By Yong Chen
The exploitation of software vulnerabilities is one of the initial steps of a cyber-attack. In engineering schools, they teach you that fixing a defect in the implementation stage is 6.5 times higher than fixing it in the design stage1. Applying this principle to ‘cybersecurity school', we can say that blocking an attack at the vulnerability stage is a dozen times cheaper than stopping it after a device is compromised by an exploit.
In this blog post we present an analysis of a recently detected vulnerability in the ThinkPHP framework, which exposed 10% of all websites using it to remote takeover. The post provides a detailed explanation of an actual code used by an attacker in an attempt to exploit this vulnerability, as well as precise recommendations of how to protect against it (hint: apply the official fix! otherwise, get help from Alibaba Cloud's Threat Detection Service).
Yohai Einav
Principal Security Researcher, SIL
ThinkPHP is a popular PHP Object-Oriented MVC framework used by many e-commerce, financial and online gaming website. The framework provides support for UTF-8, plugins, role-based-control-access (RBCA), a template control engine and multi-databases. A recent vulnerability in ThinkPHP v5, which was detected by Alibaba Cloud, allowed attackers to remotely execute commands on systems running the framework, and inflict extensive damage.
While an official fix for this critical vulnerability was released on December 10th, 2018, Alibaba Cloud Threat Detection Service (TDS), formerly known as Situational Awareness Service (SAS), has still detected multiple attacks exploiting the vulnerability after the fix. In order to ensure that even users that do not update their systems in a timely manner in the cloud are protected from the vulnerability, Alibaba Cloud TDS offers an Attack Alarm service, which uses its web application firewall (WAF) to synchronously block the vulnerability, and protect all customers from it.
The following provides a comprehensive analysis of the vulnerability's context, logic and behavior, along with a real-life case analysis.
The ThinkPHP v5 framework lacks sufficient security checking of controller names, which allows the attacker to construct a specific request where routing enforcement is disabled. This means that the attacker can run code remotely and gain server permissions.
ThinkPHP v5.0 versions earlier than 5.0.23
ThinkPHP v5.1 versions earlier than 5.1.31
With a comparison to the official fix instruction released by ThinkPHP, we analyzed the code under /thinkphp/library/think/Route.php where ThinkPHP schedules for route parsing.
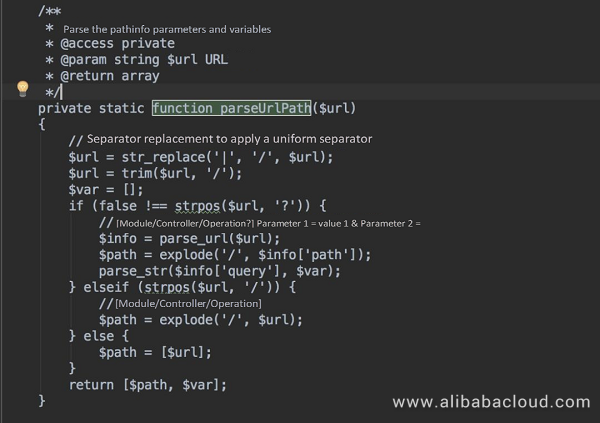
The "parseUrlPath" function calls the path function and parses the routing information in "pathinfo". The URL in the function is divided by slashes (/) without applying any filter.
After searching for "pathinfo", we find that //thinkphp/library/think/Request.php defines the "pathinfo" function which gets the URL.
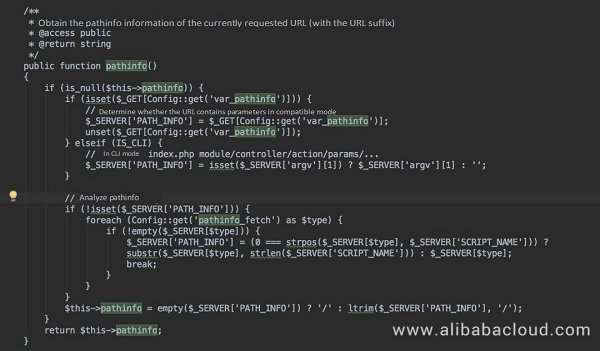
An attacker can exploit the value of "$_GET" for command injection: the parameter of "var_pathinfo" is "s", where the function for command injection can be created.
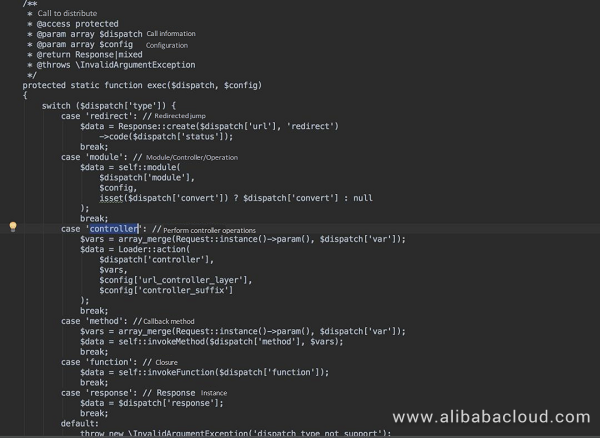
We also analyzed the app.php code for route scheduling, which operates the controller through the "controller" variable, instantiates the controller, and tracks the controller method.
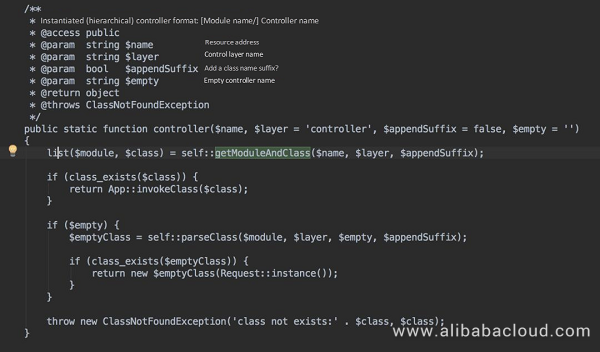
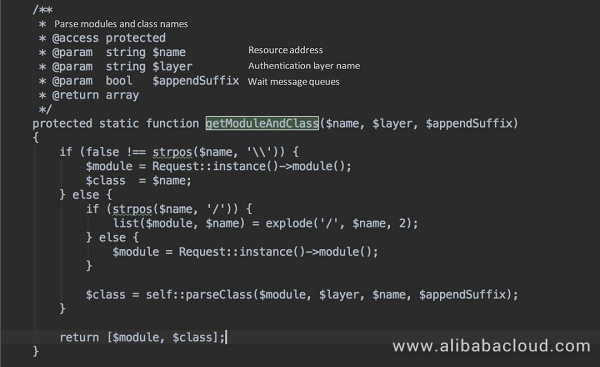
In //thinkphp/library/think/Loader.php, the controller calls "parseModuleAndClass" to parse "$name" and instantiate "$class". When "$name" matches with a backslash (\), it is used as a method and class in "strpos($name, '\')". An attacker can construct and instantiate any method to be called, and instantiate the "namespaceclass" class to execute the "call_user_func_array" method.
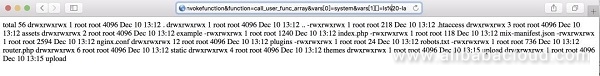
We reproduced the effect in ThinkPHP v5.0.22 which also contains the remote code execution vulnerability. The following figure shows that we can run the "ls" command on a vulnerability-infected host to obtain details of all files in the directory:
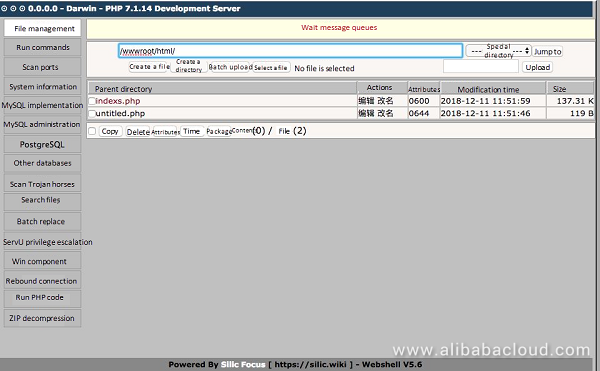
As of December 11, 2018, Alibaba Cloud Threat Detection Service (TDS) found that the vulnerability has been exploited in many ways, mostly in the form of web-shells, "a script that can be uploaded to a web server to enable remote administration of the machine" (https://www.us-cert.gov/ncas/alerts/TA15-314A).
The following is a summary of all existing web shell methods and single out the following popular methods:
Example:
The following screenshot shows the functions list of this webshell:
Example:
The following screenshot shows the functions of the webshell:

Example:
Our analysis found that about 10% of all websites using ThinkPHP worldwide were exposed to this vulnerability. Alibaba Cloud TDS saw a sharp increase in the number of attacked websites from December 4, 2018 to December 11, 2018.
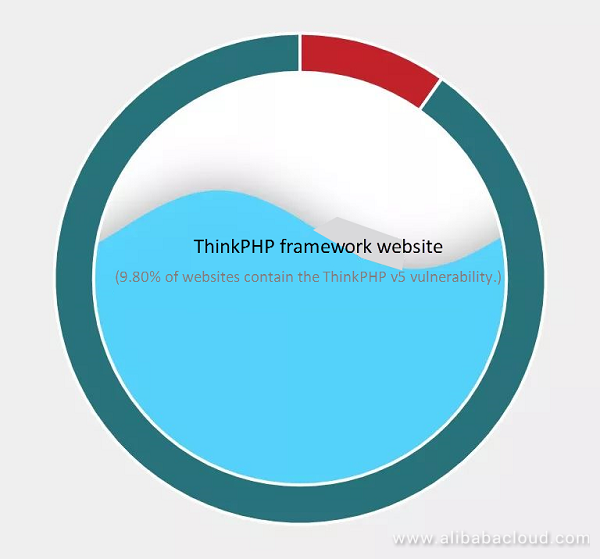
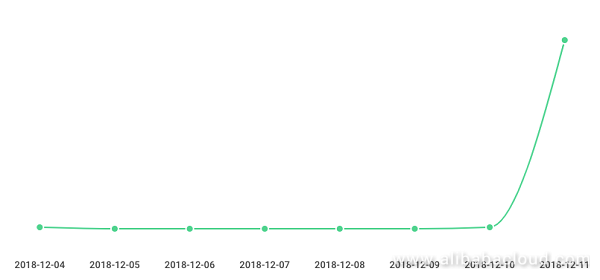
The graph above shows the sharp increase in the number of attacked websites, indicating that the vulnerability is automatically exploited at a large scale soon after being exposed.
Based on the team's previous experience with exploitation of vulnerabilities, we believe that this vulnerability may be exploited in a variety of additional ways. It is therefore recommended that all enterprises upgrade their ThinkPHP framework to the latest version as soon as possible to protect their websites against attacks and prevent their servers being compromised.
Alibaba Cloud security experts remind you that ThinkPHP v5.0.23 and v5.1.31 are secure versions, and recommend to upgrade your ThinkPHP framework to the latest version as soon as possible to fix the vulnerability. If you have not promptly upgraded your ThinkPHP framework, please subscribe to Alibaba Cloud Threat Detection Service (TDS) and Web Application Firewall (WAF) to defend against attacks in a timely manner.
For more information about this vulnerability, see https://blog.thinkphp.cn/869075.
New Vulnerability Found in the Decade-Old phpCMS 2008 Can Lead to Fresh WebShell Attacks
Alibaba Cloud Offers a Security Emergency Response Plan for Global Bank Websites Targeted by Hackers

32 posts | 15 followers
FollowAlibaba Cloud Security - January 13, 2019
Alibaba Clouder - September 16, 2020
Alibaba Clouder - July 10, 2020
Alibaba Cloud Security - July 31, 2018
Data Geek - September 3, 2024
Alibaba Cloud Security - November 6, 2019

32 posts | 15 followers
Follow Backup and Archive Solution
Backup and Archive Solution
Alibaba Cloud provides products and services to help you properly plan and execute data backup, massive data archiving, and storage-level disaster recovery.
Learn More Drive and Photo Service
Drive and Photo Service
A low-code, high-availability, and secure platform for enterprise file management and application
Learn More Architecture and Structure Design
Architecture and Structure Design
Customized infrastructure to ensure high availability, scalability and high-performance
Learn More Sensitive Data Discovery and Protection
Sensitive Data Discovery and Protection
SDDP automatically discovers sensitive data in a large amount of user-authorized data, and detects, records, and analyzes sensitive data consumption activities.
Learn MoreMore Posts by Alibaba Cloud Security
5697346405925554 January 2, 2019 at 5:14 am
Informative!Upgrade your shipping plans to digitally with ecourierz - best, cheapest and fastest courier service in India. For more details visit www.ecourierz.com