In this post, we will walk through the use of two major cloud security services: Alibaba Cloud’s Anti-DDoS tool and AWS Shield.

To maintain a secure web application, you need to invest in security tools. But because there are so many security tools available, it can be difficult to decide which one to choose. Most cloud platforms offer security services to help protect workloads, and you may not know which one is the best fit for your needs.
In this post, we will walk through the use of two major cloud security services: Alibaba Cloud’s Anti-DDoS tool and AWS Shield. Both solutions offer protection against denial-of-service attacks on cloud workloads. Below, we’ll take a look at how each service is set up, with the goal of determining which is a better fit for a given workload or use case.
Alibaba Cloud Anti-DDoS
As its name implies, Alibaba Cloud Anti-DDoS is a tool that protects web applications against DDoS attacks that aim to overload server bandwidth or overload resources until they run out, and the server stops responding.
Alibaba Cloud Anti-DDoS is available in two tiers: a Basic version and a Pro one. The following table shows how the two offerings compare feature-wise:
|
Anti-DDos Basic |
Anti-DDos Pro |
| SYN | SYN flood |
| Flood | UDP flood |
| UDP Flood | ACK flood |
| ICMP Flood | ICMP flood |
| fragments | DNS query flood |
| malformed packets | NTP reply flood |
| | HTTP flood attack |
| | Web application attacks |
| | Protection layer 4 and 7 |
As you can see,
Anti-DDoS Pro has a wider range of options for attack protection that will guarantee greater security for your web application. It also protects the application and server from the most common attacks, along with the most complex ones. With the Pro version, the mitigation capacity goes from 5 Gbps, which is the capacity defended by Basic, to 2 Tbps.
Tool test
By default, Anti-DDoS is automatically enabled when you create an instance. However, at some point, some parameters will have to be changed so that it responds according to your needs.
In the test that I performed, an ECS was created, and I will demonstrate the functioning of the Anti-DDoS service with the available instance.
On the main dashboard, you’ll find the option for Anti-DDoS in the Security menu:
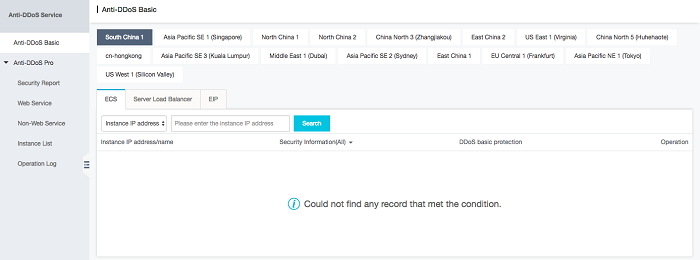
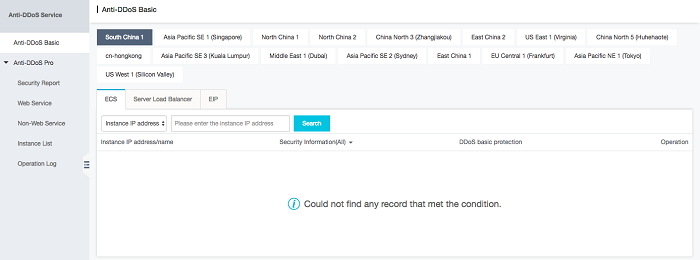
The first impression is that it is not working; however, the service will be available in the region the instance was created in. In my case, it was created in Asia Pacific SE 1 (Singapore). Note that this dashboard shows the South China 1 region preselected, so you may need to modify where the instance is.
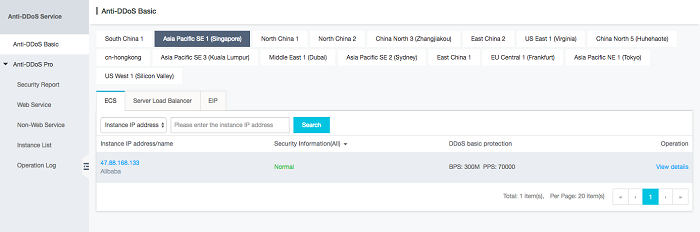
After selecting where the instance is, you can see that there is already a level of security in the Basic model for the ECS created.
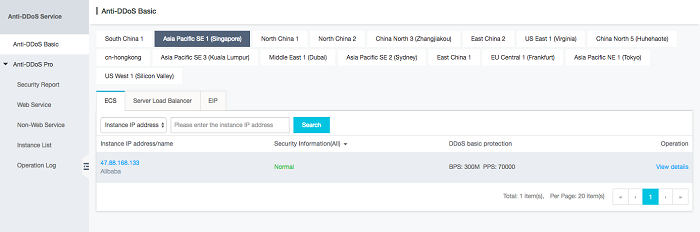
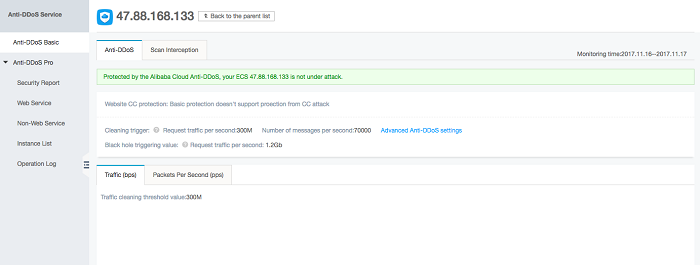
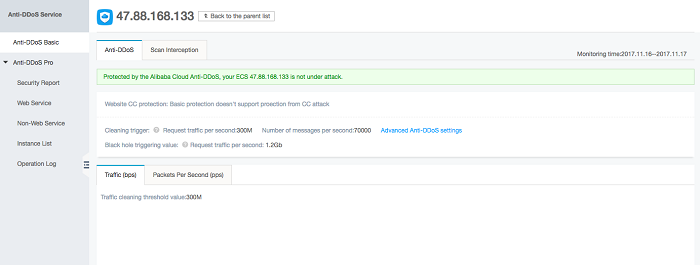
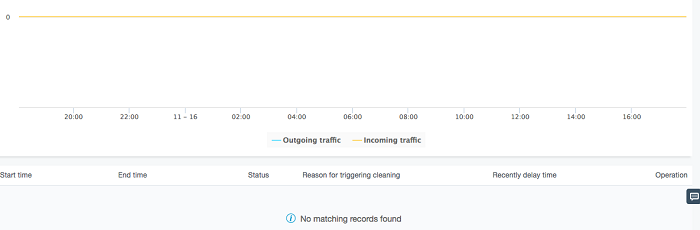
We can see that the instance has not suffered an attack. We can still see two monitoring tabs, one labeled Traffic (bps) and the other Packets Per Second (pps). In this same screen, we can see that the Basic plan does not support CC attacks, so you should evaluate whether the Basic option is best for you.
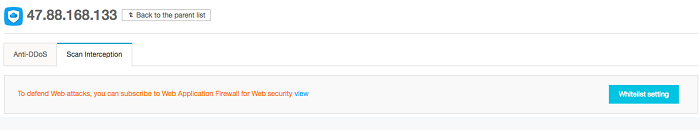
Through the following screenshots, I will show the contents of the View Details option.
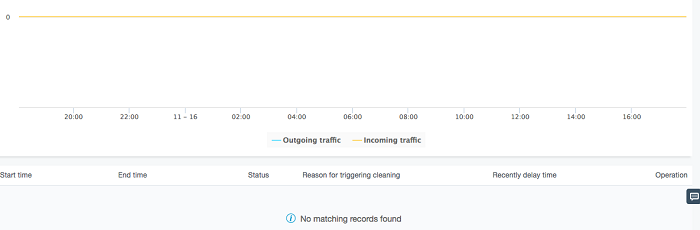
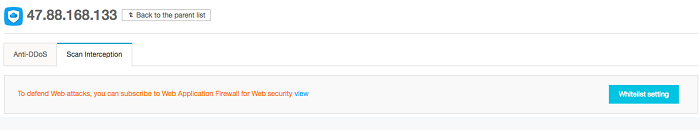
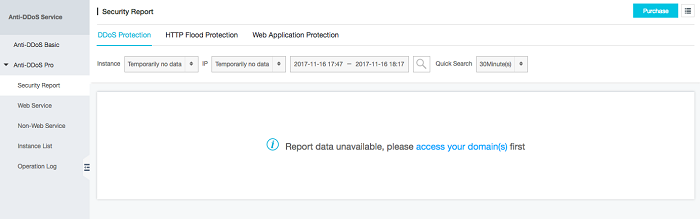
The Whitelist setting button is for feeding a list of allowed addresses if you have enabled and configured the WAF. Below are some Anti-DDoS settings, starting with the report.
Security report
In any of the options you select, the data filter options will be the same. It is easy to generate daily, weekly, and monthly reports.
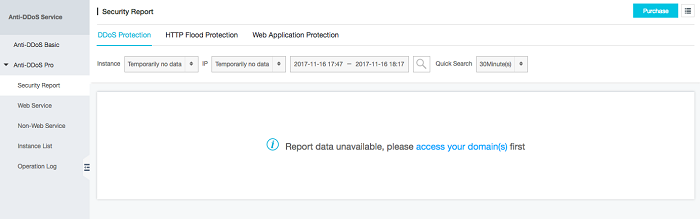
The web protection configuration can be visualized fully in the official documentation, which is available
here.
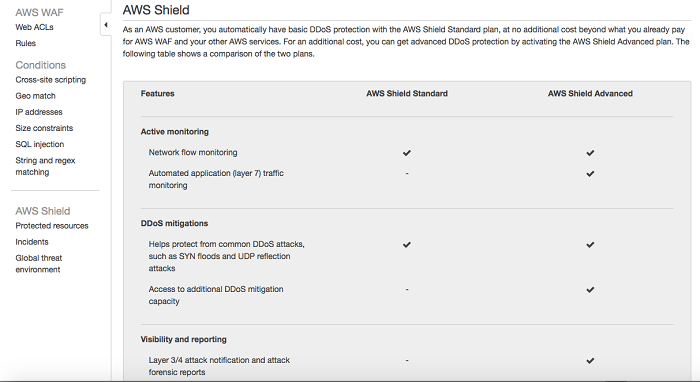
AWS Shield
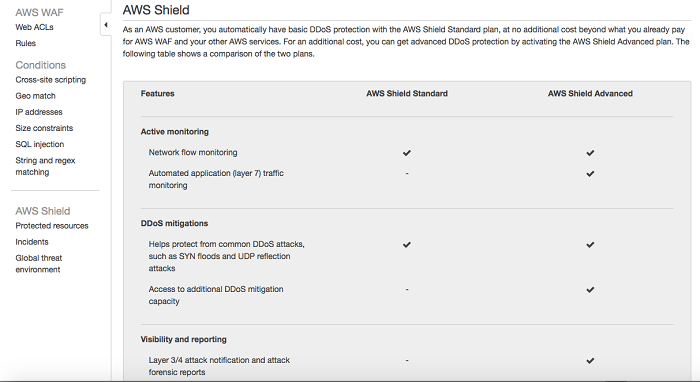
Amazon offers its own service against DDoS attacks—AWS Shield. Like Anti-DDoS, it also has two levels of protection: Standard and Advanced. Standard protects by default all applications configured on Amazon, and common attacks on the network and transport layers. At the Advanced level, you get more protection and the option of customizing defense rules, just as with Anti-DDoS.
A general comparison of the two levels of protection is shown in the table below:
Comparison of Alibaba Cloud Anti-DDoS and AWS Shield Features
| Feature | AWS Shield Standard | AWS Shield Advanced | Anti-DDoS Basic | Anti-DDoS Pro |
| Traffic monitoring |
| Network flow monitoring | Yes | Yes | Yes | Yes |
| Automatic always-on detection | Yes | Yes | Yes | Yes |
| Application traffic monitoring | No | Yes | Yes | Yes |
| Attack mitigation |
| Protection from common DDoS attacks (e.g. SYN floods, ACK floods, UDP floods, Reflection attacks) | Yes | Yes | Yes | Yes |
| SYN flood | Yes | Yes | Yes | Yes |
| UDP Flood | Yes | Yes | Yes | Yes |
| ICMP Flood | Yes | Yes | Yes | Yes |
| fragments | Yes | Yes | Yes | Yes |
| malformed packets | Yes | Yes | Yes | Yes |
| HTTP flood attack | No | Yes | No | Yes |
| Web application attacks | No | Yes | No | Yes |
| Protection layer 4 | No | Yes | No | Yes |
| Protection layer 7 | No | Yes | No | Yes |
Tool test
After logging into the AWS console, we need to locate the AWS Shield service.
Choose the service you want to access and configure. I clicked Go to AWS Shield.
To my surprise, I was directed to a different screen that contained the WAF settings.
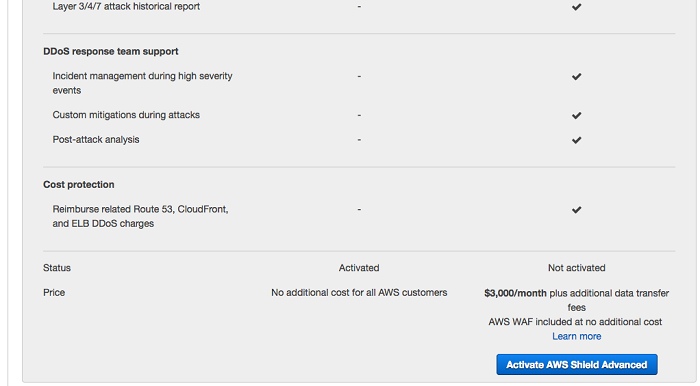
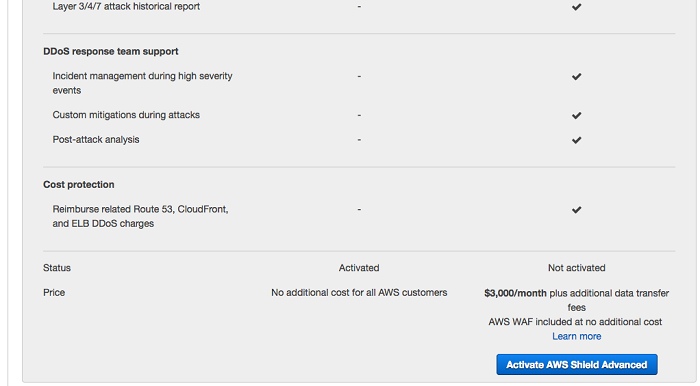
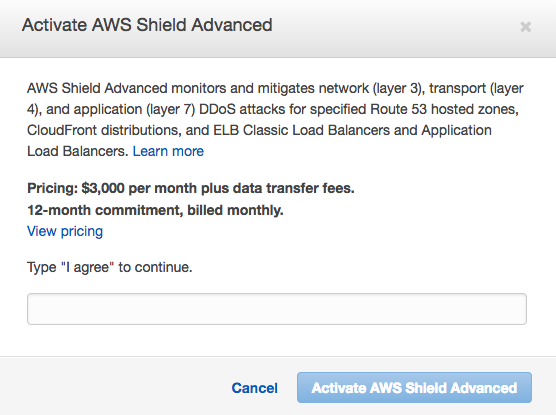
When I clicked on any icon in AWS Shield, page blocking wasn’t an option, forcing me to activate Advanced to proceed, which costs $ 3,000 per month just for the activation.
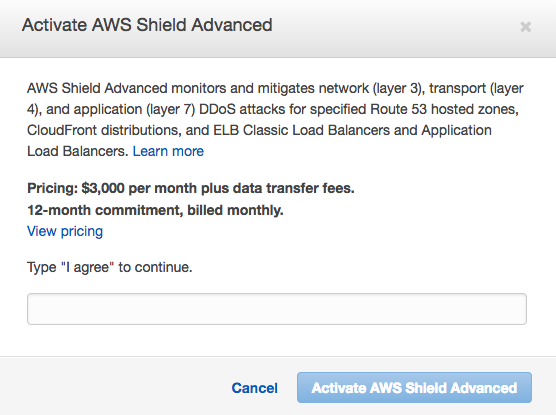
Unfortunately, my test of AWS Shield ends here because enabling activation just to test the tool is so costly. But, unlike AWS Shield, Alibaba Cloud offers a $300 credit to test the tool as much as you like, and you can simulate an environment that closely matches your requirements.
Conclusion
As we can see, both tools are similar, differentiating on the data capacity that will be served, depending on the level of protection desired. High availability at 99.99%, automatic mitigation, and 24/7 support are offered by both. However, one difference that stands out is
Alibaba Cloud’s Anti-DDoS built-in for application monitoring. AWS provides monitoring through other services. To me, it’s an advantage to have monitoring features built-in so that I do not have to seek out and use multiple tools. This makes Alibaba Cloud Anti-DDoS attractive if you are seeking a “single pane of glass” with which to manage cloud application security.
Bio

Brena Monteiro is a Fixate IO Contributor and a software engineer with experience in the analysis and development of systems. She is a free software enthusiast and an apprentice of new technologies.




 Anti-DDoS
Anti-DDoS