
tripwire --checkYou should get a notification about system violations with security level 100 in the following output:
Total objects scanned: 27502
Total violations found: 2
===============================================================================
Object Summary:
===============================================================================
-------------------------------------------------------------------------------
# Section: Unix File System
-------------------------------------------------------------------------------
-------------------------------------------------------------------------------
Rule Name: Apache Ruleset (/var/www/html)
Severity Level: 100
-------------------------------------------------------------------------------
Added:
"/var/www/html/test.html"
Modified:
"/var/www/html"
===============================================================================
Error Report:
===============================================================================
No Errors
-------------------------------------------------------------------------------
*** End of report ***
Open Source Tripwire 2.4 Portions copyright 2000 Tripwire, Inc. Tripwire is a registered
trademark of Tripwire, Inc. This software comes with ABSOLUTELY NO WARRANTY;
for details use --version. This is free software which may be redistributed
or modified only under certain conditions; see COPYING for details.
All rights reserved.
Integrity check complete.By default, Tripwire provides a function 'emailto' in the configuration file to notify you through the mail. Before starting, test E-mail notification using the following command:
tripwire --test --email root@localhostNow, check your mail with the following command:
tail -f /var/mail/rootYou should see the following output:
From: "Open Source Tripwire(R) 2.4.2.2.2" <tripwire@mail.example.com>
To: root@localhost
Subject: Test email message from Tripwire
Content-Type: text/plain
Content-Transfer-Encoding: 7bit
Message-Id: <E1fyc6G-0000Uq-3Q@mail.example.com>If you receive this message, email notification from tripwire. That means it is working correctly.
Next, you will need to configure Tripwire to send E-mail notification for Apache. You can do this by editing /etc/tripwire/twpol.txt file:
nano /etc/tripwire/twpol.txtMake the following changes:
### Ruleset for Apache ###
(
rulename = "Apache Ruleset",
severity= $(SIG_HI),
emailto = root@localhost
)
{
/var/www/html -> $(SEC_CRIT);
}Save the file. Then, regenerate the configuration and reinitialize the Tripwire database with the following command:
twadmin -m P /etc/tripwire/twpol.txt
tripwire --initNext, create some new file inside /var/www/html directory again and check the system manually using Tripwire and send the report over email.
tripwire --check --email-reportNow, check your mail using the following command:
tail -f /var/mail/rootYou should see the following output:
Rule Name: Apache Ruleset (/var/www/html)
Severity Level: 100
-------------------------------------------------------------------------------
Added:
"/var/www/html/2"
"/var/www/html/3"
"/var/www/html/1"
Modified:
"/var/www/html"
===============================================================================
Error Report:
===============================================================================
No Errors
-------------------------------------------------------------------------------
*** End of report ***
Open Source Tripwire 2.4 Portions copyright 2000 Tripwire, Inc. Tripwire is a registered
trademark of Tripwire, Inc. This software comes with ABSOLUTELY NO WARRANTY;
for details use --version. This is free software which may be redistributed
or modified only under certain conditions; see COPYING for details.
All rights reserved.
Integrity check complete.Next, you can also configure cron that check your system every day and send a notification for an Apache rule violation to your email.
You can do this by editing /etc/crontab file:
nano /etc/crontabAdd the following line:
0 0 * * * tripwire --check --email-reportSave and close the file, then restart cron to apply the changes:
systemctl restart cronNow, you will get notifications by e-mail every day.
How to Create an SSL VPN server on Alibaba Cloud in 15 Minutes
How to Connect Tableau to MaxCompute Using HiveServer2 Proxy

2,593 posts | 794 followers
FollowAlibaba Clouder - June 13, 2019
Alibaba Clouder - June 13, 2019
Alibaba Clouder - June 25, 2018
Alibaba Clouder - June 13, 2019
Alibaba Clouder - June 13, 2019
Alibaba Clouder - August 2, 2019

2,593 posts | 794 followers
Follow ECS(Elastic Compute Service)
ECS(Elastic Compute Service)
Elastic and secure virtual cloud servers to cater all your cloud hosting needs.
Learn More Simple Log Service
Simple Log Service
An all-in-one service for log-type data
Learn More Marketplace
Marketplace
Marketplace is an online market for users to search and quickly use the software as image for Alibaba Cloud products.
Learn MoreMore Posts by Alibaba Clouder